![]()
Security is critical in the extensive AWS landscape. Understanding the network security tools available to businesses as they migrate their applications and data to the cloud becomes critical. AWS Security Groups and Network Access Control Lists are two fundamental components that play critical roles in this domain.
Let’s dive into the world of AWS network security and explore the nuances between Security Groups (SGs) and Network Access Control Lists (NACLs).
- What is Security Groups
- Network Access Control List (NACL)
- Choosing the Right tool
- Best Practices
- Comparison Between SG and NACL
- Conclusion
- FAQs
AWS Security Groups (SGs)
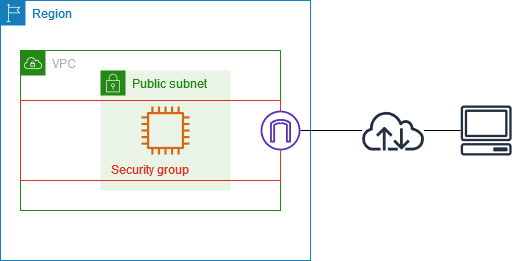
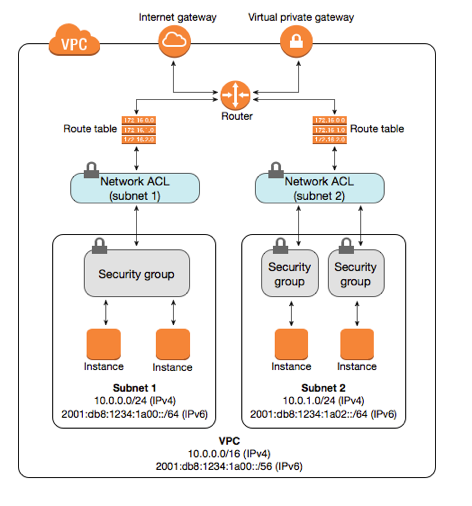
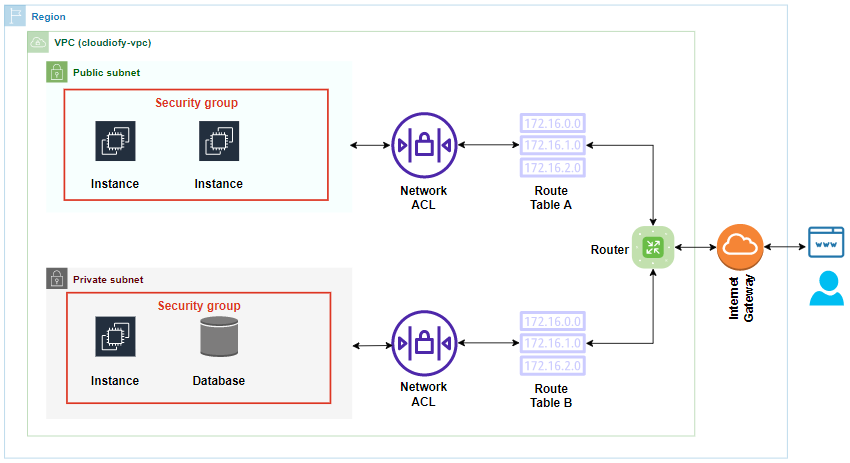
Let’s start with AWS Security Groups, which act as virtual firewalls for your instances to control inbound and outbound traffic. Think of them as the first line of defense, protecting your instances at the instance level.
- Stateful Filtering: One of the key characteristics of AWS Security Groups is stateful filtering. This means that if you allow inbound traffic from a specific IP address, the corresponding outbound traffic is automatically allowed. SGs make it easy to manage and understand the flow of traffic, simplifying rule configurations.
- Instance Level Security: SGs are associated with individual instances, providing a granular level of control. You can specify rules for each instance separately, tailoring the security posture based on the unique requirements of each workload.
- Dynamic Port Configuration: The AWS Security group dynamically adjusts the allowed ports based on the rules you define. This flexibility allows you to adapt your security posture to changes in your application architecture without the need for manual adjustments.
- Easy to Use: SGs are user-friendly and easy to set up. Their simplicity makes them an ideal choice for many scenarios, especially when you need a quick and efficient way to control traffic.
Network Access Control Lists (NACLs)
On the other side of the spectrum, we have Network Access Control Lists, operating at the subnet level. NACLs are an additional layer of security that can be customized to control traffic entering or leaving a subnet.
- Stateless Filtering: Unlike SGs, NACLs operate on a stateless filtering principle. This means that you need to define both inbound and outbound rules separately, as allowing inbound traffic does not automatically permit outbound traffic.
- Subnet Level Security: NACLs provide security at the subnet level, allowing you to define rules that affect all instances within a subnet. This makes them a suitable choice for scenarios where you want to enforce consistent security policies across multiple instances.
- Rule Order Matters: The order of rules in NACLs is crucial. The rules are evaluated based on their order, and the first rule that matches the traffic is applied. This requires careful planning and consideration when setting up rules to avoid unexpected behavior.
- Manual Adjustment Required: Unlike SGs, NACLs don’t dynamically adjust rules based on outbound traffic. If you open a port for inbound traffic, you must explicitly open the corresponding outbound port if needed. This manual configuration can be both an advantage and a challenge, depending on the use case.
Choosing the Right Tool for the Job
Now that we’ve explored the characteristics of SGs and NACLs, the question arises: when to use each?
- Use AWS Security Groups for Instance-Level Security:
- When you need to control traffic at the instance level.
- For stateful filtering, that simplifies rule configurations.
- In scenarios where dynamic port configuration is advantageous.
- Use Network Access Control Lists for Subnet-Level Control:
- When consistent security policies are required across multiple instances in a subnet.
- For scenarios where you need stateless filtering and manual control over inbound and outbound rules.
- When the order of rules and explicit definition of both inbound and outbound traffic are acceptable.
Best Practices
- Defense in Depth: Use Security Groups and NACLs to implement a defense-in-depth strategy. This multi-layered approach enhances security by providing redundancy and mitigating the impact of a single point of failure.
- Least Privilege Principle: Adhere to the principle of least privilege when configuring rules for both SGs and NACLs. Only allow the necessary traffic, reducing the attack surface and potential security risks.
- Regular Audits and Updates: Periodically review and update your security configurations. As your infrastructure evolves, ensure that your SGs and NACLs align with the current requirements and best practices.
Comparison Between SG and NACL
This expanded table offers a more detailed comparison of the key features and characteristics of Security Groups and Network Access Control Lists, helping you make informed decisions based on your specific security requirements in the AWS cloud environment.
| Feature | Security Groups (SGs) | Network Access Control Lists (NACLs) |
|---|---|---|
| Scope of Control | Operate at the instance level, controlling traffic for individual instances | Operate at the subnet level, controlling traffic for all instances within a subnet |
| Filtering Mechanism | Stateful filtering: Automatically allows corresponding outbound traffic | Stateless filtering: Separate rules required for inbound and outbound traffic |
| Flexibility and Dynamism | Dynamically adjust rules based on actual traffic, facilitating easy adaptation to changes | Manual adjustment is required for changes in rules; rules are evaluated based on order, requiring careful planning |
| Association | Associated with individual instances, providing granular control | Associated with subnets, enforcing security policies consistently across multiple instances |
| Rule Order | Rule order is not explicitly defined or critical | Rule order matters; the first matching rule is applied |
| Ease of Use | User-friendly and easy to set up, ideal for scenarios where simplicity is key | It requires careful planning and understanding of rule order and is suited for scenarios where manual control is acceptable |
| Dynamic Port Configuration | Dynamically adjust allowed ports based on defined rules | Manual configuration required for port adjustments |
| Use Cases | Suitable for instance-level security, providing dynamic and adaptive security | Ideal for enforcing consistent security policies across multiple instances in a subnet |
| Redundancy and Defense-in-Depth | Both components contribute to a robust defense mechanism, implementing a defense-in-depth strategy | Implementing a defense-in-depth strategy enhances overall security |
| Audits and Updates | Regular audits and updates are crucial for maintaining security | Regular audits and updates are crucial for maintaining security |
Conclusion
Security Groups and Network Access Control Lists are indispensable tools in the realm of AWS network security, each with its own set of characteristics and use cases. The right tool for the job is determined by your specific needs and the level of control you require. You can architect a robust and secure network infrastructure in the AWS cloud by understanding the strengths and considerations of SGs and NACLs.
Remember that the key is to view SGs and NACLs as complementary components of your overall security strategy rather than mutually exclusive. When used thoughtfully, they form a formidable defense mechanism, protecting your applications and data in the volatile landscape of cloud computing.
Frequently Asked Questions
Is NACL stateful or stateless?
NACLs are stateless, which means that no information about previously sent or received traffic is saved. If you create an NACL rule, for example, to allow specific inbound traffic to a subnet, responses to that traffic are not automatically permitted. This is not how security groups operate.
Is NaCl a firewall?
A network access control list (NACL) is an optional security layer for your VPC that acts as a firewall to control traffic in and out of one or more subnets.
What's the main difference between stateless and stateful?
The Stateless Protocol does not require the server to save server or session information. Stateful Protocol necessitates that the server save the status and session information. There is no tight dependency between server and client in Stateless Protocol. The Stateless protocol design makes server design easier.
How many rules can an AWS security group have?
A security group can contain 60 inbound rules and 60 outbound rules for an account with a default quota of 60 rules. Furthermore, this quota is enforced independently for IPv4 and IPv6 rules.
Related Links/References
- AWS Free Tier Limits
- AWS Free Tier Account Details
- How to create a free tier account in AWS
- AWS Certified Solutions Architect Associate SAA-CO3
- Steps to Connect Windows EC2 Instance
- AWS Free Tier Account Services
- AWS Linux EC2 Instance: All You Need To Know
Next Task For You
Begin your journey towards an AWS Cloud by joining our FREE Informative Class on Amazon Cloud Free Class by clicking on the below image.






![AWS DevOps [DOP-C02] Professional Step By Step Activity Guides (Hands-On Labs)](https://k21academy.com/wp-content/uploads/2023/02/DOP-C02-1.png)