In this blog, I’ll cover some valuable insights, including Q&As and valuable links, from Day 6 of our recent Cloud Security for Azure, AWS, Google Cloud, and Oracle live class, where we discussed Web App, App Services, Containers, Kubernetes, Traffic Manager and others. We also did hands-on on Lab-10 of our 18+ hands-on extensive labs in the live session.
On Day 5 in the previous week, we covered Firewall, Route table, Load balancer, NAT, Application gateway, etc.
So, here are some of the Q&As asked during the Live session from Module 2: Implement Platform protection.
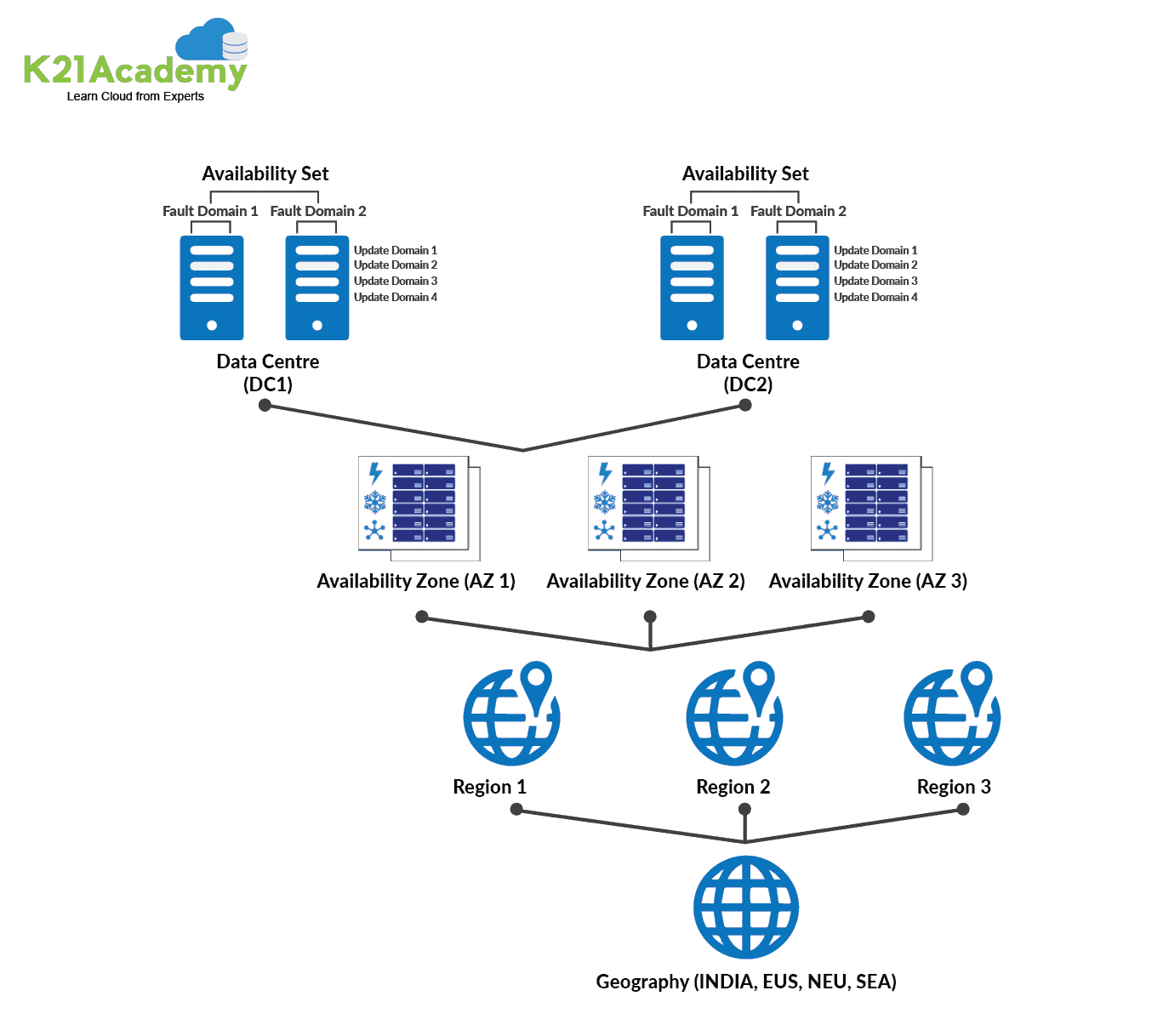
Q1. How to chooses the correct region for your service?
Ans. Each Azure geography has one or more regions and adheres to strict data residency and compliance guidelines. This enables you to keep your mission-critical data and apps close at hand on a fault-tolerant, high-capacity networking architecture. Choose the right Azure region for you based on these three criteria:
- Compliance and data residency
- Service availability
- Pricing
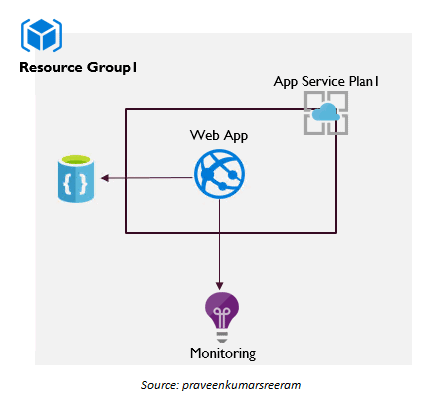
Web Apps or App Service
Azure App Service is an HTTP-based service that allows you to host web applications, REST APIs, and mobile backends. You can code in any language you like, including.NET, Java, Ruby, Node.js, PHP, or Python.
App Service not only adds the security, load balancing, autoscaling, and automated management features of Microsoft Azure to your application. It also has DevOps features, including continuous deployment via Azure DevOps, GitHub, Docker Hub, and other sources, package management, staging environments, custom domains, and TLS/SSL certificates.
You pay for the Azure compute resources you utilise with App Service. The App Service plan on which you run your apps determines the compute resources you consume.
>Know more about Web App
App Service Plan
An App Service plan defines a set of computing resources for a web app to run.
When you create an App Service plan in a specific region (for example, West Europe), that region gets its own set of computer resources. Whatever apps you add to this App Service plan operate on these compute resources, according to your App Service plan’s specifications. Each App Service plan specifies the following:
- Operating System (Windows, Linux)
- Region (West US, East US, etc.)
- Number of VM instances
- Size of VM instances (Small, Medium, Large)
- Pricing tier (Free, Shared, Basic, Standard, Premium, PremiumV2, PremiumV3, Isolated)
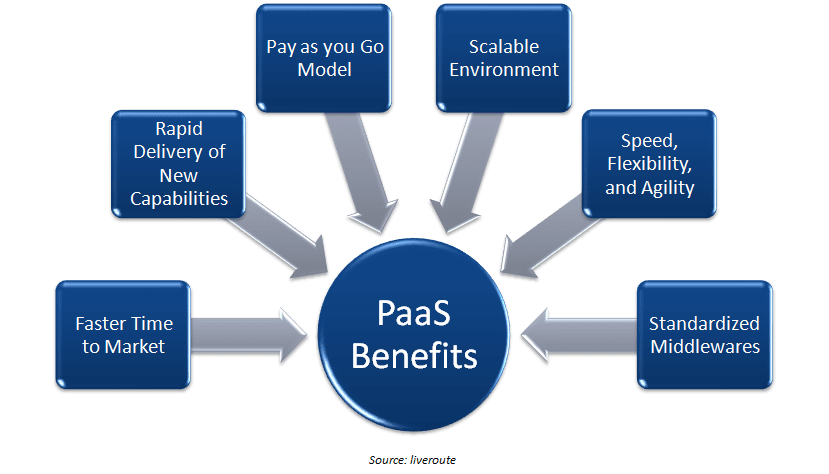
Q2. What are the advantages of PaaS?
Ans. One of the most major advantages of adopting a PaaS is the ability to swiftly create and deploy apps. They will run without the hard lifting required to set up and maintain the environment. With service-level agreements and other guarantees, developers don’t have to worry about tedious and repeated chores like patching and upgrading because a service provider maintains a PaaS. They may be assured that their environment will be highly available and stable, despite the fact that outages sometimes occur.
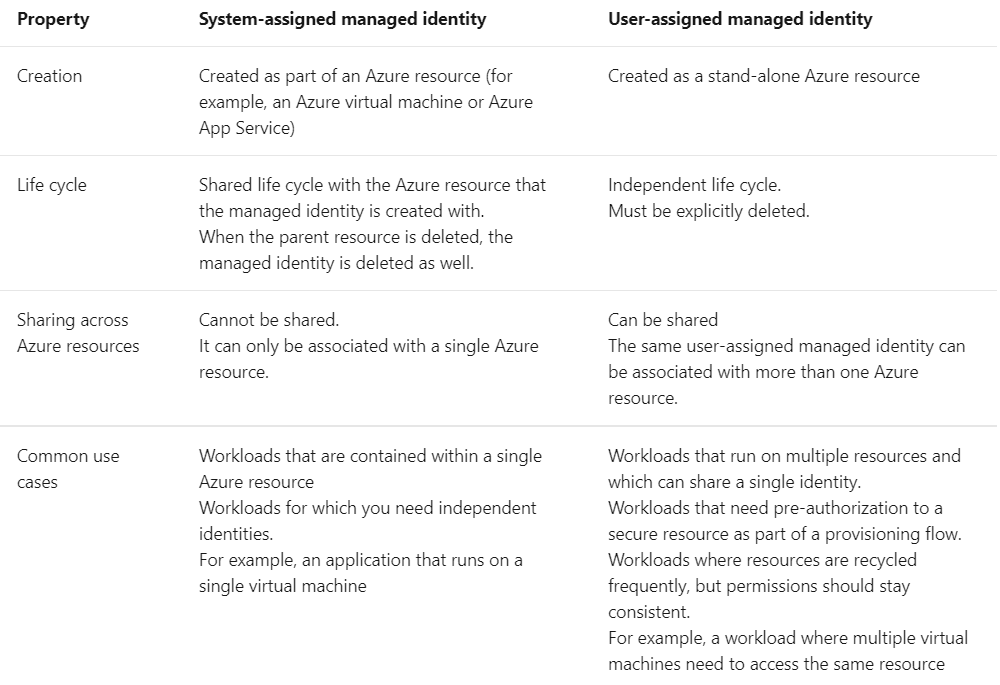
System Assigned Manage Identity
Managed identities eliminate the need for developers to manage credentials. Some of the advantages of adopting Managed Identities are as follows:
- You do not need to keep track of credentials. You don’t even have access to credentials.
- Managed identities can be used to log in to any resource that supports Azure Active Directory authentication, including your own apps.
- It is not necessary to pay more to use managed IDs.
You can enable a managed identity directly on a service instance in some Azure services. When you enable a system-assigned managed identity, an identity in Azure AD is created that is linked to the service instance’s lifecycle. As a result, when you delete the resource, Azure also deletes your identity. By design, this identity can only be used to request tokens from Azure AD by that Azure resource.
The distinctions between the two types of managed identities are shown in the table below:
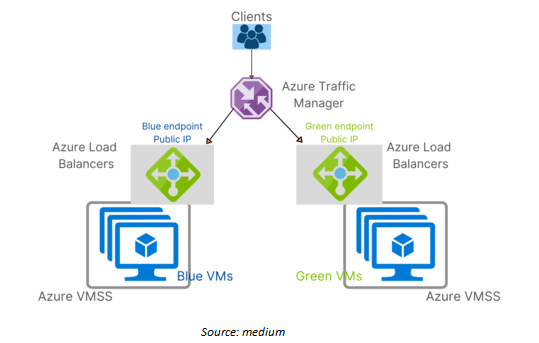
Blue-Green Deployments
The Blue-Green deployment method involves running two identical production environments, Blue and Green, to minimise downtime and risk. Only one of the environments is active at any given moment, with the active environment providing all production traffic.
Common hazards connected with software deployments, such as downtime and rollback capabilities, can be mitigated via Blue-Green deployments. However, there are a variety of ways to implement Blue-Green deployments in Azure, and today we’ll look at how to do so with Azure VMSS, Azure Load Balancers, and Azure Traffic Manager.
>Know more about Blue-Green Deployment
Web Apps Authorization
The process of validating one’s identification is known as authentication. A username or userid is a unique identifier that is connected with a user. To authenticate a user, we traditionally utilise a username and password combination. We’ll name it local authentication because the authentication logic must be maintained locally. We can use OpenID, Oauth, and SAML as Auth providers in addition to local authentication.
There are various ways by which you can authenticate your web application:
- Cookie-Based authentication
- Token-Based authentication
- Third-party access(OAuth, API-token)
- OpenId
- SAML
>Know more about Authentication
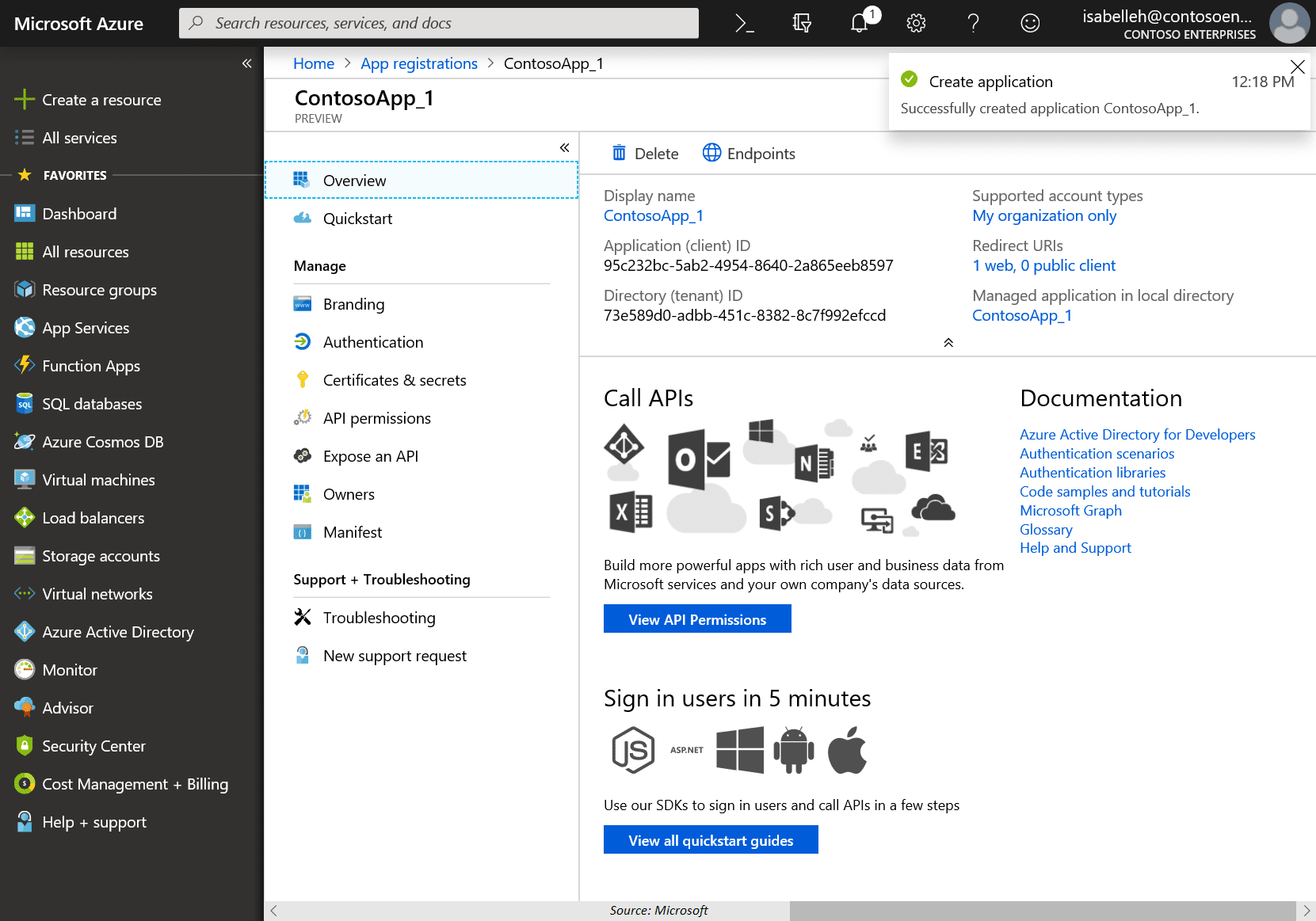
Application Registration
Application registration is the process of adding and registering an app on Azure Portal so that it can be integrated with Microsoft’s identity platform and make use of Microsoft Graph.
Q3. In brief, what do you mean by Application Registration?
- The application registration in your tenant allows you and others to authenticate against your Azure Active Directory.
- A standard application registration can’t do much more than verifying that the user has valid login credentials on its own.
- Another alternative is to use an application secret for authentication. This might be your Active Directory or, in the case of a multi-tenant application, the user’s original directory. If you configure it, users can also use their @outlook.com and @live.com accounts to log in.
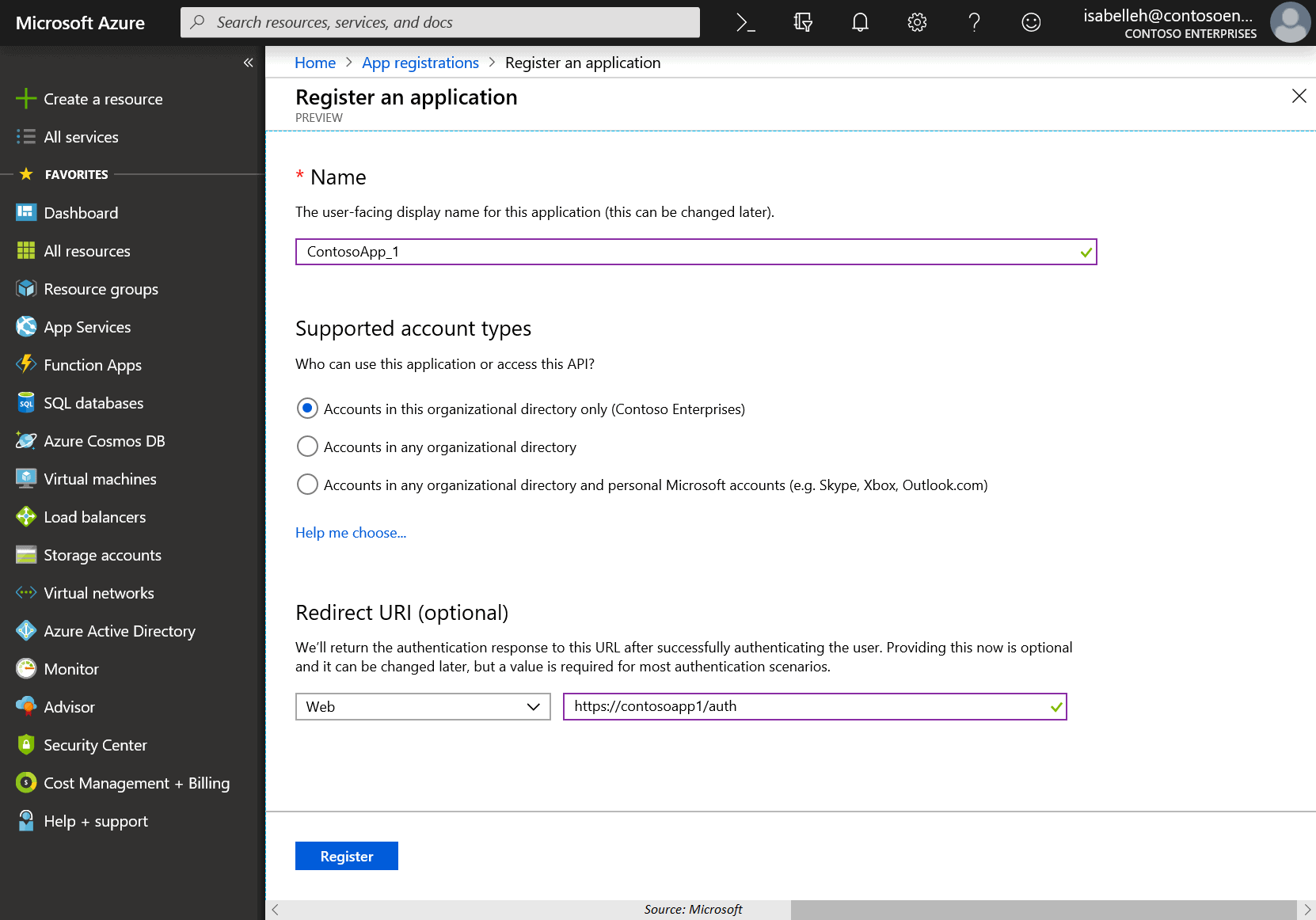
Steps to register an application:
- Sign in to the Azure Portal using either a work or school account or a personal Microsoft account.
- If your account gives you access to more than one tenant, select your account in the top right corner, and set your portal session to the Azure AD tenant that you want.
- In the left-hand navigation pane, select the Azure Active Directory service, and then select App registrations > New registration.
- When the Register an application page appears, enter your application’s registration information:
- Name
- Supported account types
- Redirect URI (optional)
- When finished, select Register.
>For more details click Registration Process
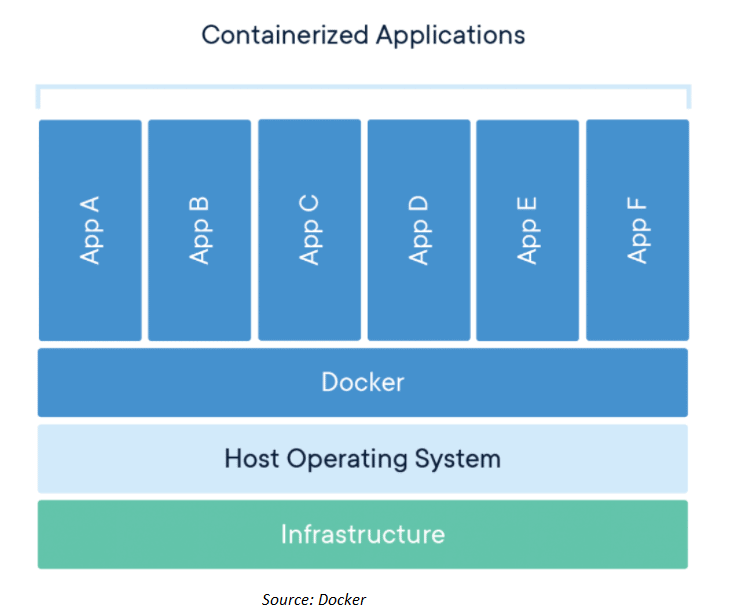
Container
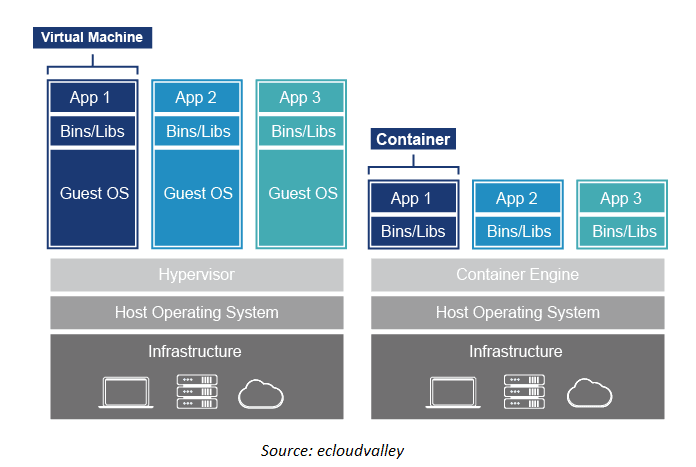
A container is a standard software unit that encapsulates code and all of its dependencies so that the programme can be moved from one computing environment to another fast and reliably.
Containers are a type of virtualization for operating systems. From a small microservice or software process to a huge application, a single container can operate it all. All of the necessary executables, binary code, libraries, and configuration files are contained within a container.
Q4. What is a microservice?
Ans. Microservices are an architectural approach to application development in which each core function or service is designed and deployed separately. Because microservice architecture is dispersed and loosely connected, the failure of one component will not bring the entire app down.
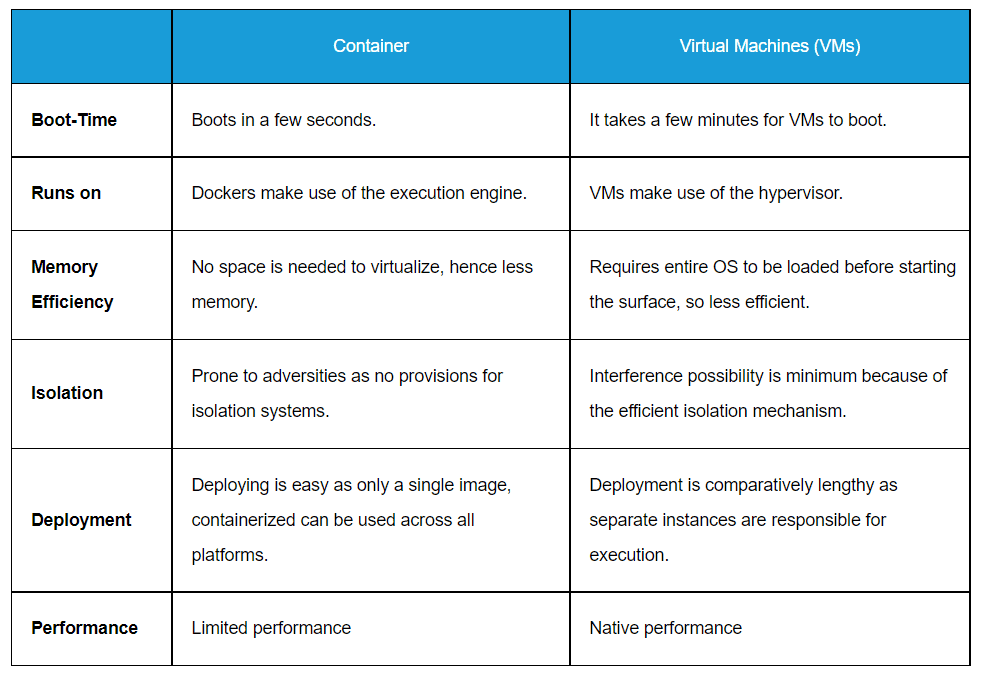
Q5. What is the difference between Virtual Machines and Containers?
Q6. What is a Container Image?
Ans. A container image is a static file that contains executable code and can be used to construct a container on a computer.
Docker Container
Docker is the most popular container. A Docker container image is a small, standalone software package that contains everything needed to run a programme, including code, runtime, system tools, system libraries, and settings.
>Know more about Docker
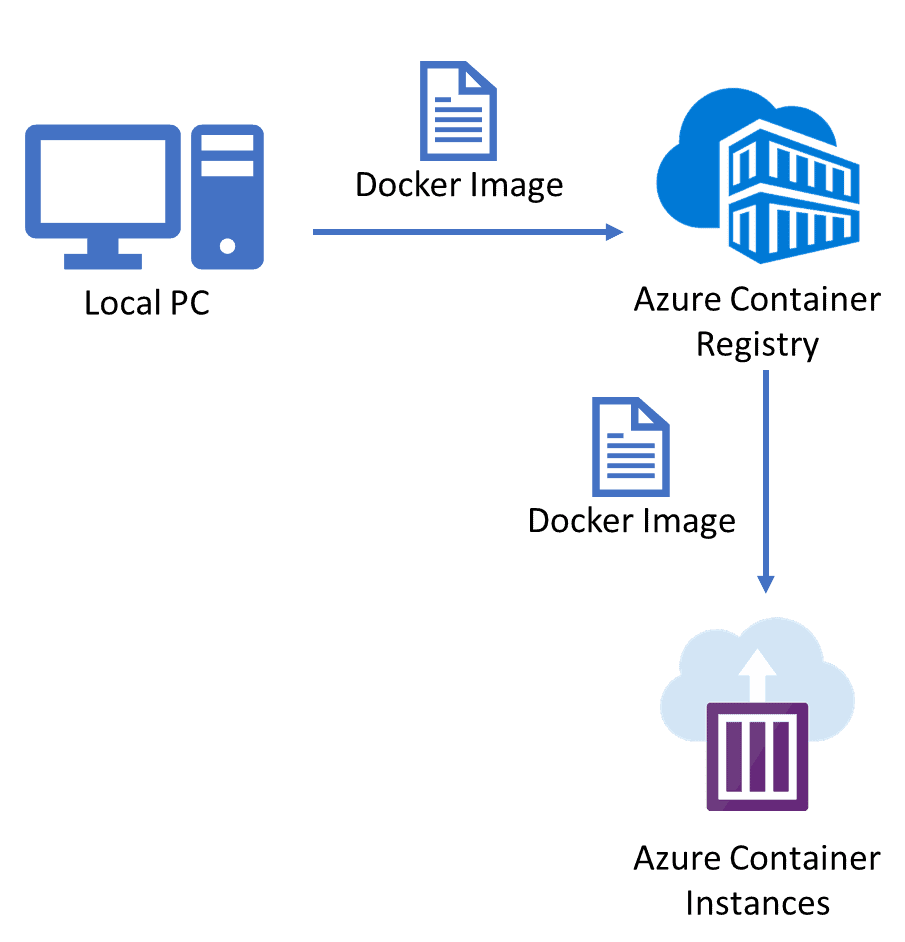
Azure Container Registry (ACR)
Azure Container Registry permits you to create, store, and manage container images in a private registry for all types of container deployments. You can use Azure container registries with your existing container development and deployment pipelines.
Azure Container Instance
ACI (Azure Container Instances) is a managed service that lets you run containers directly on the Microsoft Azure public cloud without the need for virtual machines (VMs).
You don’t need to build underlying infrastructure or use higher-level services to manage containers with Azure Container Instances. Basic features for controlling a group of containers on a host machine are provided by ACI. For more complex activities like coordinated upgrades, service discovery, and automatic scaling, it supports the usage of full container orchestrators like Kubernetes.
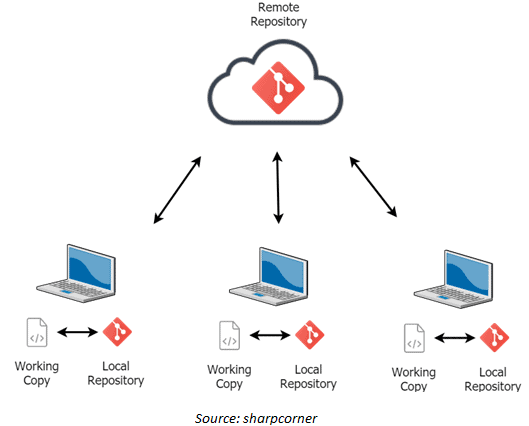
Q7. What is Azure Repository?
Ans. Azure Repos is a collection of version control tools for managing your code. Version control systems are pieces of software that allow you to keep track of changes to your code over time. You tell the version control system to take a snapshot of your files as you edit them. The version control system keeps that snapshot indefinitely, so you may go back to it if necessary.
Azure Kubernetes Service
Kubernetes is an open-source framework for managing containerized workloads and services that allows declarative configuration as well as automation. It has a huge and fast-expanding ecosystem. Services, support, and tools for Kubernetes are widely available.
Azure Kubernetes Service (AKS) offers serverless Kubernetes, an integrated continuous integration and continuous delivery (CI/CD) experience, and enterprise-grade security and governance.
Q8.What is container orchestration?
Ans. Container orchestration automates a lot of the labour that goes into running containerized workloads and services. This covers provisioning, deployment, scaling (up and down), networking, load balancing, and other tasks that software teams must perform to manage a container’s lifespan.
It also offers its own benefits for a containerized environment, including:
- Simplified operations: The most important benefit of container orchestration and the primary reason for its adoption is this. Containers offer a lot of complexity, which can quickly spiral out of control if you don’t use container orchestration to keep track of it.
- Resilience: Container orchestration technologies can restart or scale a container or cluster automatically, increasing resilience.
- Added security: Container orchestration’s automated method reduces or eliminates the risk of human error, which helps make containerized applications secure.
>Know more about Container Orchestration
Azure Traffic Manager
Azure Traffic Manager allows you to regulate the distribution of user traffic by using DNS to direct requests to the most appropriate service endpoint supported on a traffic-routing method and therefore the health of the endpoints.
Azure traffic manager selects an endpoint based on the configured routing method. It supports a variety of traffic-routing methods to suit different application needs. After the selection of endpoints, the client is connected directly to the appropriate service point. It also provides endpoint health checks and automatic failover. It also enables you to build a highly available application that is resilient to failure, including the failure of an entire Azure region.
>Know more about Azure Traffic Manager
What is Azure Front Door?
Microsoft Azure Front Door (AFD) is a service that offers a single global entry point for customers accessing web apps, APIs, content, and cloud services.
We can configure Azure front door service in two ways,
- Configure a backend pool for each website
- Create one backend pool and direct all website traffic to a single backend pool.
It offers services over Web applications, VM, APIs’, Cloud services, Data. Also, it provides a global infrastructure for building, managing, and provide security. It’s a kind of a global load balancer.
Feature of Azure Front Door
- Microsoft Azure provides Azure front door in two ways, first, Azure front door which has normal functions, and another one, Azure front door standard/Premium (in preview) which have integration with DevOps, support analytics, and a high level of security.
- It supports a Modern Content delivery network with built-in security features.
- Syntactic HTTP/HTTPS request in form of GET, HEAD
- Sticky Session Supported
- It can be implemented with a web application firewall (WAF).
- Azure DDOS protection support enables security and protection from cyber-attacks.
Know about Azure Front Door vs. Application Gateway vs. Load Balancer
Quiz Time (Sample Exam Questions)!
With our Cloud Security for Azure, AWS, Google Cloud & Oracle training program, we cover 220+ sample exam questions to help you prepare for the certification like AZ-500.
Check out one of the questions and see if you can crack this…
Ques: Which of the following Azure cloud services offers serverless capabilities?
- Azure Functions
- Azure App Service
- Azure Kubernetes Service (AKS)
- All of the above
The correct answer will be revealed in my next week’s blog.
Here is the answer to the question shared in the previous blog.
Ques: What is the full form of FQDN in Azure Firewall?
- Fully Qualified Destination Name
- Fully Qualified Data Name
- Fully Qualified Domain Name
- Fully Qualified Desired Name
Answer: 3
Explanation: A fully qualified domain name (FQDN) is the complete domain name for a specific computer, or host, on the internet.
Feedback
Related/References
- [Recap] Day 5: Implement Platform Protection In Cloud
- [Recap] Day 4: Implement Platform Protection In Cloud
- Microsoft Azure Secure Network Connectivity: Firewall, DDOS, & NSG
- Microsoft Azure Security Technologies: Step By Step Activity Guides
- Microsoft Azure Security Technologies Certification
Next Task For You
To get more clarity on what to expect in the training program, I recommend you to attend the FREE Class I’m holding this weekend! This FREE class will help you to understand what the training program looks like and give will you a clear vision to plan your career ahead!
Join me in the FREE Session and fast track your success!
Click on the below image and Register for our FREE CLASS Now!






![AWS DevOps [DOP-C02] Professional Step By Step Activity Guides (Hands-On Labs)](https://k21academy.com/wp-content/uploads/2023/02/DOP-C02-1.png)