One of the most critical considerations when deploying cloud services is security since you must ensure that the data you store on the Cloud is restricted, regulated, monitored, maintained, and secured to the appropriate degree.
AWS has developed a number of AWS security services and management tools to assist you in protecting your data and environment from undesired exposures, vulnerabilities, and threats, but it is mostly up to us as customers to ensure that these AWS security services are effectively applied.
In this blog, we will discuss AWS Cloud Security and cover topics like:
- Overview of AWS Security
- AWS Compliance
- Why AWS Security & Compliance?
- Benefits of AWS Security
- Essential AWS Security Services
- Shared Security Responsibility Model
- Case Study
- Conclusion
Overview of AWS Security
Security is a critical consideration for anyone looking to expand their cloud footprint. It could be a large corporation, a startup, or a small firm. AWS Security features assist in preventing unauthorized access to your data, accounts, applications, and infrastructure. It enables the development of the most secure cloud infrastructure for managing data flow and encrypts sensitive data. AWS Automation cloud security enables developer and operations teams to safely design and deploy apps more quickly.
AWS Compliance
AWS Compliance enables you to comprehend AWS’s stringent procedures for maintaining cloud security and data protection. In its infrastructure, AWS handles a number of compliance programs. The following is a partial list of assurance services that AWS provides:
- SOC 1/ISAE 3402, SOC 2, SOC 3
- FISMA, DIACAP, and FedRAMP
- PCI DSS Level 1
- ISO 9001, ISO 27001, ISO 27017, ISO 27018
Check Out: How to Set Up MFA for AWS.
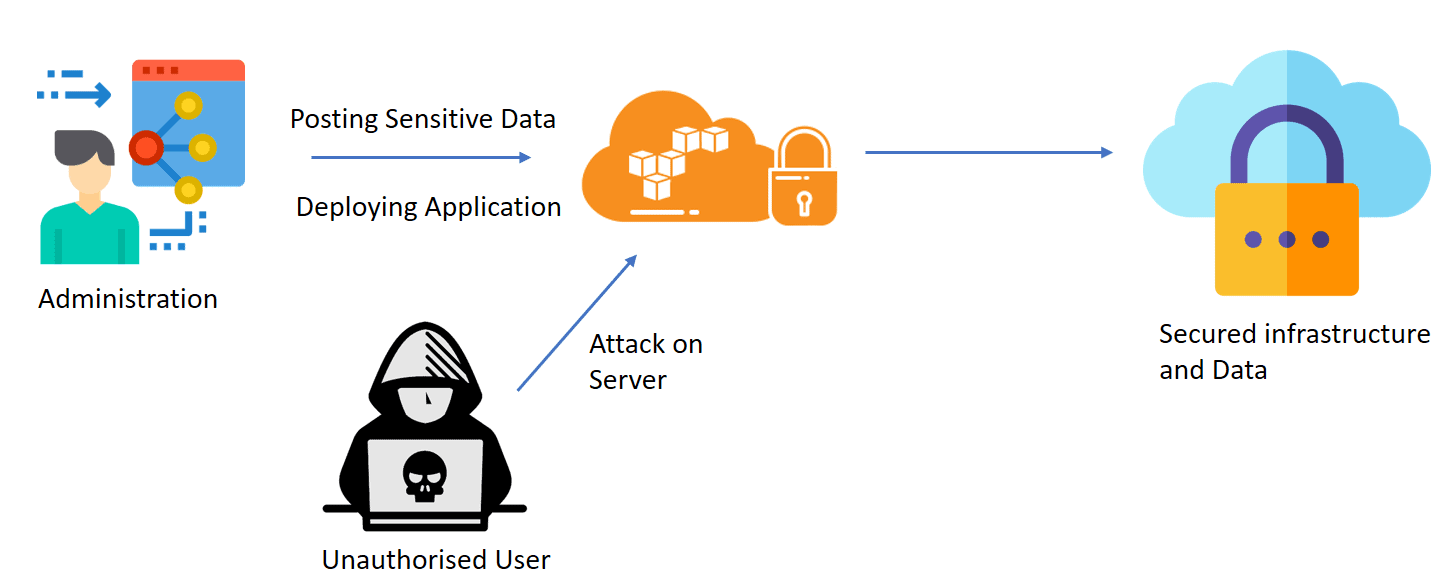
Why Cloud Security & Compliance?
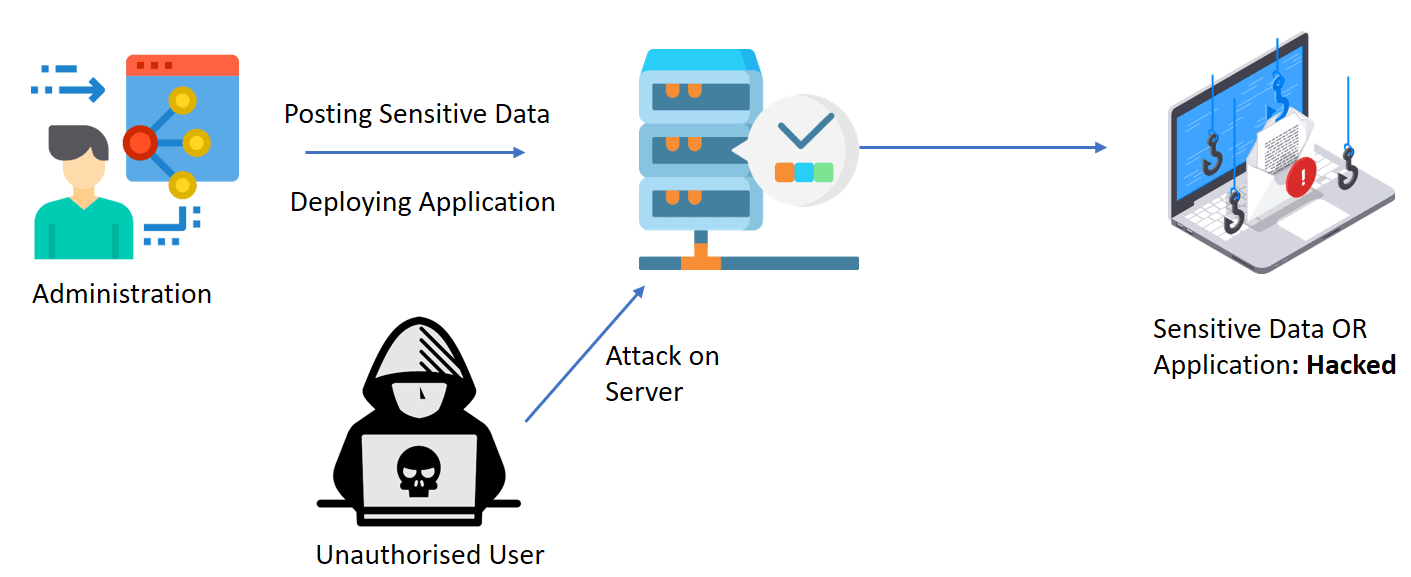
When Dropbox, a cloud-based file-sharing business, reported the hack in 2012, no one understood how catastrophic it was. Over 68 million user accounts, including passwords, were compromised by hackers. Hackers, according to sources, sold stolen passwords on the dark web.
In another case, 6 million LinkedIn user passwords were stolen and published on a Russian forum. LinkedIn adopted two-way authentication in addition to password changes, which worked extremely well. As a result, in order to avoid a large loss of sensitive data, we employ security procedures to create the most secure environment in the cloud.
So security is a big concern for running a business on the cloud. AWS Provides reliable and secure services that help companies to store sensitive data, applications, and authentication more securely.
Also Check: AWS Serverless Application Model.
Benefits of AWS Security Services & Compliance
Security is critical for companies making the transition to the cloud. Cloud computing is no less vulnerable than an on-premise system to security threats continually changing and becoming more sophisticated. For this reason, it is vital to work with a cloud provider that offers best-in-class security that has been customized for your needs.
To know more about AWS for testers.
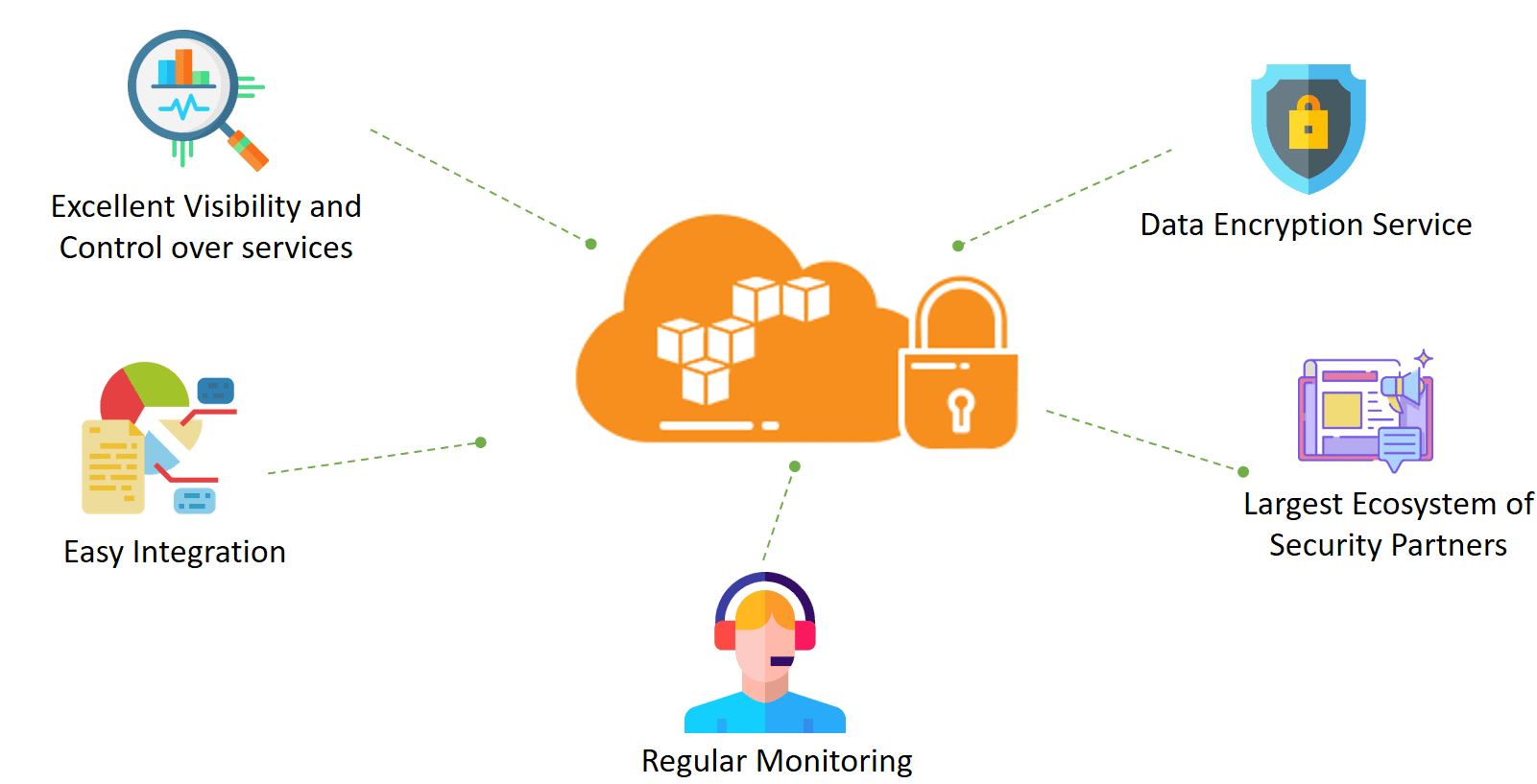
AWS Cloud Security offers various benefits:
Excellent Visibility and Control over services: AWS helps you track stored data with accessibility and resources consumed by your applications. Also, it provides identity and access control, combined with continuous security information monitoring in real-time. It ensures that the right resources have proper suitable access, regardless of where the data is stored.
Easy Integration: By this, you can integrate AWS services with your current solution to help existing workflows, streamline your processes, and simplify compliance reporting.
Regular Monitoring: AWS ensures that they have a world-class team of security experts monitoring services and systems over time to protect your application and data.
Data Encryption Service: Data encryption is just a one-step process in AWS. Key Management service encrypts the data and manages the keys for you.
Largest Ecosystem of Security Partners: Get benefits of AWS security technology by consulting services from familiar solution providers you already know and trust.
Also, Read Our blog post on Blue-Green Deployment.
AWS Security Services & Compliance
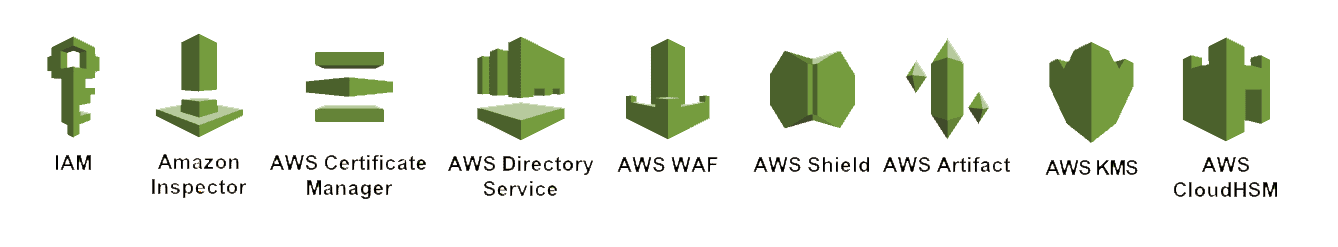
AWS provides services that help protect your sensitive data and accounts from unauthorized access. Let’s have a look at those Essential security services mentioned below.
- Identity & Access Management (IAM): Through the use of identities, permissions, and a set of authentication and authorization methods, IAM allows you to limit who and what can access your AWS resources.
- Amazon Inspector: Amazon Inspector is an automated security assessment service that helps you find security vulnerabilities within EC2 instances. Also, it improves the security and compliance of AWS-hosted applications.
- AWS Certificate Manager: The certificate Manager handles the planning and managing of SSL (Secure Sockets Layer)/TLS(Transport Layer Security ) certificates.
- AWS Directory Service: AWS Directory Service enables directory-aware resources and workloads in your environment to access managed Active Directory (AD). Without the AWS Directory Service, AD and AWS would be isolated to their respective resources and would have to be maintained independently.
- AWS WAF & Shield: The WAF service helps prevent websites and applications from being maliciously attacked by web attack patterns, such as SQL injection and cross-site scripting. The shield protects web applications from Distributed Denial of Service (DDoS) attacks.
- AWS Artifact Portal: Artifact provides on-demand access to security and compliance reports and selects online agreements. Although the following two services do not fall within the same console category as the ones above, these are also critical services for encrypting your data.
- AWS Key Management Service (KMS):Key Management Service allows you to easily regulate access to your data through managed encryption. It is critical to protect sensitive data from unauthorized users. It makes the services extremely accessible while also providing full auditing capabilities to encrypt data at AWS and within your apps.
- AWS Cloud HSM: Hardware Security Module (HSM) is another encryption service that encrypts your data with protected keys. Therefore with this dedicated appliance, you control the HSM’s encryption keys and cryptographic operations.
Also Check Our previous blog post on Amazon API Gateway.
Here are some essential services that we have discussed. Now let’s have a look at AWS
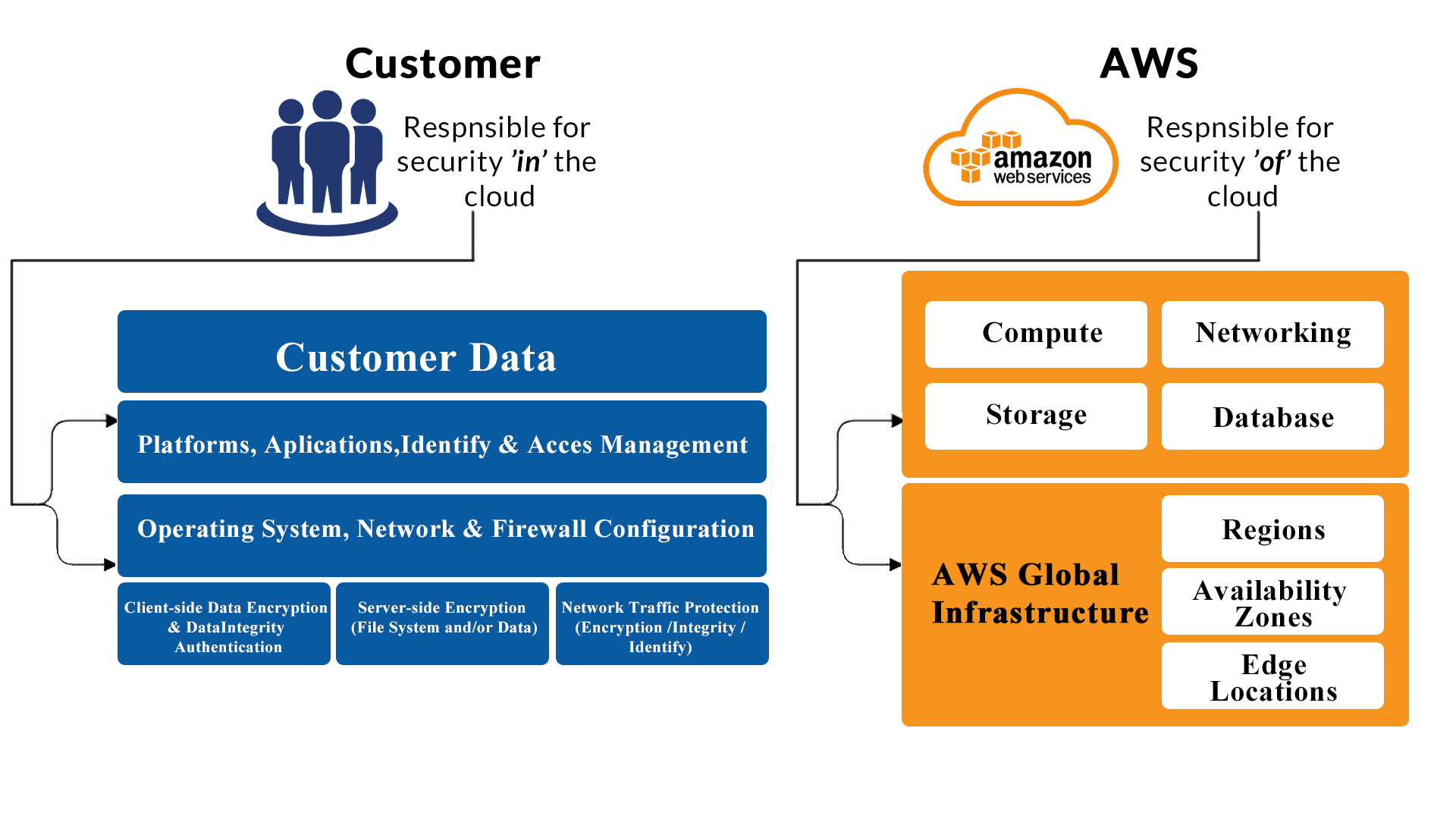
AWS has security rights starting from infrastructure, Regions, and Availability zones. These zones are physical data centers and are a group of 2 or more. In the Shared Security Responsibility Model, AWS is responsible for securing infrastructure, and customers are responsible for anything they put on the cloud or connect to the cloud.
Also Read: Our blog post on AWS Command Line Interface.
AWS Responsibility: For securing the underlying infrastructure, Regions, and Availability Zones.
- Amazon web service is responsible for defending the infrastructure that runs all of the AWS services in the cloud. The infrastructure is involved in physical centers, software, networks, and facilities that run services inside the AWS portal.
- AWS provides several feedback from third-party auditors who have verified their compliance with various compute security standards and regulations.
- AWS is responsible for the security configuration of its products and services like RDS, and DynamoDB.
- For Managed Services, AWS handles basic security tasks like guest OS and database patching, firewall configuration, and disaster recovery.
Customers’ Responsibility
- AWS IaaS products like EC2, VPC, S3, etc., are entirely under your (customer) control and require you to perform all of the necessary security configuration and management tasks.
- Customers are responsible for managing the guest OS, including updates and security patches, application software, and the configuration of the AWS-provided firewall on each instance.
- In most of the AWS services, customers only have to protect the account credentials and configure logical access controls for the resources.
To know more about Amazon AWS DynamoDB.
Case Study
Security is one of the major factors while doing operations on the cloud. AWS services help in Healthcare, Financial Services, Education, Government, and many other fields. Some of them are as follows:
Healthcare
MedStar Health: MedStar Health is a non-profit healthcare organization. It operates more than ten hospitals and 110 other healthcare entities. Using AWS has made it possible to engage their patients more directly—and offer them a reliable and efficient experience.
Financial Services
Intuit®: Intuit Inc. is an American company that concentrates on financial software. Through Intuit’s partnership with AWS, they instantly and frequently provision the servers required to simulate the targeted user traffic.
Many more entities trust AWS to achieve great heights in their journey to the cloud.
Also Read: Cloudtrail vs Cloudwatch, know their significant differences!
Conclusion
A less secure cloud can be the best target for data break by hackers. So, the Security of the cloud is essential in making a cloud successful. AWS security compliance tools play a vital role in improving your cloud security in all possible ways. This blog covered the most important points on AWS Security and compliance, its importance, and its benefits.
Related Links/References
- Overview of Amazon Web Services & Concepts
- How to Create a free tier Account in AWS
- AWS Management Console Walkthrough
- Top 6 AWS Training Courses & Certifications
- AWS Certified Solutions Architect Associate SAA-C03 Exam details
- Amazon S3 Bucket: Overview, Errors & Resolutions
- AWS Outposts: Overview, Working, Features & Use Cases
Next Task For You
Begin your journey towards an AWS Cloud by joining our FREE Informative Class on Amazon Cloud Free Class by clicking on the below image.








![AWS AI Services: Complete List of AI, ML & GenAI Tools with Use Cases [2026]](https://k21academy.com/wp-content/uploads/2024/09/AWS-AI-1.png)
![AWS DevOps [DOP-C02] Professional Step By Step Activity Guides (Hands-On Labs)](https://k21academy.com/wp-content/uploads/2023/02/DOP-C02-1.png)