This blog has listed the Top 10 Best Practices for Azure Security to make your Azure strong and secure. Here is the list of below mentioned topics that are covered in this blog.
Why Azure Security?
Azure is one of the best and leading cloud computing service providers in the market. In Azure, various services run together like storage, databases, network, and many others. An organization stores and access confidential information multiple times daily. A business can not let someone attack their systems, take all the controls, and leak confidential information. Azure provides endless services to make your network strong and secure. It will automatically alert you in case of some serious trouble, but there are some things that you can do to ensure double security in Azure.
Learn more about Azure Security
What is Azure Security Center?
Azure Security Center (ASC) empowers you to safeguard your Azure environment. Gain centralized security management, proactive threat detection, and simplified compliance – all in one place.
- Unified Security Management: Monitor VMs, networks, storage, and more – all from a single pane of glass.
- Proactive Threat Detection: Identify vulnerabilities and remediate risks before they become breaches.
- Compliance Made Easy: Simplify meeting security standards like SOC 2 and PCI DSS.
- Empower Your Security Team: Focus on what matters with prioritized alerts and actionable insights.
- Simplify Cloud Security: ASC automates tasks and streamlines best practices, freeing up IT resources.
How Azure Security Works
Securing your Azure cloud is a collaborative effort. Microsoft handles core infrastructure security, but some responsibilities shift based on your chosen service model (IaaS, PaaS, SaaS).
- IaaS (Focus on Customer Data): Azure secures the physical foundation (data centers, networks), while you manage data security and access controls.
- PaaS (Balanced Approach): Azure handles underlying infrastructure and platform security, while you secure your applications and data within the platform.
- SaaS (Reduced Customer Burden): Azure takes on most security tasks, including infrastructure, platform, application, and data security.
Best Practices for Azure Security
One can ensure more strong Azure security with the below points but can not rely completely on them. Below are the best practice points that I feel will be beneficial for you to make your Azure much secure and strong.
1) Manage Your Workstations
Daily a person needs to access multiple websites over the Internet. Suppose you are accessing some confidential information. At the same time, you are accessing some unknown file from the open internet containing some malware. How will it impact your business? You might be an easy target for hackers to inject malware and get access to confidential data. The only solution is to use dedicated workstations for sensitive and normal daily tasks.
For the same reason, Microsoft provides Privileges Access Workstations (PAW) in Azure that protects from all the possible security threats. An organization can use this workstation to manage confidential data and the administration of Azure.
2) Use Multiple Authentication
It’s always a security concern to strengthen the authentication process to restrict hackers from trying any phishing or brute force attacks. There is no way to make your system completely secure, but you can make it much stronger. Some basic things like complex passwords and Multi-Factor Authentication help make your simple authentication process strong and secure. Azure gives you the flexibility to use their directory service called Azure Active Directory to safeguard your authentication. The user with Azure Active Directory admin access should also enable Multi-Factor Authentication too.
3) Secure Administrator Access
Accounts with all access are highly prone to risks. You should frequently check accounts with administrative privileges at regular intervals. You should block all unnecessary access to these accounts. Privileged Identity Management is an Azure Active Directory service to manage, analyze and control access in your organization. Using this, users have to follow an activation process that will grant administrator rights for a limited time.
4) Microsoft Azure Security Center
If you are not aware of the best practices, then Azure Security Center is the best choice. Although it will charge you some additional cost to get the service onboard and maintain, it will be perfect for you if you don’t want to compromise security. It will benefit you in various terms like real-time threat protection, continuous CVE scanning, Microsoft Defender ATP licensing, and Azure CIS compliance benchmarking. It will help you to monitor and analyze network configuration and virtual appliances. In simple words, Azure Security Center is a one-stop solution that gives you all the recommendations and suggestions to make your Azure strong and secure.
Key Benefits of Azure Security Center
- Control traffic by configuring Azure Network Security Groups
- Protect Web Applications from threats by provisioning Web Application Firewalls (WAF).
- Identify and remove malware by providing Anti-Malware software
- Fix operating system configurations
5) Secure Networking
Systems and resources that are accessed directly through the internet are more prone to security threats. So it is important to ensure the security of these resources that can lead to threats to other resources. The RDP port is accessible to the public internet for Windows virtual machines, and for Linux, the SSH port is open. All the open ports must be properly restricted and locked to reduce unauthorized access. By default, you should always block ports 22, 3389, 5985, 5986, and 445, as these are the most common ports that lead to attacks.
In Azure, Network Security Group (NSG) is utilized to restrict access from all networks except some needed access points. Also, enable firewalls wherever possible. For example, the SQL Server Firewall mechanism will work outside your NSG to restrict your Microsoft SQL Server access. In case of accidental NSG misconfiguration, the firewalls will save your day. To save your network through various threats, regular vulnerability scans to your Azure infrastructure are a must.
See More on Azure Networking
6) Monitor Activity Log Alerts
Activity logs are crucial in finding any threats that occurred in the system. Any unrecognized event can lead to severe issues, so it is better to identify those beforehand. Create some activity log alerts in your system that will notify you of security threats. Here are a few cases that are crucial for your security. And it would be best if you created alerts on them.
- Changes or modifications in Security Solution and Security Policy and Policy Assignment.
- Any changes or modifications in Network Security Group, including deletion.
- Changes or modifications in Network Security Group Rule including deletion.
- Any changes or modifications in Firewall and rules.
- Changes or modifications in SQL Server Firewall rule.
7) Key Management
All the confidential information like passwords are encrypted into keys. These are much secure and act as a password for any security check. But keys need to be properly encrypted and safeguarded to prevent any misuse and loss of keys. Secure key management is a must to protect cloud data.
Azure Key Vault allows storing the encryption and secure keys safely in HSM (Hardware Security Modules). According to the ‘FIPS 140-2 Level 2’ standard, Microsoft processes keys in HSM. For additional threat detection, monitor key usage by sending logs to Azure or Security Information and Event Management (SIEM)
8) Secure Storage
Storage is the key component in your system that stores data. The security of storage is one of the most important aspects on its own. To eliminate data theft risk, Azure Disk Encryption restricts unauthorized data access. BitLocker on Windows and DM-Crypt on Linux is used by disk encryption to encrypt data drives and operating systems.
Also, configure your storage account to use blob encryption, file encryption, and secure transfer. You should regularly update the keys used in your Storage Account and limit the use of Shared Access Signatures to secure transfer and with access for few hours only.
9) Secure Microsoft SQL Server
Microsoft SQL Server is the most common service used by many organizations. Azure detects various threats and attacks like SQL injection and other vulnerabilities, but you can also make it strong by enabling and monitoring SQL Server Firewall regularly. Make your SQL Server Firewall policy more tough and strong and monitor all the security logs, misuse of information, and breaches alert.
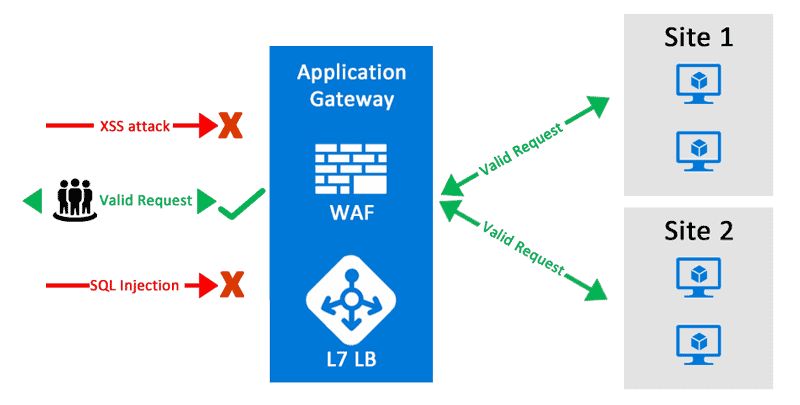
10) Use a WAF with ATM
Azure Web Application Firewall (WAF) is built on top of the Application Gateway service and prevents OWASP 3.0 attacks against Azure SQL databases. You can reduce the chances of attack by reducing the accessibility of your components on the public internet. Use a geolocation filter in Azure Traffic Manager (ATM) to lock down your web app if it is not required to be accessed internationally. So, make certain policies on your ATM to accept limited traffic and block unwanted or international traffic. Finally, make your Web Application Firewall ready only to accept traffic from Azure Traffic Manager (ATM).
Enhancing Azure Security
While traditional tools and programs provide a good starting point, you also need tools with advanced capabilities to protect your applications from changes made by criminals in the cloud. The following additional capabilities are critical to cloud security:
- Insights: Real-time cloud detection, network visibility, and user authentication details will help identify and reduce uncertainty.
- Automation: Integrating automation into cloud security operations with options such as default templates and security rules will help prevent human error and misconfiguration from day one.
- Compliance and Management: Security reports that demonstrate compliance and business management simplify your reporting and auditing process.
- Reduce regular installation: Continuous monitoring of the installation environment against defined security standards and automation of job and policy management will help reduce mis-setting.
- Intelligence and predictive analytics: Intelligence-powered threat hunting and predictive analytics can help identify vulnerabilities faster and generate real-time alerts about violence.
- Workload/Storage Protection (for Containers and Serverless): Extends security features to containers and serverless to protect modern microservice-based workloads.
Conclusion
Securing your Azure environment demands a comprehensive approach by leveraging robust services like Azure Security Center, Azure Firewall, Azure Active Directory, Azure Key Vault, and security monitoring capabilities, combined with best practices such as managing workstations securely, implementing multi-factor authentication, securing administrator access, embracing secure networking principles, monitoring activity log alerts, effective key management, securing storage, hardening SQL Server instances, and utilizing Web Application Firewalls (WAF) with Azure Traffic Manager (ATM) for enhanced application and database protection.
Frequently Asked Questions
What are the security features in Azure?
Microsoft Sentinel. Protect your Azure resources from distributed denial-of-service (DDoS) attacks. Azure Bastion. Fully managed service that helps secure remote access to your virtual machines. Web Application Firewall. Azure Firewall. Azure Firewall Manager.
How do I maintain security in Azure?
Identify all sensitive information. Encrypt data at rest. Encrypt data in transit. Have a backup and disaster recovery (DR) plan. Use a key management solution. Harden your management workstations. Use Azure Information Protection.
What are three examples of security principles in Azure?
These lenses provide a framework for the application assessment questions. Plan resources and how to harden them. Automate and use least privilege. Classify and encrypt data. Monitor system security, plan incident response. Identify and protect endpoints. Protect against code-level vulnerabilities.
What is the benefit of Azure security?
Some Azure Security Center benefits customers can enjoy are: Providing visibility and control over the security of Azure resources (like Virtual Machines, Cloud Services, Azure Virtual Networks, and Blob Storage). Protecting hybrid workloads deployed in Azure or non-Azure environments and on customers' premises.
References
- Microsoft Azure Security Technologies Certification
- Introduction to Azure Sentinel and Steps to Setup
- What is Azure Backup?- Features, Benefits, Tools & Real-life Examples
- Azure Site Recovery: Benefits, Working, Features, and Implementation
- Activity Guides/Hands-on Lab & Projects
- Azure Security vs AWS Security
- What is Azure security?
Next Task for You
Begin your journey toward Mastering Azure Cloud and landing high-paying jobs. Just click on the register now button on the below image to register for a Free Class on Mastering Azure Cloud: How to Build In-Demand Skills and Land High-Paying Jobs. This class will help you understand better, so you can choose the right career path and get a higher paying job.









![AWS DevOps [DOP-C02] Professional Step By Step Activity Guides (Hands-On Labs)](https://k21academy.com/wp-content/uploads/2023/02/DOP-C02-1.png)