In the dynamic world of cloud computing, microservices have become the architecture of choice for developing scalable and flexible applications. However, managing communication and security between services can be complex. Enter Istio, the open-source service mesh that simplifies the deployment, management, and security of microservice architectures.
This blog will explore:
- Understanding the Microservices Landscape
- What is Istio?
- Features of Istio
- How Istio Works
- Getting Started with Istio
- Conclusion
Understanding the Microservices Landscape
Before we jump into Istio, let’s briefly recap the challenges associated with microservices architecture. In a microservices-based system, applications are composed of small, independent services that communicate with each other to deliver overall functionality. While this approach offers flexibility and scalability, it introduces complexities in terms of service discovery, load balancing, fault tolerance, and security.
What is Istio?
Istio is an open-source service mesh platform that helps manage and secure communication between the different parts of a distributed application. In simpler terms, it acts as a control plane for the microservices in your application, providing features such as load balancing, traffic routing, service discovery, and observability.
When you build a complex application using microservices, where each service handles a specific functionality, communication between these services becomes crucial. Istio helps simplify this communication by providing a dedicated infrastructure layer that sits between the services. It enables you to configure and control the traffic flow between services without modifying the application code.
Also Read: Our blog post on What is Service Mesh?
Features of Istio
Istio comes with a set of capabilities designed to address common challenges in microservice architectures:
- Traffic Management: Istio makes it easier to control the flow of data between services, allowing for advanced routing, load balancing, and handling of failures.
- Security: It enhances security by managing authentication, authorization, and encryption of service communication, all without requiring changes to the microservices themselves.
- Observability: Istio provides detailed insights into your services, including logging, tracing, and monitoring of all communications, which helps in identifying and resolving issues quickly.
How Istio Works
Istio introduces a lightweight proxy, Envoy, which is deployed alongside each service. This setup, often called a sidecar, intercepts communication to and from the service, allowing Istio to manage, observe, and secure traffic without altering the service code.
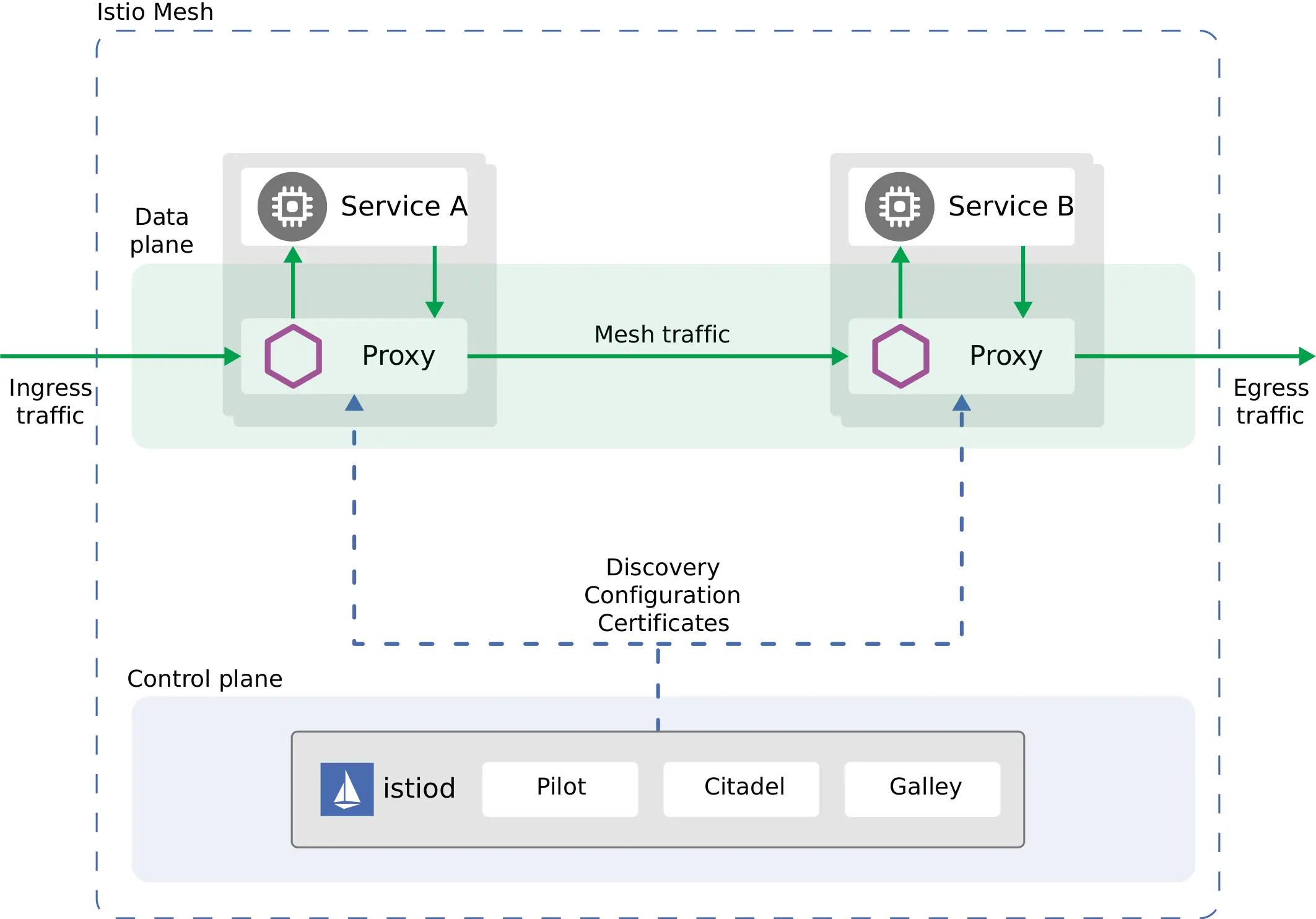
Istio’ s Architecture: Control and Data Planes
Istio is structured around two main components:
- Control Plane: This is the brain behind Istio, responsible for managing and configuring the proxies to route traffic, enforce policies, and provide security measures.
- Data Plane: Made up of the Envoy proxies deployed with the services, the data plane handles the actual network communication, data monitoring, and security enforcement based on the configurations from the control plane.
Getting Started with Istio
Getting started with Istio involves a few key steps that enable you to leverage its full capabilities for managing microservices. Here’s a basic guide to help you begin your journey with Istio, focusing on setting up the control plane with Istiod and integrating the data plane using Envoy Proxy.
Istio is designed to operate on Kubernetes. Make sure you have a running cluster with sufficient resources to deploy Istio and your applications.
Step 1: Install Istio
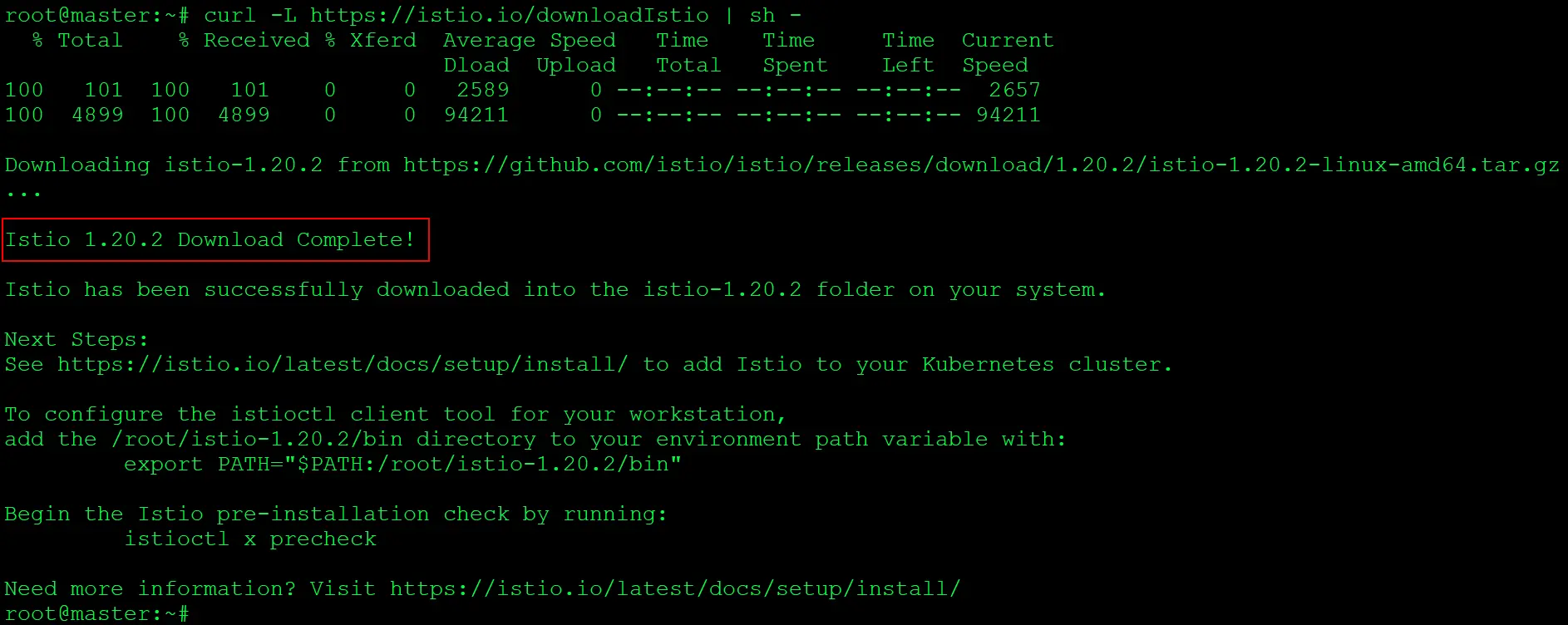
1. Go to the Istio release page to download the installation file for your OS, or download and extract the latest release automatically.
$ curl -L https://istio.io/downloadIstio | sh -
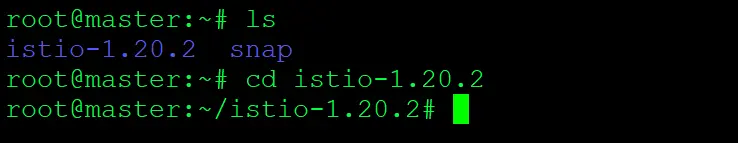
2. Check the downloaded Istio packages and move to the istio package directory.
$ ls $ cd istio-1.20.2
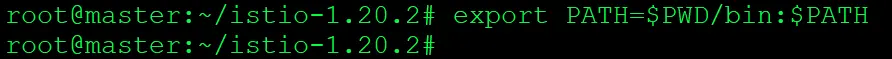
3. Add the istioctl client to your path
$ export PATH=$PWD/bin:$PATH
4. Install Istio, For this installation, we use the demo configuration profile.
$ istioctl install --set profile=demo -y
5. Verify that Istio has installed and ensure that all pods are running
$ kubectl get ns $ kubectl get pods -n istio-system
Step 2: Enable Automatic Sidecar Injection
We inject the Envoy sidecar proxy as part of the Istio installation. The Envoy proxy handles traffic between microservices, enabling Istio to manage advanced features like traffic routing and security.
1. Let us create a normal pod without any side car
$ kubectl run pod1 --image httpd $ kubectl get pods
In this pod, we can observe that one container has been created and is in a ready state.
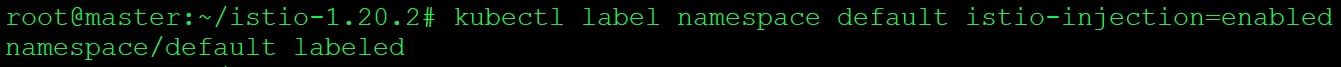
2. Add a namespace label to instruct Istio to automatically inject Envoy sidecar proxies when you deploy your application later.
$ kubectl label namespace default istio-injection=enabled
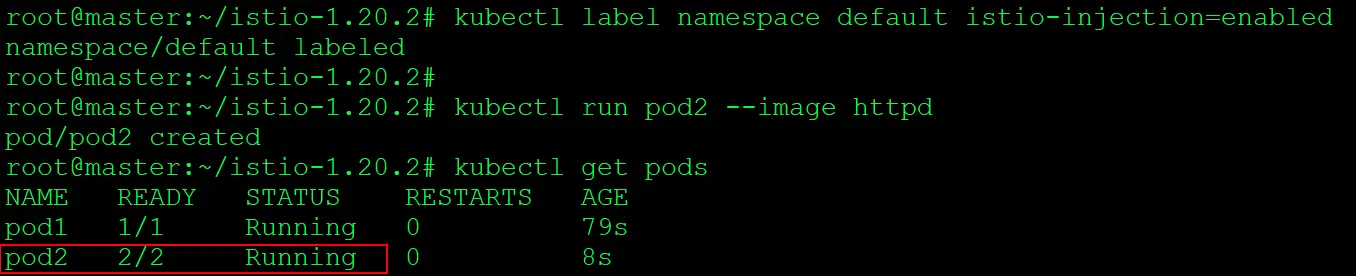
3. Create a pod after adding namespace label
$ kubectl run pod2 --image httpd $ kubectl get pods
4. Describe the pod and check the containers
$ kubectl describe pod pod2
In this pod, we can observe that both the IstioProxy container and another container have been created and are in a ready state.
The IstioProxy container is a component of Istio that runs alongside the application container in each pod. It is responsible for intercepting and managing network traffic between microservices.
The IstioProxy container uses the Envoy proxy to implement features like traffic routing, load balancing, and security policies as defined by Istio’s configuration.
Conclusion
Istio, as a service mesh solution, provides a robust foundation for managing microservices communication. With its advanced features for traffic management, security, and observability, Istio simplifies the complexities associated with microservices architectures. As organizations continue to adopt microservices, understanding and implementing Istio becomes crucial for building scalable, secure, and reliable applications.
Frequently Asked Questions
What is Istio?
Istio is an open-source service mesh platform used to connect, secure, control, and observe microservices across multiple clusters.
What are some common use cases for Istio?
Common use cases for Istio include service discovery, load balancing, A/B testing, canary deployments, blue-green deployments, and enforcing security policies across microservices.
How can Istio be integrated into existing applications?
Istio can be gradually introduced into existing applications by deploying sidecar proxies alongside microservices and gradually enabling Istio features like traffic management and security.
What platforms and environments does Istio support?
Istio supports various platforms including Kubernetes, VMs, and cloud-based environments such as Google Kubernetes Engine (GKE), Amazon EKS, and Microsoft Azure Kubernetes Service (AKS).
How does Istio handle service resiliency?
Istio incorporates features like circuit breaking, retries, and timeouts to improve service resiliency and fault tolerance in distributed systems.
Related/References
- Subscribe to our YouTube channel on “Docker & Kubernetes”
- Kubernetes Architecture | An Introduction to Kubernetes Components
- Create AKS Cluster: A Complete Step-by-Step Guide
- [Solved] The connection to the server localhost:8080 was refused – did you specify the right host or port?
- CKA/CKAD Exam Questions & Answers
- Kubernetes Monitoring: Prometheus Kubernetes & Grafana Overview
Join FREE CLASS Masterclass
Discover the Power of Kubernetes, Docker & DevOps – Join Our Free Masterclass. Unlock the secrets of Kubernetes, Docker, and DevOps in our exclusive, no-cost masterclass. Take the first step towards building highly sought-after skills and securing lucrative job opportunities. Click on the below image to Register Our FREE Masterclass Now!









Leave a Reply