This blog post will go through some quick tips including Q/A and related blog posts on the topics that we covered in the Azure Admin Day 7 Live Session which will help you gain a better understanding and make it easier for you to
The previous week, In Day 6 session we got an overview of Module 7: Azure Storage where we have covered topics like Azure Storage, Azure Storage Account Types, Azure Core Storage Services, Azure Table Storage, Azure Storage Blob, Blob Storage Categories, Blob Storage Access Tiers, Azure Queue Storage, Azure File Storage, Managed and Unmanaged Disks in Azure, Azure Storage Redundancy, Storage Access Keys, Azure Private Link Endpoint, Azure Shared Access Signatures.
In this blog, I am going to share some quick tips including Q/A and useful links from Day 7 of Azure Admin covering Module 8: Azure Active Directory where we have covered topics like Identity and access management, Azure Active Directory, Azure Active Directory Concepts, Azure AD Comparison with Active Directory, Azure RBAC, Azure Active Directory Roles, Azure AD Connect, Azure AD Registered Devices, Azure AD Join, Azure Identity Protection, Conditional Access, Multi-Factor Authentication.
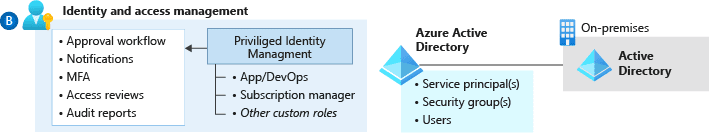
Identity and Access Management
Identity provides the basis for a large percentage of security assurance. It enables access based on identity authentication and authorization controls in cloud services to protect data and resources and to decide which requests should be permitted.
Identity and access management (IAM) is boundary security in the public cloud. It must be treated as the foundation of any secure and fully compliant public cloud architecture. Azure offers a comprehensive set of services, tools, and reference architectures to enable organizations to make highly secure, operationally efficient environments as outlined here.
Q1. Why do we need identity and access management?
Ans. The technological landscape in the enterprise is becoming complex and heterogeneous. To manage compliance and security for this environment, IAM enables the right individuals to access the right resources at the right time for the right reasons.
Azure Active Directory
Active Directory (AD) is a database and set of services that connect users with the network resources they need to get their work done. The database (or directory) contains critical information about your environment, including what users and computers there are and who’s allowed to do what.
The Active Directory structure includes three main tiers: Domains, Trees, and Forests.
Several objects (users or devices) that all use the same database may be grouped into a single domain. Multiple domains can be combined into a single group called a tree. Multiple trees may be grouped into a collection called a forest. Each one of these levels can be assigned specific access rights and communication privileges.
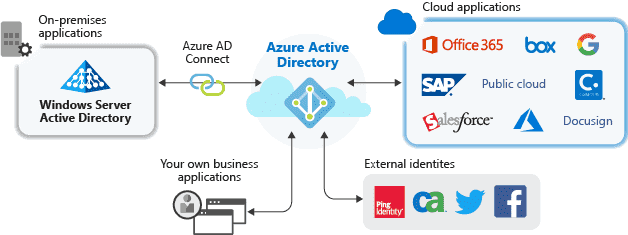
Azure Active Directory (Azure AD) is Microsoft’s multi-tenant cloud-based directory and identity management service, which helps your employees sign in and access resources in:
- External resources, such as Microsoft 365, the Azure portal, and thousands of other SaaS applications.
- Internal resources, such as apps on your corporate network and intranet, along with any cloud apps developed by your own organization.
Read more on Azure Active Directory
Q2. Why do we need Azure Active Directory?
Ans. Cost-effective and easy to use, Azure AD helps businesses streamline processing, and improve productivity and security, while single sign-on (SSO) gives employees and business partners access to thousands of cloud applications – such as Office 365, Salesforce, and DropBox.
Q3. What’s the relationship between Azure AD, Microsoft 365, and Azure?
Ans. Azure AD provides you with a common identity and access capabilities to all web services. Whether you are using Microsoft 365, Microsoft Azure, Intune, or others, you’re already using Azure AD to help turn on sign-on and access management for all these services. All users who are set up to use web services are defined as user accounts in one or more Azure AD instances. You can set up these accounts for free Azure AD capabilities like cloud application access.
Azure AD paid services like Enterprise Mobility + Security complement other web services like Microsoft 365 and Microsoft Azure with comprehensive enterprise-scale management and security solutions.
Azure Active Directory Concepts
Identity: Anything that can be authenticated. It can be a user with a username & password, applications, or other services that require authentication.
Account: Identity with data associated.
Azure AD Account: Identity created using Azure AD or other Microsoft cloud services.
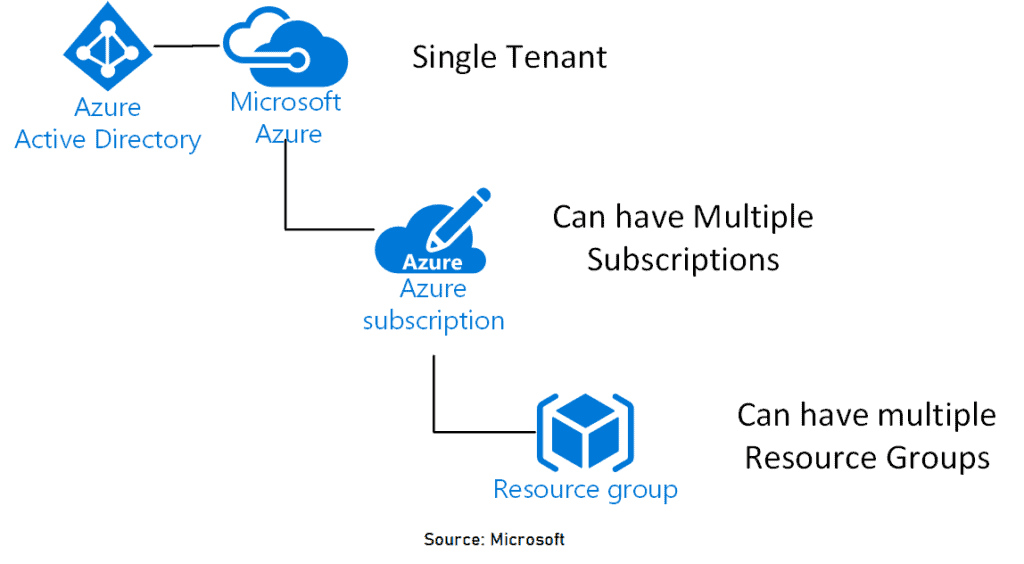
Azure Tenant: An Instance of Azure AD created when an organization signs up for a Microsoft Cloud service subscription.
Azure AD Directory: Each Azure Tenant has a dedicated and trusted Azure AD Directory.
Users: Azure AD defines users in three ways:
- Cloud identities: These users exist only in Azure AD. Examples are administrator accounts and users that you manage yourself.
- Directory-synchronized identities: These users exist in an on-premises Active Directory. A synchronization activity that occurs via Azure AD Connect brings these users into Azure.
- Guest users: These users exist outside Azure. This type of account is proper when external vendors or contractors need access to your Azure resources.
Groups: Azure AD Groups is a collection of Users which helps the resource owner assign a set of access permissions to all the members of the group instead of having to provide the rights one by one.
User Subscription: To pay for Azure cloud services used.
Q4. What is a Tenant in Azure Active Directory?
Ans. A tenant represents an organization in Azure Active Directory. It’s a dedicated Azure AD service instance that an organization receives and owns when it signs up for a Microsoft cloud service such as Azure, Microsoft Intune, or Microsoft 365. Each Azure AD tenant is distinct and separate from other Azure AD tenants.
Q5. Can Azure AD be used with AWS?
Ans. Yes, you can use it with AWS or any other cloud provider. Azure AD is just an identity provider. As long as your application can communicate with Azure AD, you be used as an authentication provider.
We also have Azure Active Directory single sign-on (SSO) integration with AWS Single-Account Access.
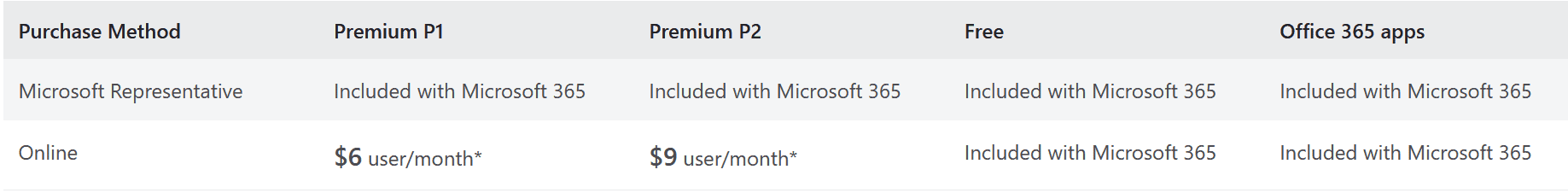
Q6. What is the pricing for Azure Active Directory?
Ans. Azure Active Directory comes in four editions—Free, Office 365 apps, Premium P1, and Premium P2. The Free edition is included with a subscription to a commercial online service, e.g. Azure, Dynamics 365, Intune, and Power Platform. The other three editions have their different features, and pricing is different for them also.
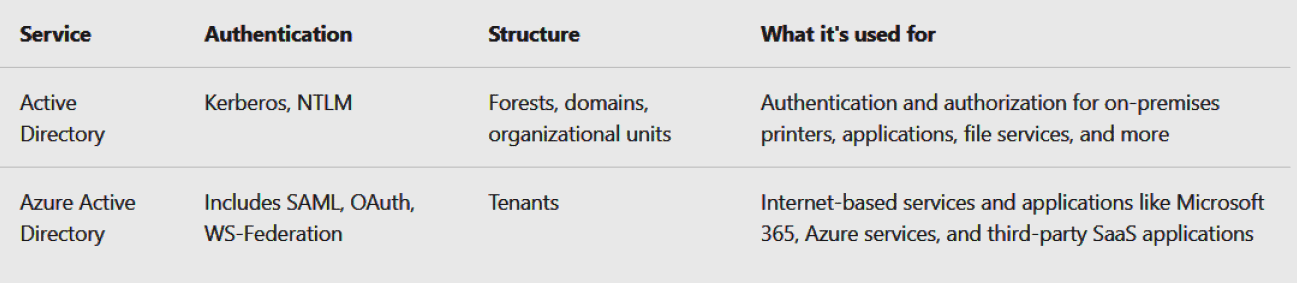
Azure AD comparison with Active Directory
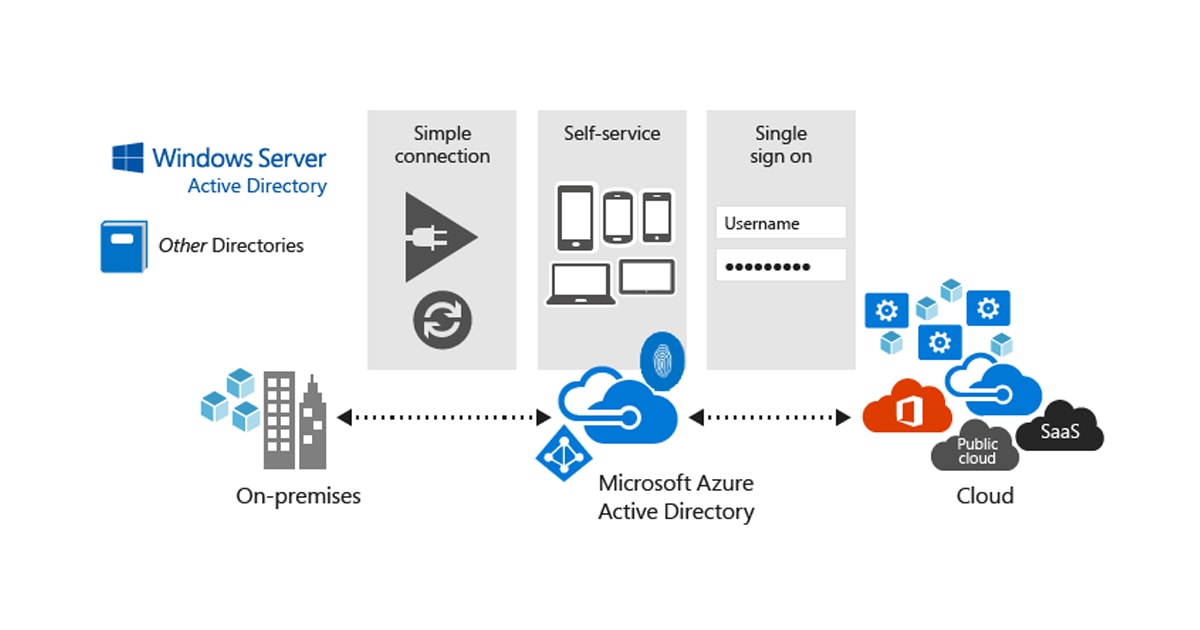
Azure Active Directory is a cloud-based identity solution that helps you manage users and applications, Where Active Directory manages objects, like devices and users, on your on-premises network.
Check more on: Azure AD vs Active Directory
Q7. Can I create multiple managed domains for a single Azure AD directory?
Ans. No. You can only create a single managed domain serviced by Azure AD Domain Services for a single Azure AD directory.
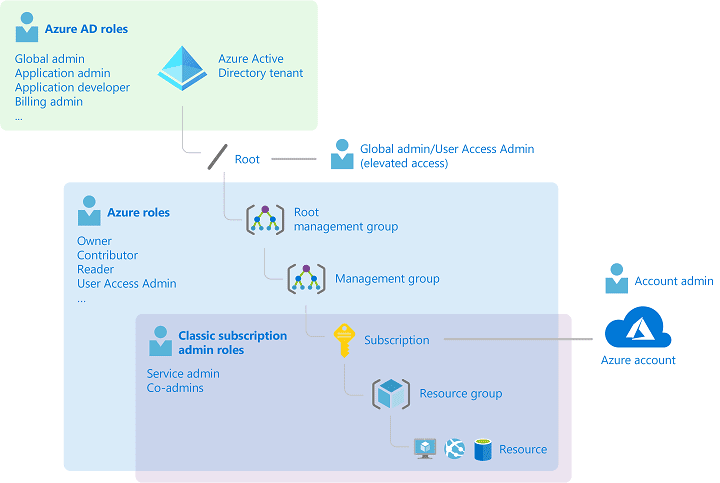
Azure RBAC (Role-Based Access Control)
Azure RBAC (Role-Based Access Control) is the system that allows control over who has access to which Azure resources, and what those people can do with those resources. A role might be described as a collection of permissions.
Azure RBAC has many built-in roles, and you can create custom roles.
Here are four examples of built-in roles:
- Owner: Has full access to all resources, including the ability to delegate access to other users.
- Contributor: Can create and manage Azure resources.
- Reader: Can view only existing Azure resources.
- User Access Administrator: Can manage access to Azure resources.
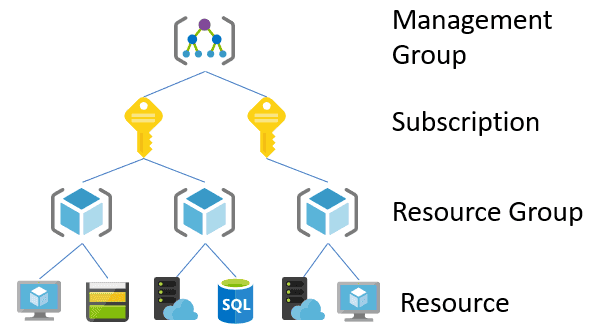
Scope of Azure RBAC
Scope is the set of resources that access applies to. When you assign a role, it’s important to understand the scope so that you can grant a security principal just the access that it really needs. Scopes are structured in a parent-child relationship. Each level of hierarchy makes the scope more specific. You can assign roles at any of these levels of scope. The level you select determines how widely the role is applied. Lower levels inherit role permissions from higher.
- Azure management groups help you manage your Azure subscriptions by grouping them together.
- Azure subscriptions help you organize access to Azure resources and determine how resource usage is reported, billed, and paid for.
- Resource groups are containers that hold related resources for an Azure solution. A resource group includes those resources that you want to manage as a group.
- Resources are a manageable item in Azure. For example virtual machines, storage accounts, web apps, etc.
Azure Active Directory Roles
Azure AD also has its own set of roles, which apply mostly to users, passwords, and domains. These roles have different purposes.
Global Administrator: Can manage access to administrative features in Azure AD. A person in this role can grant administrator roles to other users, and they can reset a password for any user or administrator.
User Administrator: Can manage all aspects of users and groups, including support tickets, monitoring service health, and resetting passwords for certain types of users.
Billing Administrator: Can make purchases, manage subscriptions and support tickets, and monitor service health. Azure has detailed billing permissions in addition to Azure RBAC permissions.
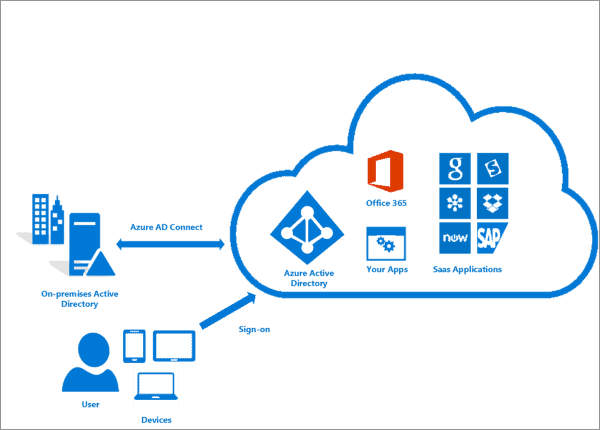
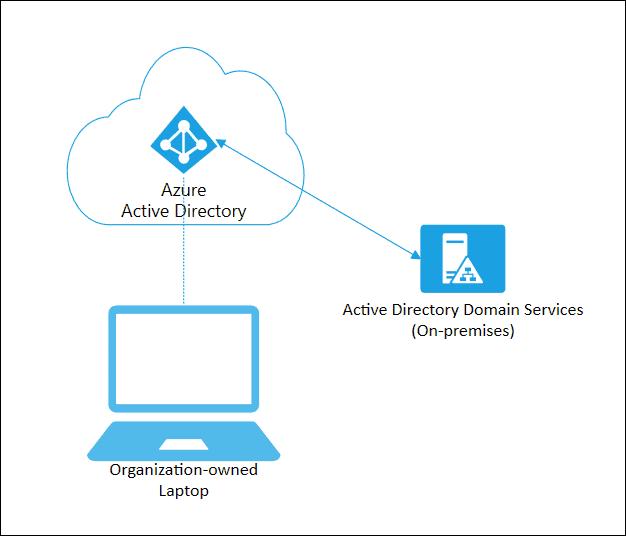
Azure AD Connect
It is used to integrate the on-premise directories (Active Directories) with Azure Active Directory which provides a common identity for accessing both cloud and on-premise resources.
There are various features of Azure AD Connect:
1) Password Hash Synchronization: Sign-in method that synchronizes a hashed user on-premised AD password with Azure AD.
2) Pass-through authentication: Sign-in method that provides access to users to use the same password on-premise and on the cloud.
3) Synchronization: Responsible for creating users, groups, and other objects and also validating if the identity information of your on-premise users and groups match with the cloud.
4) Health Monitoring: A central place to view the activity and also provide monitoring.
Q8. What are the license requirements for using Azure AD Connect?
Ans. Azure AD Connect feature is free and available with our Azure subscription
Q9. What is Azure AD B2B collaboration?
Ans. Azure Active Directory (Azure AD) business-to-business (B2B) collaboration is a feature that allows us to invite guest users to our organization. With B2B collaboration, you can securely share our applications and services with guest users from any other organization, while maintaining control and security of our organization’s data.
Azure AD registered devices
Azure AD registered devices are signed in to using a local account as a Microsoft account on a Windows 10 device. These devices have an Azure AD account for access to organizational resources.
Azure AD Join
Azure AD Join is designed to provide access to organizational apps and resources and to simplify Windows deployments of work-owned devices. AD Join has these benefits.
- Single-Sign-On (SSO) to your Azure-managed SaaS apps and services. Your users won’t have additional authentication prompts when accessing work resources. The SSO functionality is available even when users are not connected to the domain network.
- Enterprise compliant roaming of user settings across joined devices. Users don’t need to connect to a Microsoft account (for example, Hotmail) to observe settings across devices.
- Access to Microsoft Store for Business using an Azure AD account. Your users can choose from an inventory of applications pre-selected by the organization.
- Windows Hello support for secure and convenient access to work resources.
- Restriction of access to apps from only devices that meet the compliance policy.
- Seamless access to on-premise resources when the device has a line of sight to the on-premises domain controller.
Q10. Can a disabled or deleted user sign in to an Azure AD joined device?
Ans. Yes, but only for a limited time. When a user is deleted or disabled in Azure AD, it’s not immediately known to the Windows device. So users who signed in previously can access the desktop with the cached username and password.
Q11.Does Azure AD Domain Services include high availability options?
Ans. Yes. Each Azure AD Domain Services managed domain includes two domain controllers. You don’t manage or connect to these domain controllers, they’re part of the managed service. If you deploy Azure AD Domain Services into a region that supports Availability Zones, the domain controllers are distributed across zones. In regions that don’t support Availability Zones, the domain controllers are distributed across Availability Sets. You have no configuration options or management control over this distribution. For more information, see Availability options for virtual machines in Azure.
Q12. Why am I asked to remove a user from an Azure AD group when I delete that user from my organization?
Ans. Users can belong to your organization, both as individuals and as members of Azure AD groups in Azure DevOps groups. These users can still access your organization while they’re members of these Azure AD groups.
To block all access for users, remove them from Azure AD groups in your organization, or remove these groups from your organization. We currently can’t block access completely or make exceptions for such users.
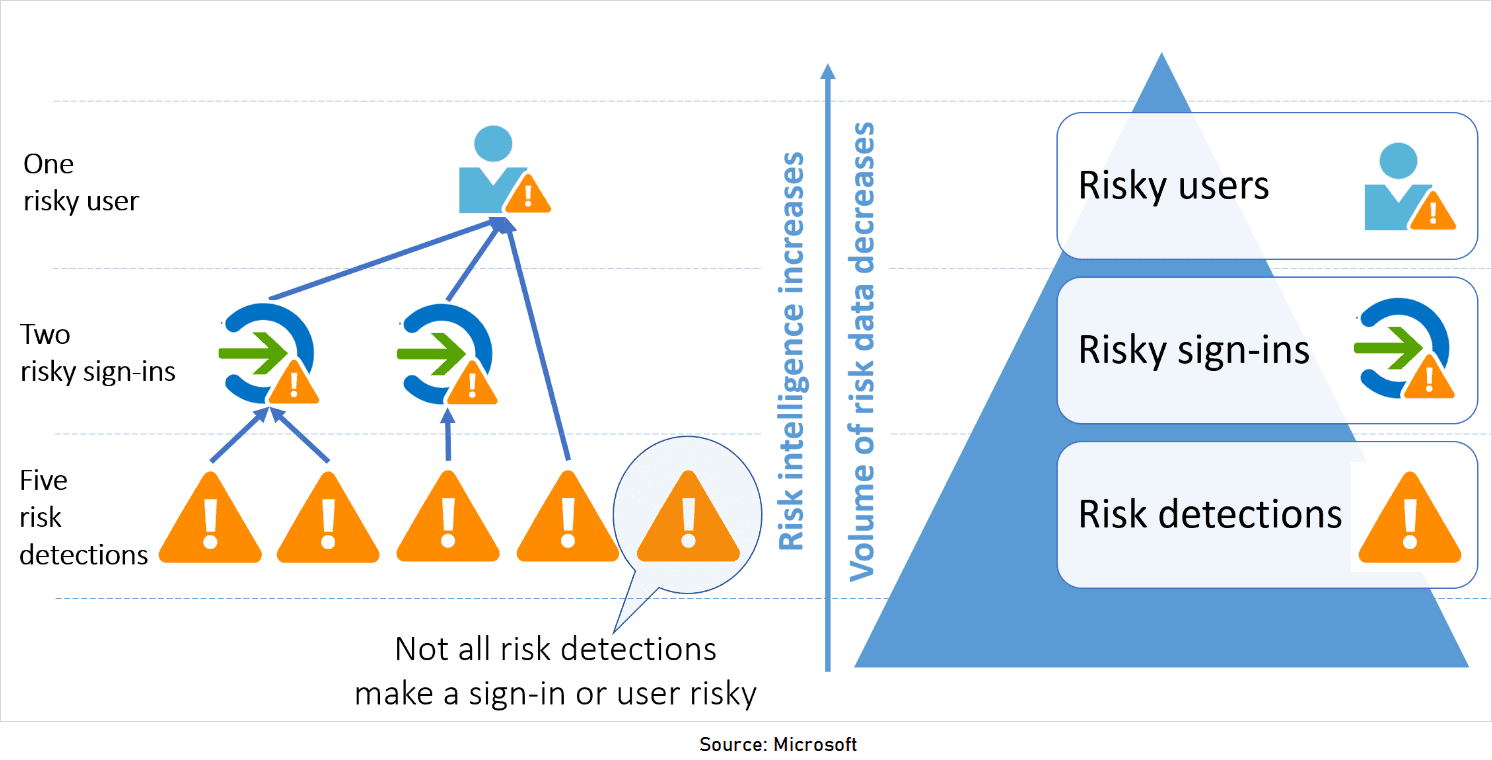
Azure Identity Protection
Azure Active Directory (Azure AD) Identity Protection helps keep you informed of suspicious users and sign-in behavior in your environment. Identity Protection uses the learnings Microsoft has acquired from their position in organizations with Azure AD, the consumer space with Microsoft Accounts, and in gaming with Xbox to protect your users.
Q13. What is a risky user?
Ans. A user risk or risky user represents the probability that a given identity or account is compromised. You can gauge the probability of compromised user accounts in your environment. A user flagged for risk is an indicator for a user account that might have been compromised.
Q14. Which licensing plan supports Identity Protection?
Ans. You need Azure Active Directory Premium P2 to use Identity Protection.
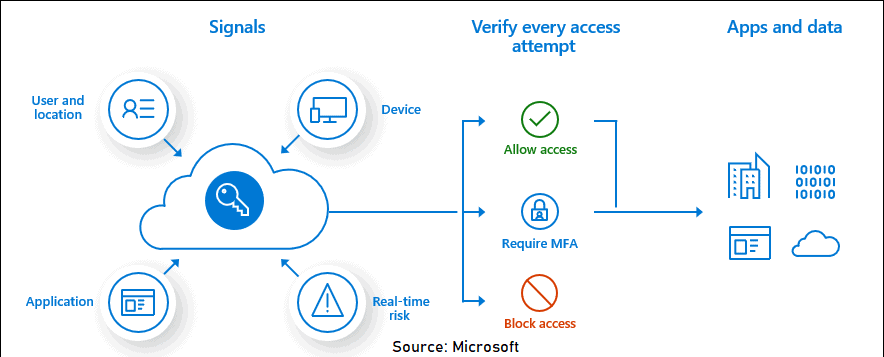
Conditional Access
Conditional Access is the tool used by Azure Active Directory to bring signals together, make decisions, and enforce organizational policies. Conditional Access is at the heart of the new identity-driven control plane. Conditional Access policies, at their simplest, are if-then statements. If a user wants to access a resource, then they must complete an action.
Q15. Are Conditional Access policies enforced for B2B collaboration and guest users?
Ans. Policies are enforced for business-to-business (B2B) collaboration users. However, in some cases, a user might not be able to satisfy the policy requirements.
For example, a guest user’s organization might not support multi-factor authentication.
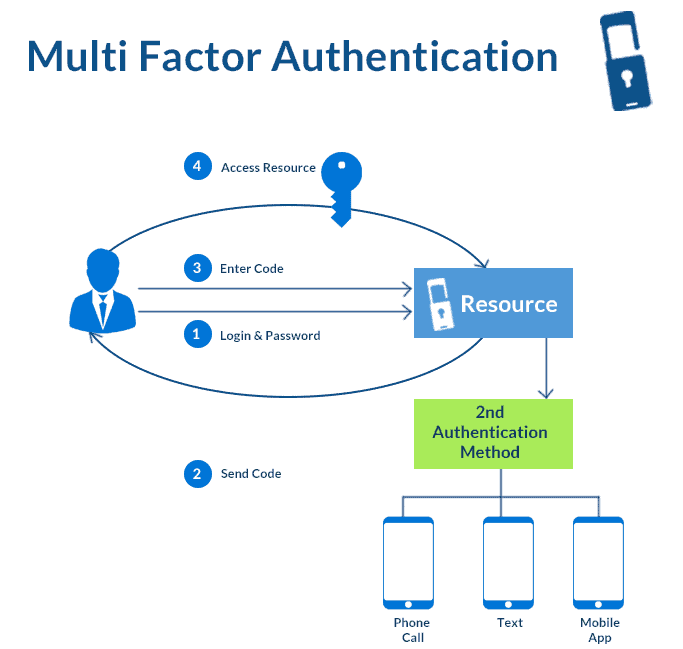
Multi-Factor Authentication (MFA)
Azure Multi-Factor Authentication(MFA) is an addition to a two-step verification process. This becomes quite a challenge for attackers to hack into someone’s ID. Even if the hacker or attacker knows the user ID and password, it is useless without an additional authentication method. This is a trusted security feature that can guarantee the solid security of your accounts. Various methods such as facial recognition, fingerprint access, registered mobile number, etc., are helpful in Multi-Factor Authentication.
Check More on Azure MFA.
Q16. Is there a free version of Azure AD Multi-Factor Authentication?
Ans. Security defaults can be enabled in the Azure AD Free tier. With security defaults, all users are enabled for multi-factor authentication using the Microsoft Authenticator app. There’s no ability to use text message or phone verification with security defaults, just the Microsoft Authenticator app.
Quiz Time (Sample Exam Questions)!
With our Microsoft Azure Administrator training program, we cover 150+ sample exam questions to help you prepare for the certification AZ-104.
Check out one of the questions and see if you can crack this…
Ques: In Azure, the ability to deploy, manage, and monitor all the resources for your solution as a group, rather than handling these resources individually is a feature of which of the following?
A. Resource Groups
B. Resource Manager
C. Azure Analytics
D. All of the above
The right answer will be revealed in next week’s blog. Here is the answer to the question shared last week.
Ques: In Azure, the ability to deploy, manage, and monitor all the resources for your solution as a group, rather than handling these resources individually is a feature of which of the following?
A. Database
B. Language
C. Framework
D. All of the above
Answer: A
Explanation: Yes, Active Directory is a Database.
Feedback
We always work on improving and being the best version of ourselves from the previous session hence constantly ask feedback from our attendees.
Here’s the feedback that we received from our trainees who had attended the session…
Here 2107 is in YYMM format, represents the trainees from the batch of July 2021.
Related/References
- [Recap] Day 6: Azure Storage [Azure Administrator] [AZ-104]
- [Recap] Day 5: Azure Virtual Machines [Azure Administrator] [AZ-104]
- Azure Storage Accounts Overview & Steps To Create
- Azure Blob Storage: Features, Usage, And Steps to Create
- Multi-Factor Authentication
Next Task For You
Begin your journey toward Mastering Azure Cloud and landing high-paying jobs. Just click on the register now button on the below image to register for a Free Class on Mastering Azure Cloud: How to Build In-Demand Skills and Land High-Paying Jobs. This class will help you understand better, so you can choose the right career path and get a higher paying job.








![AWS DevOps [DOP-C02] Professional Step By Step Activity Guides (Hands-On Labs)](https://k21academy.com/wp-content/uploads/2023/02/DOP-C02-1.png)