![]()
Before coming to the Azure Firewall, One question! What do you understand by the word Firewall?
In everyday language, a firewall is a physical barrier designed to block fire from spreading. In the digital world, a firewall offers a similar protective measure, but it guards against unwanted network traffic and cyber threats. By setting up a firewall, you ensure that only trusted sources and data can enter your network, keeping your digital environment secure while you browse the internet.
In this blog, you will see a brief introduction about Azure Firewall, so let’s get started.
The Topics covered in this blog are:
- Overview of Azure Firewall
- Concepts of Azure Firewall
- Features of Azure Firewall
- Pricing and SLA of Azure Firewall
- Conclusion
- FAQ’s
Overview of Azure Firewall
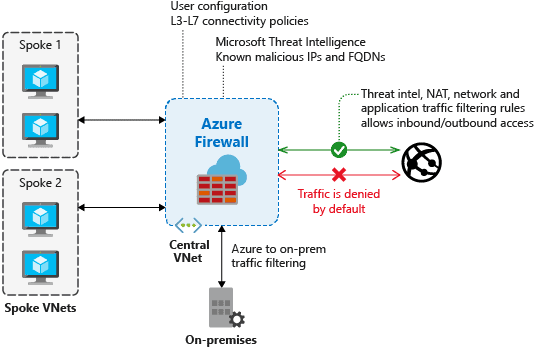
Azure Firewall is a controlled security utility that defends your Azure Virtual Network resources. It comes with high availability and unlimited cloud scalability, Which means that you don’t have to deploy additional infrastructure for high availability like two firewalls or three firewalls and also no need for the load balancer. An important point to note here is that by default Azure Firewall blocks all the traffic.
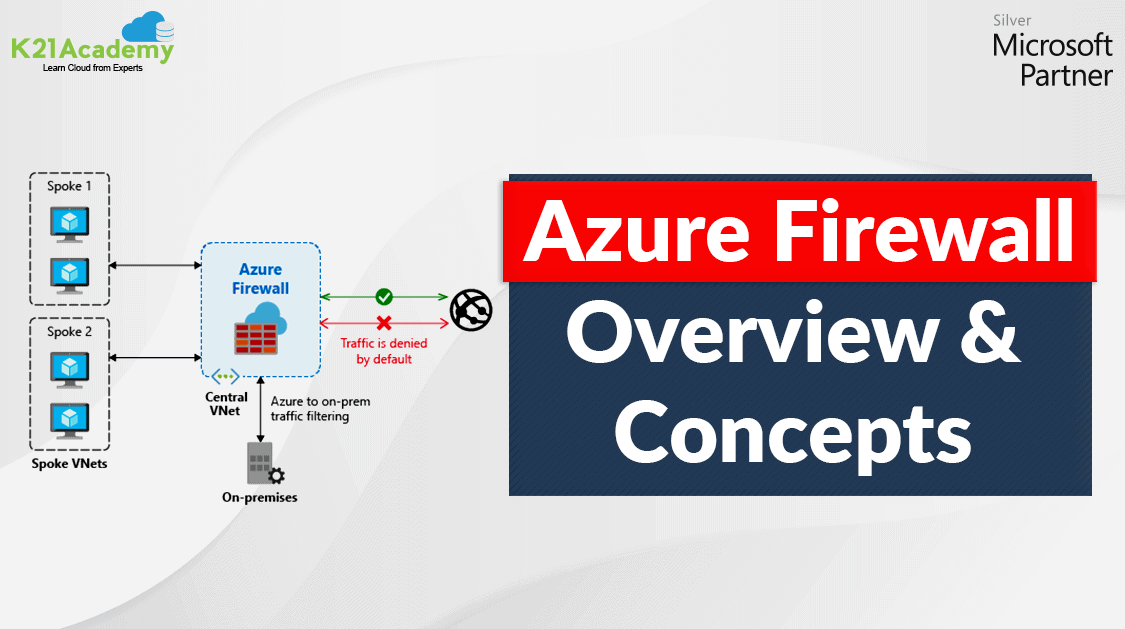
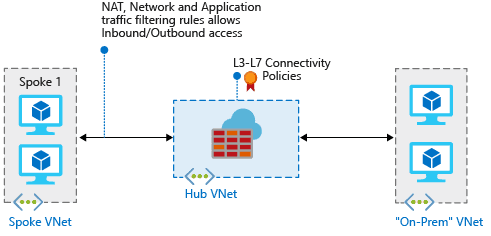
You can deploy a Firewall on each virtual network. But usually, users will use it on a central virtual network and compare it to other virtual networks on the hub and speaker models. You can then set the default route from the peered virtual networks to purpose to the present central firewall virtual network. Global VNet peering is supported, however, it is not suggested attributable to potential performance and latency problems across regions. For most reliable production, deploy one firewall per region.
This model’s advantage is that the ability to centrally exert management on multiple spoke VNETs across totally different subscriptions. There are price savings as you do not have to be compelled to deploy a firewall in every VNet separately. savings ought to be measured versus the associate peering cost supported by the client traffic patterns.
Also Check: Our blog post on Azure Secure Score.
Concepts of Azure Firewall
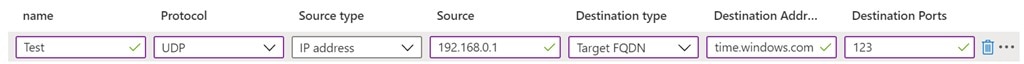
Controlling outbound network access is an essential part of the overall network security plan. For example, you may want to limit access to a website, or you may wish to restrict outbound IP addresses or ports. With a firewall, you can configure applications rules that define fully qualified Domain names that can be accessed from a subnet. Also, you can configure network rules so that you can define source address, protocol destination, and destination addresses.
In Azure Firewall Network rule collections are a higher preference than application rule collections.
There are three types of rule collections:
- Application rules: Configure Fully qualified domain names (FQDNs) that can be reached from a subnet.
- Network Rule Collections: Takes precedence over application rules, focusing on source addresses, protocols, destination ports, and destination addresses.
- NAT rules: Configures DNAT for incoming internet connections, directing them to appropriate internal resources.
Note: FDQN Tags: Represents a group of fully qualified domain names associated with well-known Microsoft services.
Check Out: Our blog post on AZ 500 Exam Prep.
Features of Azure Firewall
Azure Firewall includes the following features:
- Built-in high availability
- Availability Zones
- Unrestricted cloud scalability
- Application FQDN filtering rules
- Network traffic filtering rules
- FQDN tags
- Service tags
- Threat intelligence
- Outbound SNAT support
- Inbound DNAT support
- Multiple public IP addresses
- Azure Monitor logging
- Forced tunneling
- Web categories
- Certifications
Some of the significant features of the Azure Firewall which plays a key role while configuring are:
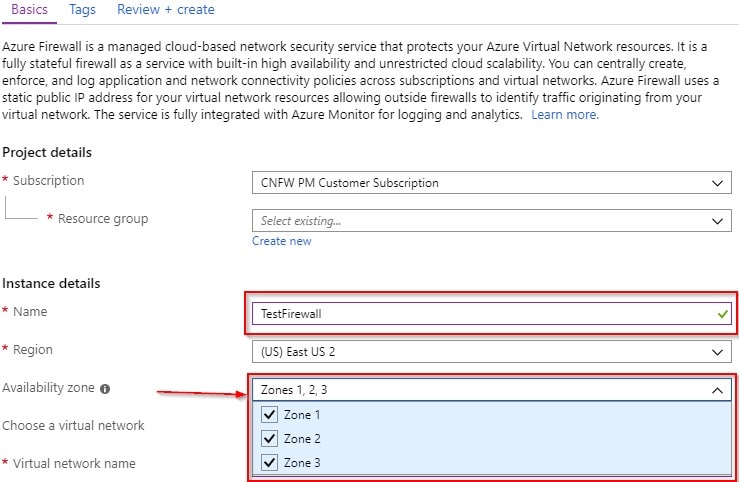
1. Built-in high availability & Availability Zones
We have built-in High Availability. It can be configured at the time of deployment for multiple Availability Zones, to increases availability uptime to 99.99%. When two or more Availability Zones are selected uptime SLA is offered is 99.99%. You can deploy a Firewall in an Availability Zone has no additional cost, but there is the cost for outbound and inbound traffic data transfer associated with Availability Zones.
So no extra cost for deploying in multiple availability zones.
2. Unrestricted cloud scalability with Threat intelligence
You can scale up Azure Firewall as many as you need to accommodate increasing network traffic flows, so you don’t need to schedule for your peak traffic.
You can alert and deny traffic from/to known malicious IP addresses and domains, it can be enabled for your firewall using Threat intelligence-based filtering. Microsoft Threat Intelligence feed is sourced for malicious IP addresses and domains.
3. Service tags
It helps reduce complexity for security rule creation by designates a group of IP address prefixes. Microsoft manages the address prefixes embraced by the service tag and automatically updates the service tag as addresses change, because you can’t create your own service tag, nor specify which IP addresses are inserted within a tag.
4. Application FQDN filtering rules & FQDN Tags
We can filter our outbound traffic such as HTTP/S or Azure SQL traffic to a defined list of fully qualified domain names (FQDN) including wild cards, and this feature doesn’t need any TLS termination.
FQDN Tags permits well-known Azure service network traffic within your firewall. If you want to allow Windows Update network traffic into your Azure firewall. You can do it by building an application rule and enter the Windows Update tag, which allows network traffic from Windows Update can flow within your firewall.
5. Outbound SNAT & Inbound DNAT support
Azure Firewall public IP (Source Network Address Translation) has all translate outbound virtual network traffic IP addresses. Firewall SNAT doesn’t support when the destination IP is a private IP range. we can distinguish and allow traffic beginning from your virtual network to remote Internet destinations. Destination Network Address Translation (DNAT) translated and filtered inbound internet network traffic from your firewall public IP address to the private IP addresses on your virtual networks.
6. Multiple public IP addresses
You can link various public IP addresses (up to 250) with your firewall.
This enables the following scenarios:
- DNAT – You can translate multiplied standard port instances over your backend servers. For example, if you have a couple of public IP addresses, you can translate TCP port 3389 (RDP) for both IP addresses.
- SNAT –More ports are active for outbound SNAT connections, reducing the potential for SNAT port exhaustion. At this point, the Azure Firewall randomly chooses the origin public IP address to utilize for connection. If you hold any downstream filtering on your network, you need to allow all public IP addresses linked with your Azure firewall. Consider using the public IP address prefix to clarifies this configuration.
Check Out: Our blog post on AZ 500.
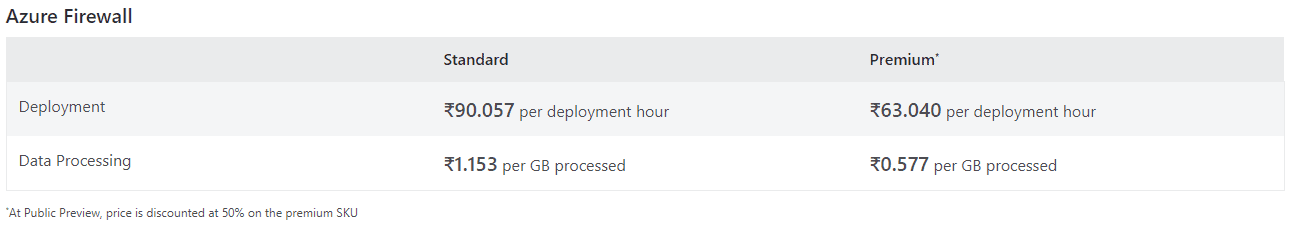
Pricing and SLA of Azure Firewall
Azure Firewall is a controlled cloud-established network security service that shields your Azure Virtual Network resources. It can be seamlessly expanded, requires zero maintenance, and is highly available with unlimited cloud scalability. Setting up a Firewall is easy with billing involved of a fixed and variable fee.
Azure Firewall provides fully stateful necessary firewall capabilities for Virtual Network resources, with built-in high availability and the ability to scale automatically. Microsoft assures you that it will be available at least 99.95% of that time when deployed inside a single Availability Zone and the Firewall will be available at least 99.99% of the time when spread within two or more Availability Zones in the corresponding Azure region.
Conclusion
Before wrapping up, it’s important to distinguish between Azure Firewall and Network Security Groups (NSGs). While both enhance security, NSGs are more focused on direct traffic management within subnets, whereas Azure Firewall provides broader protection against external threats. Azure Firewall is particularly well-suited for public-facing applications, where security and scalability are paramount.
FAQs
1. What is the difference between Azure firewall and WAF?
Ans: Both are security services for your Azure resources, but they target different threats. Azure Firewall acts like a general bouncer, inspecting all traffic entering and leaving your virtual network to block unauthorized access. WAF is a specialist focused on web applications, shielding them from common hacking techniques and vulnerabilities that could steal data or disrupt functionality
2. Is firewall free in Azure?
Ans: It itself isn't free, but there are some nuances. You'll be charged a fixed hourly rate for the deployment and a variable fee based on the amount of data processed. The management tool, Azure Firewall Manager, on the other hand, is completely free to use. There are just charges for the firewall policies and deployments you create through it
3. What are the different types of Azure firewalls?
Ans: Azure Firewall comes in three pricing tiers: Standard, Premium, and Basic. Standard offers the most features, including Layer 3-7 filtering, threat intelligence, and web filtering. Premium adds on TLS inspection and intrusion detection for advanced threat protection. Basic is a stripped-down version with just firewall rules and port filtering, suitable for simple scenarios.
4. What is the difference between Application Gateway firewall and Azure firewall?
Ans: Azure Firewall is a general network security service that inspects and filters all incoming and outgoing traffic across your virtual network. It can handle non-web traffic (like RDP and SSH) and outbound traffic for all applications. In contrast, the Web Application Firewall (WAF) built into Application Gateway is specifically designed to secure web applications (like HTTP/S traffic) from common attacks
References/Related
- Microsoft Azure Secure Network Connectivity: Firewall, DDOS, & NSG
- Microsoft Azure Security Technologies: Step By Step Activity Guides
- Microsoft Azure Security Technologies Certification
- Top 10 best practices for Azure Security in 2021
- Azure Firewall vs Azure Network Security Groups (NSG)
Next Task For You
Begin your journey toward Mastering Azure Cloud and landing high-paying jobs. Just click on the register now button on the below image to register for a Free Class on Mastering Azure Cloud: How to Build In-Demand Skills and Land High-Paying Jobs. This class will help you understand better, so you can choose the right career path and get a higher paying job.







![AWS DevOps [DOP-C02] Professional Step By Step Activity Guides (Hands-On Labs)](https://k21academy.com/wp-content/uploads/2023/02/DOP-C02-1.png)