In this post, I have shared some quick tips, including Q/A and useful links from the Day 2 live session of our current batch of Certified Kubernetes Security Specialists [CKS].
This series will help you better understand and make it easier for you to learn Docker and Kubernetes, clearing Certification [CKS] & get a better-paid job.
In our Certified Kubernetes Security Specialist training program, we started right from scratch on Day-1. Now on Day 2 of our training program, we covered these topics:
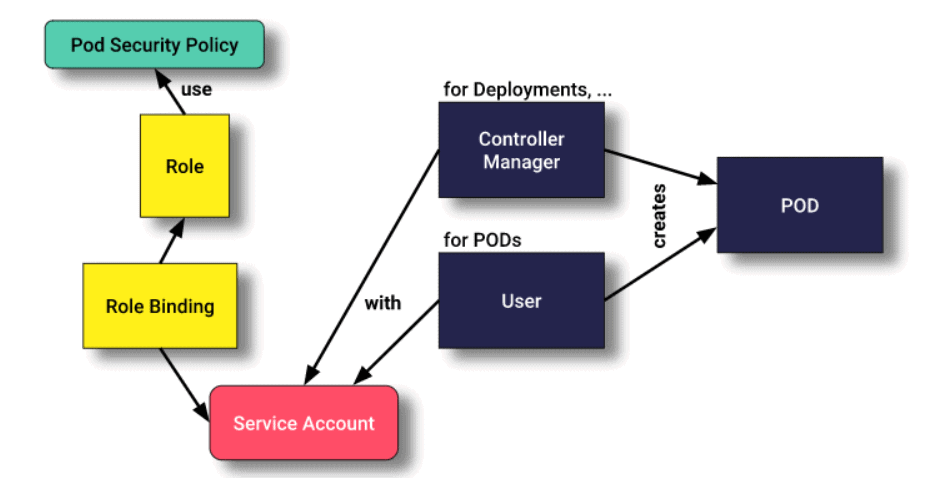
Then we went ahead with Service Account concepts and introduced why Service Account is an important aspect in Kubernetes.
- Introduction to Service Account & Exercise caution in using service accounts
Even we started with the Network Policy and discussed why it is important in Kubernetes
We also covered hands-on Lab 6, Lab 7, Lab 8 & Lab 9 out of our 27+ extensive labs.
Know everything about the CKS Certification
So, here are some of the Q/A’s asked during the Live session from Module 2: Kubernetes Cluster Setup.
➪Role Based Access Control (RBAC)
Role-based access control (RBAC) is a method of regulating access to Kubernetes object resources based on the roles of individual users within your organization.
RBAC authorization uses the rbac.authorization.k8s API group to drive authorization decisions, allowing you to configure policies through the Kubernetes API dynamically.
Q-1. What is Role binding in RBAC?
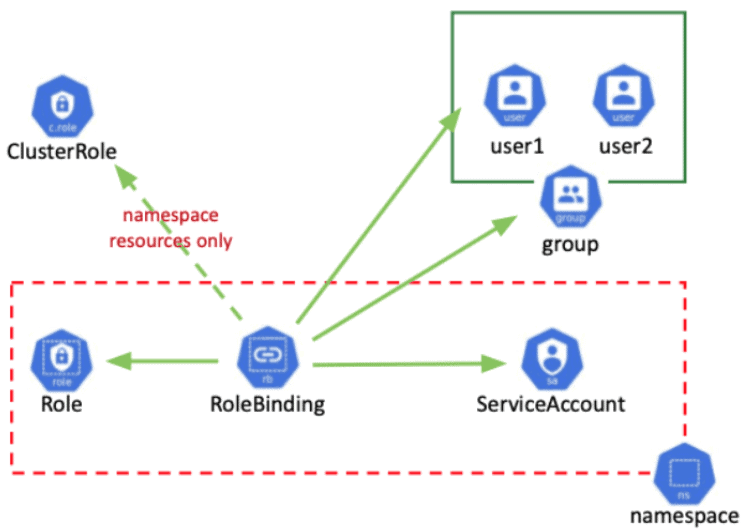
Ans. Role Binding in Kubernetes Role-Based Access Control is used for granting permission to a Subject in a Kubernetes cluster. Subjects are nothing but a group of users, services, or teams attempting Kubernetes API. It defines what operations a user, service, or group can perform.
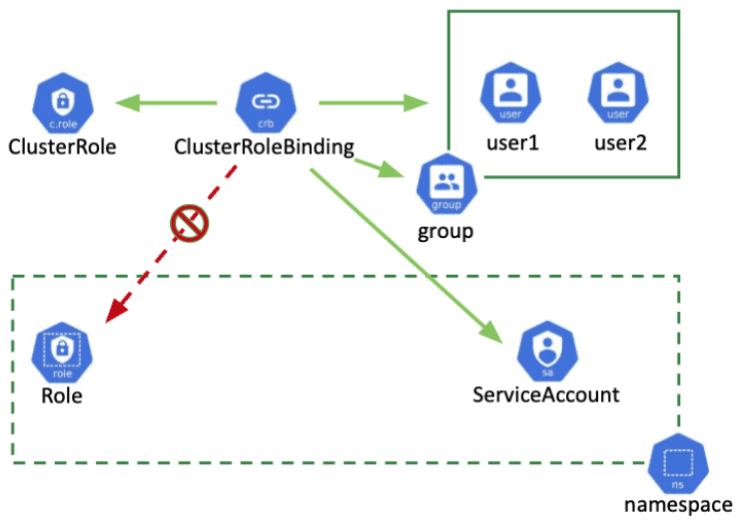
Q-2. What is Cluster Role Binding In RBAC?
Ans. Cluster Role Binding in RBAC is used to grant permission to a subject on a cluster-level in all the namespaces. It will offer you permissions for cluster resources, and it can even offer you permissions for resources within any namespace within a cluster.
➪ Service Account
Service accounts are used to provide an identity to the pods in Kubernetes. Pods that want to interact with the API server will authenticate with a particular service account. By default, applications will authenticate as the default service account in the namespace they are running in. This means, for example, that an application running in the test namespace will use the default service account of the test namespace.
Read more about How to Configure Service Accounts for Pods.
Q-3. How to create a Service Account?
Ans. We can create Service Account using two ways-
- Imperative.
- Declarative.
↦ Create A Service Account in an Imperative way :
$ kubectl create serviceaccount my-service-account
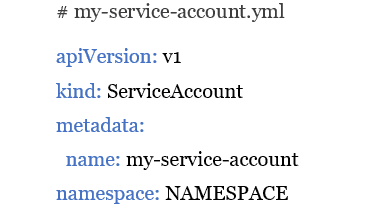
↦Creating a Service Account in a declarative way:
You can use the following manifest to create a service account. Replace NAMESPACE with the namespace you want to use and optionally rename the service account.
Then Create the object with-
$kubectl apply -f my-service-account.yml
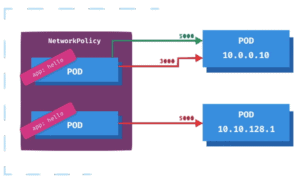
➪ Kubernetes Network Policy
Network policies are Kubernetes resources that allow you to control the traffic between Pods and/or endpoints on the network. Most CNI plug-ins support network policy execution, but if they do not, the created network policy will be ignored.
The most popular CNI plugins with network policy support are:
- Weave
- Calico
- Canal
- Cilium
Q-4. What is an ingress network?
Ans. Inbound traffic includes all data communications and network traffic, which originate from the external network and are destined for nodes on the host network. Inbound traffic can be any form of traffic originating from an external network and destined for the host network.
Q-5. What is Kubernetes egress?
Ans. Inbound and Outbound From the perspective of a Kubernetes Pod, the input is the incoming connection to the Pod, and the output is the outgoing connection from the Pod. In the Kubernetes network policy, create inbound and outbound “permissions” rules (outbound, inbound, or both) independently.
Q-6. Why is network policy important?
Ans. The Value of Cybersecurity Strategy Information is the most important product for many business organizations. They have sensitized company employees to security issues and helped the company demonstrate its commitment to protecting valuable data assets.
Quiz Time!
With our Certified Kubernetes Security Specialist [CKS] training program, we cover real exam questions to help you prepare for the CKS certification.
Check out one of the simple questions and see if you can crack this…
Ques: Which of the following is not a type of security attack?
A. Active
B. Passive-aggressive
C. Passive
The right answer will be revealed in my next week’s blog.
Here is the answer to the question shared last week.
Ques: What are the four C’s of Cloud security? (Choose 4 in the right order)
A. Code
B. Certificate
C. Container
D. Co-Operation
E. Cluster
F. Cloud/Co-Lo/Corporate Datacenter
Correct Answer: A, C, E, D
Explanation:
Each layer of the Cloud Security model builds upon the next outermost layer. The Code layer benefits from strong base (Cloud, Cluster, Container) security layers.
Feedback
We always work on improving and being the best version of ourselves from the previous session hence constantly ask feedback from our attendees.
Here’s the feedback that we received from our trainees who had attended the session…
References
- Certified Kubernetes Security Specialist (CKS): Everything You Must Know
- How to generate a Certificate in Kubernetes
- Kubernetes Dashboard: An Overview, Installation, and Accessing
- Kubernetes for Beginners
- Certified Kubernetes Security Specialist (CKS): Everything You Must Know
- Kubernetes Security for Beginners
- Certified Kubernetes Security Specialist (CKS): Step-by-Step Activity Guide (Hands-on Lab)
Next Task For You
Begin your journey towards becoming a Certified Kubernetes Security Specialist [CKS] by joining our FREE CLASS. You will also know more about the Roles and Responsibilities, Job opportunities for K8s security specialists in the market.




![AWS DevOps [DOP-C02] Professional Step By Step Activity Guides (Hands-On Labs)](https://k21academy.com/wp-content/uploads/2023/02/DOP-C02-1.png)