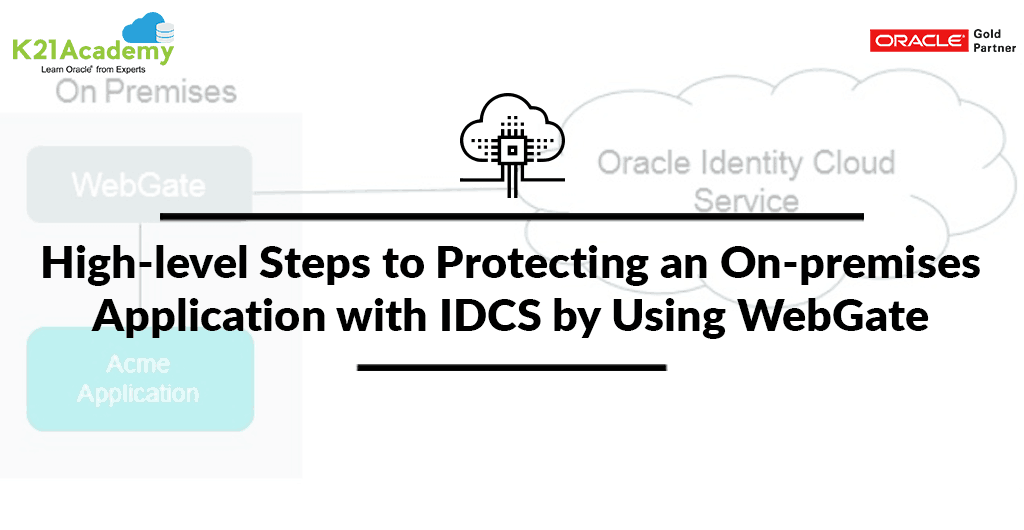
This Post Cover High-Level Steps to protect an on-premises application with Oracle Identity Cloud Service(IDCS) by configuring WebGate.
Introduction
Oracle Access Management uses WebGate to protect an on-premises web application. Instead of relying on Oracle Access Manager for authentication service, WebGate can now interact with Oracle Identity Cloud Service and protect the on-premises web application by using cloud service to authenticate users to access the web application.
If you are new to IDCS, I would highly recommend you to check our post on Oracle Identity Cloud Service (IDCS) Overview & Concepts (Click here) & Cloud Security Using Identity Cloud Service (Click here)
Why IDCS to protect an On-Premise Applications?
Oracle Identity Cloud Service provides identity management, single-sign-on (SSO) and identity governance for applications on-premise, in the cloud and mobile applications. Any user can access the application at any time, anywhere on a device in a secure manner. IDCS has now increased application security for cloud and on-premises workloads, Risk-aware, Enhanced User Productivity, Experience, Reduced Cost & Lot more..
How does IDCS Protect On-Premise Applications?
When an unauthenticated user tries to access the application protected by Oracle Identity Cloud Service, the user is redirected to the Sign In the page of Oracle Identity Cloud Service for authentication.
In this blog, we are using IDCS to protect an On-Premise application by configuring webgate, so you should know about below configurations files to Enable OAuth on Webgate with IDCS.
- Cloud.config — This configuration file has information related to OIDC (OAM/IDCS) server. It is used to configure Webgate for using OAuth/OpenID connect.
- Cloud.policy – Declares the policy to be enforced by the Webgate.
- CWallet– This file contains OAuth Client ID, OAuth Client Secret and Key to encrypt cookies. To establish a connection with an IDP, the Oracle Wallet must be present in the following folder, <WebgateInstanceDir>/config/cwg_wallet
For more information about these configuration files Click here .
Prerequisite
- Oracle WebLogic Server is installed, a domain has been created, and you can access the Oracle WebLogic Server administration console and ensure that EM Console is running on top of Weblogic server.
- Install Oracle HTTP Server 12.2.1.3 (Webgate will be automatically installed when you install OHS) for more information Click here
- WebGate Bundle Patch 28243743 (how to install Bundle patch Click here to check )
- Deploy On-Premise application on Weblogic Server.
- Then, Modify the mod_wl_ohs.conf file and Configure the WebLogic Proxy Plug-In manually by specifying directives in mod_wl_ohs.conf file so Oracle HTTP Server can allow requests to be proxied from Oracle HTTP Server (OHS) to Oracle WebLogic Server. For more information Click here
- After deploying and configuring the application, ensure the application is accessible through Oracle HTTP Server port.
- Download the cloud_config.txt and cloud_policy.txt files to your webgate folder.
- You should have your own Free Cloud Account and able to access IDCS Console. (if you don’t have free cloud account, then use our free guide to create cloud account and access IDCS Console)
Note: We use this same guide to creating Cloud account for Oracle Identity Cloud service (IDCS) Training and our other Cloud Trainings.
HighLevel steps to Protect an On-Premise application with IDCS:
There are two steps of Configuration to protect On-premise application with IDCS by using Webgate.
1. Configuration on Oracle Identity Cloud Service
- Login to the Oracle Identity Cloud Service console using the URL: https://idcshost:port.
- In the Oracle Identity Cloud Service console, expand the Navigation Drawer, click Applications, and then click Add.
- Select Trusted Application.
- Provide the Application URL (Enter the URL http://<hostname>:port/App/index.html, host:port is the Oracle HTTP Server where your WebGate is configured) & Redirected URL (http://<hostname>port/oauth/callback) to Detail & Client tab respectively
- Select Configure this application as a resource server now.
- for the Resources tab, provide the value for the following field Primary Audience, Secondary Audience, Allowed Scopes etc.
- then, click Next until you reach the last pane, and then click Finish to save the application.
- Record the values of Client ID and Client Secret for the application, and then click Close (these Client ID and Client Secret would be required when you will Create a wallet in the WebGate folder.)
- After the application is created and saved. Select the Configuration tab, expand the Client Configuration> section. In the Accessing APIs from Other Applications section, under Allowed Scopes, click Add. In the Add Scope dialog, select Application (name of the application) and click on Add to assign the application to the scope. Click Save to save your changes.
- Select the Configuration tab, expand the Client Configuration section. In the Accessing APIs from Other Applications section, under Grant the client access to Identity Cloud Service Admin APIs, click Add. In the Add App Role dialog, select Identity Domain Administrator role and click on Add to assign the app Roles. Click Save to save your changes.
- To activate the application, click Activate button, and then click Activate Application. Oracle Identity Cloud Service displays a confirmation message.
2. Configure WebGate to Interact with Oracle Identity Cloud Service
- Launch a terminal and navigate to the WebGate folder
- cd $OAM_DOMAIN/config/fmwconfig/components/OHS/ohs1/webgate/config
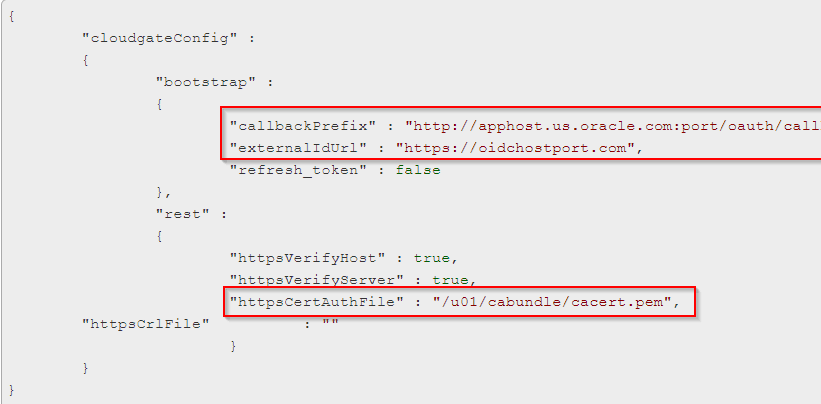
- In the WebGate folder, edit downloaded cloud.config file with following parameter callbackPrefix <http://<hostname>:port/oauth/callback>, externalIDUrl <https://idcshost:port>, httpsCertAuthFile is Optional to chnage .
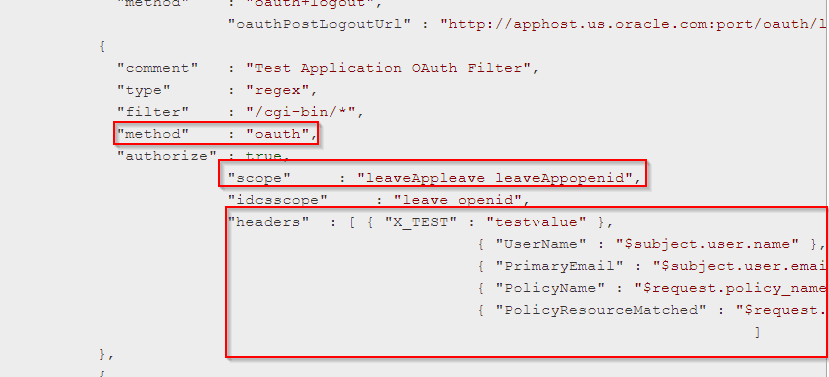
- In the WebGate folder, edit downloaded cloud.policy file with following parameter filter, Policy name, scope, idcsscope, headers (for more information about how to edit configuration file click here)
- Create a wallet in the WebGate folder to store Client ID and Client Secret of the On-Premise application. for more information on the creation of wallet click here
- Finally, Test the On-premise Application.
This post is from our Oracle Identity Cloud Service (IDCS) training in which we have covered everything one should know about Oracle Identity Cloud Service like Architecture, Users & Groups Application, Branding, Auditing & Reports, Rest APIs and much more..
Interested? Register for Free Master Class on Cloud Security Using Oracle IDCS: Career Path & What to Learn?
Related Posts
- Cloud Security With Oracle Identity Cloud Service (IDCS) Click here
- Oracle Identity Cloud Service (IDCS): Step By Step Lab Activity Guide for Beginners Click here
- Oracle Identity Cloud Service (IDCS) Overview & Concepts Click here
- Cloud Security Using Identity Cloud Service Click here
- Oracle Identity Cloud Service: Configuring Multi-Factor Authentication (MFA) Click here
References
- Protecting an On-premises Application with Oracle Identity Cloud Service by Using WebGate
- Video [Protecting an On-premises Application with Oracle Identity Cloud Service by Using WebGate]
Register for Free Master Class on Cloud Security Using Oracle IDCS: Career Path & What to Learn?
Next Task for You
Download our 7 Docs free Guide to become Expert in Oracle Identity Cloud Service(IDCS) for Security & Identity Administrator.
Click on Below image to download the guide:







![AWS DevOps [DOP-C02] Professional Step By Step Activity Guides (Hands-On Labs)](https://k21academy.com/wp-content/uploads/2023/02/DOP-C02-1.png)