In this post, I am going to share some quick tips, including Q/A’s and useful links from Azure Job Oriented Day 5 Training of our recently launched new batch of Microsoft Azure Job Oriented, in which we have 25+ hands-on labs in the course.
On our Day 5 Live Session, we covered Network Security Group, Application Security Group , Bastion Host
The previous week In Day 4 session we covered about Azure VPN Gateway , Express Route.
Two weeks before In Day 3 session we covered about Azure Networking and VNet peering.
Three weeks before In Day 2 session we covered about Azure Resource Manager, Subscriptions, NSG, and PowerShell.
Four weeks before In Day 1 session we covered about Azure Cloud Fundamentals, App Services, and Scaling Strategies.
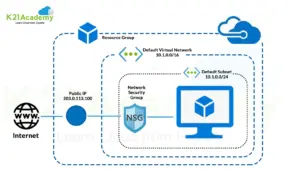
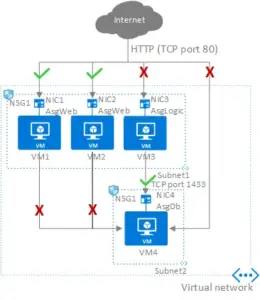
Network Security Group
The Network Security Group (NSG) is a critical component of network security that allows you to regulate traffic to and from Azure resources. An NSG serves as a virtual firewall for your virtual machines (VMs) and other Azure resources within a virtual network, allowing you to establish rules that allow or deny certain types of network traffic. Network Security Groups are essential for enforcing security boundaries and managing network traffic flow within Azure virtual networks. You may improve the security posture of your Azure resources and protect them from unauthorized access and potential threats by defining and administering NSG rules.
Related Readings: Cloud Services Model
Q1) What types of traffic can I control with NSGs?
Ans. NSGs allow you to control both inbound and outbound traffic. You can create rules to allow or prevent traffic based on particular IP addresses, protocols, and port numbers.
Q2) Are NSGs stateful or stateless?
Ans. NSGs are stateful. They automatically allow return traffic related to an established connection initiated from within the virtual network.
Q3) What are some common use cases for NSGs?
Ans. It provides a variety of purpose including:
Improving security by restricting incoming and outbound access to specific ports.
Controlling communication by isolating and segmenting resources within a virtual network.
Controlling virtual machine access depending on source IP addresses.
Application Security Group
Application Security Group (ASG) is a networking feature that allows you to group Azure virtual machines (VMs) based on the application to which they belong. ASGs enable network security group (NSG) policies to be defined using logical application groupings rather than individual VM IP addresses. This simplifies network security rule management, particularly in instances where numerous VMs are part of the same application or service. Application Security Groups are especially useful in complicated and distributed application architectures where VMs must safely communicate across network boundaries. You can use ASGs to ease the maintenance of network security rules, improve security, and simplify application deployment in Azure.
Q1) How do Application security group work?
Ans. ASGs operate by applying a set of security rules to a collection of VMs. The ASG rules are assessed whenever a VM sends or receives network traffic. The ASG rules are reviewed in order, with the first matching the traffic being implemented. If no rules match the traffic, it is dropped.
Q2) Can I use ASGs with peered virtual networks?
Ans. Yes, you can use ASGs with peered virtual networks to control traffic between peered networks based on application tiers.
Q3) Difference between ASG and NSG?
Ans. ASGs offer application-centric security groupings for VMs, allowing for better role-based management and control, whereas NSGs provide network-level security control for traffic filtering based on IP addresses, ports, and protocols.
Related Readings: Azure Region and Availability Zone
Bastion Host
Azure Bastion is a Microsoft Azure fully managed platform solution that allows safe and seamless remote access to virtual machines (VMs) without the need for a public IP address or a VPN connection. It improves the security of remote connections to Azure VMs by acting as a gateway, giving a more secure and streamlined alternative to standard remote access techniques. Azure Bastion is especially beneficial for cases requiring secure remote access to Azure VMs, such as maintaining VMs in a private subnet or avoiding the administration difficulties associated with typical remote access solutions. You can improve the management experience for your Azure infrastructure and increase the security of your remote connections by utilizing Azure Bastion.
Q1) Why do I need a Bastion Host?
Ans. A Bastion Host enhances security by acting as a single entry point for user to access servers within a private network. A Bastion Host enhances security by acting as a single entry point for user to access servers within a private network.
Q2) How does a Bastion Host work?
Ans. User access the Bastion Host over secure protocols such as SSH (for Linux) or RDP (for Windows). They can then make secure connections to other servers or resources within the private network via the Bastion Host. This prevents direct access to internal servers from the internet.
Q3) Is bastion host a proxy server?
Ans. Yes, a bastion host can function as a proxy server.
Q4) What is the difference between a firewall and a bastion host?
Ans. A firewall is a network security device that filters and regulates incoming and outgoing network traffic based on established rules, with the goal of controlling overall network communication. A bastion host, on the other hand, is a dedicated server strategically positioned within the internal network that provides regulated and secure remote access for administrators to handle specific systems while focusing on application-level security and minimizing the attack surface.
Q1)What is an Azure network security Group?
Ans. The Azure Network Security Group (NSG) is a resource that serves as a firewall for traffic to and from Azure resources. Rule-based rules are used by NSGs to allow or refuse traffic based on factors like as source and destination IP addresses, ports, and protocols. They are stateful, which means that response traffic is automatically authorised, and they prioritise rules based on allocated numbers. NSGs can be linked to subnets or network interfaces and provide predefined outbound and inbound rules that can be customised. They also have monitoring and logging capabilities for increased network security.
Q2)What is an Azure Application Security Group?
Ans. Azure Application Security Groups (ASGs) is a feature for streamlining network security. They let you to categorize virtual machines and resources based on their tasks or functions, making it easier to apply network security policies collectively. Because ASGs are dynamic, VMs can join or leave a group based on tags, avoiding the need for human configuration.
Q3)What is a bastion host Azure?
Ans. Azure Bastion is a Microsoft Azure-protected and managed service that serves as a gateway for remote access to virtual machines (VMs) within an Azure Virtual Network. It provides a more secure method of accessing VMs without the use of public IP addresses, minimizing vulnerability to potential threats.
Next Task For You
Begin your journey toward Mastering Azure Cloud and landing high-paying jobs. Just click on the register now button on the below image to register for a Free Class on Mastering Azure Cloud: How to Build In-Demand Skills and Land High-Paying Jobs. This class will help you understand better, so you can choose the right career path and get a higher paying job.







![AWS DevOps [DOP-C02] Professional Step By Step Activity Guides (Hands-On Labs)](https://k21academy.com/wp-content/uploads/2023/02/DOP-C02-1.png)