This post covers how to Configure Multi-Factor Authentication (MFA) with Oracle Identity Cloud Services (IDCS).
If you Don’t know What is Identity Cloud Service (IDCS)? then I would highly recommend you to check my previous post on Oracle Identity Cloud Service (IDCS) Overview & Concepts
Introduction
Multi-Factor Authentication (MFA) is a method of authentication that requires the use of more than one factor to verify a user’s identity.
With MFA enabled in Oracle Identity Cloud Service, when a user signs in to an application, they are prompted for their username and password, which is the first factor – something that they know. The user is then required to provide a second type of verification. This is called 2-Step Verification. The two factors work together to add an additional layer of security by using either additional information or a second device to verify the user’s identity and complete the login process.
Why Use MFA?
Users are increasingly connected, accessing their accounts and applications from anywhere. As an administrator, when you add MFA on top of the traditional username and password, that helps you to protect access to data and applications. This also reduces the likelihood of online identity theft and fraud, which secures your business applications even if an account password is compromised.
MFA Factors
As of August 2018 update, MFA supports Six factors:
- Security Questions: prompts the user to answer security questions to verify their identity. After the user enters their username and password, he must provide answers to a defined number of security questions.
- Mobile App One-Time Passwords: User has Oracle Mobile Authenticator (OMA) App installed in his device to generate a One-Time Password (OTP). A new OTP is typically generated every 30 seconds and is valid for 90-180 seconds. After the user enters his username and password he is prompted to enter the OTP generated by the Oracle Mobile Authenticator app.
- Mobile App Notification: IDCS sends a push notification that contains an approval request to allow or deny a login attempt. After the user provides his username and password, a login requests us sent to his phone. The user taps ‘Allow’ to authenticate.
- Text Message (SMS): IDCS sends a passcode as a text message (SMS) to the user phone. This method is useful for users with limited connectivity. After the user enters his username and password, a passcode is sent to their device to use as a second authentication factor.
- Bypass Code: When enrolling users can generate a bypass code and save for later use. User-generated bypass codes never expire, but can be only used once. Users also have the option to contact an administrator to request a bypass code for access.
- Email: Send a one-time passcode in an email to the user. After the user selects Email as the authentication method, Oracle Identity Cloud Service sends a one-time passcode to the user’s primary email address for use as a second verification method. The user’s primary email address is defined in the user’s Oracle Identity Cloud Service account.
Configure MFA
1. Select MFA Factors
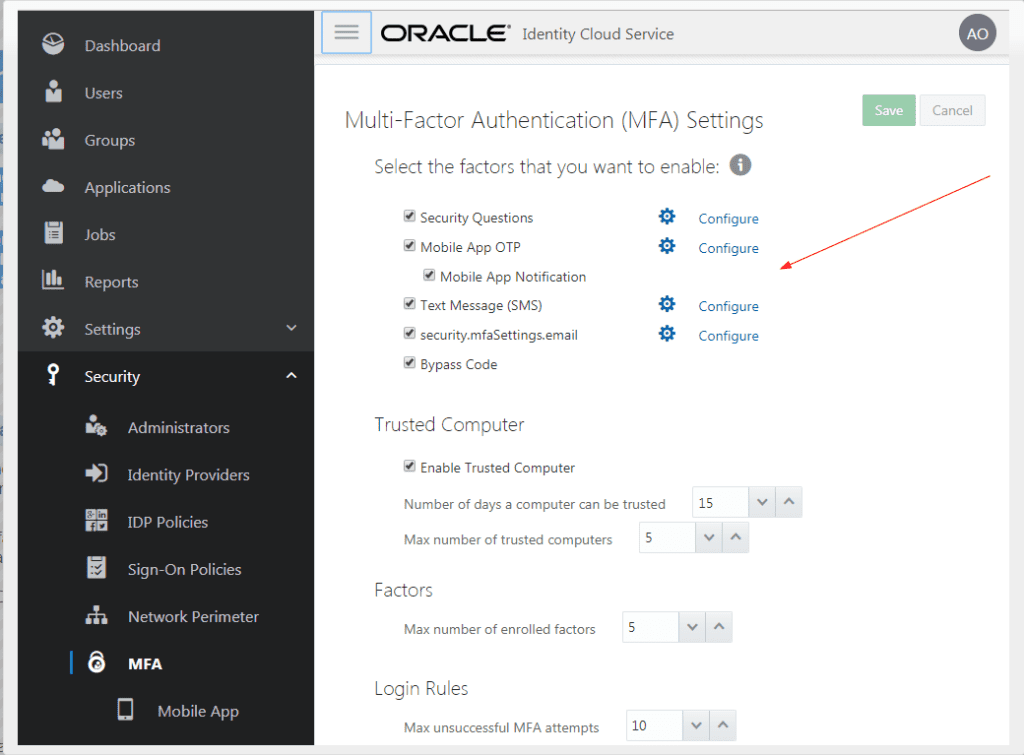
- In the Identity Cloud Service console, expand the Navigation Drawer, click Security, and then MFA.
- Select the factors that you want to enable for your users: Security Questions, Mobile App OTP, Mobile App Notification, Text Message (SMS), Email, and Bypass Code.
- Click Save.
2. Create a Sign-On Rule for MFA
- In the Identity Cloud Service console, expand the Navigation Drawer, click Security, and then Sign-On Policies.
- Oracle Identity Cloud Service provides a default sign-on policy, which allows you to define criteria that Oracle Identity Cloud Service uses to determine whether to allow a user to sign in or to prevent a user from accessing Oracle Identity Cloud Service.
- Click the Default Sign-On Policy.
- Click the Sign-On Rules tab, and then click Add.
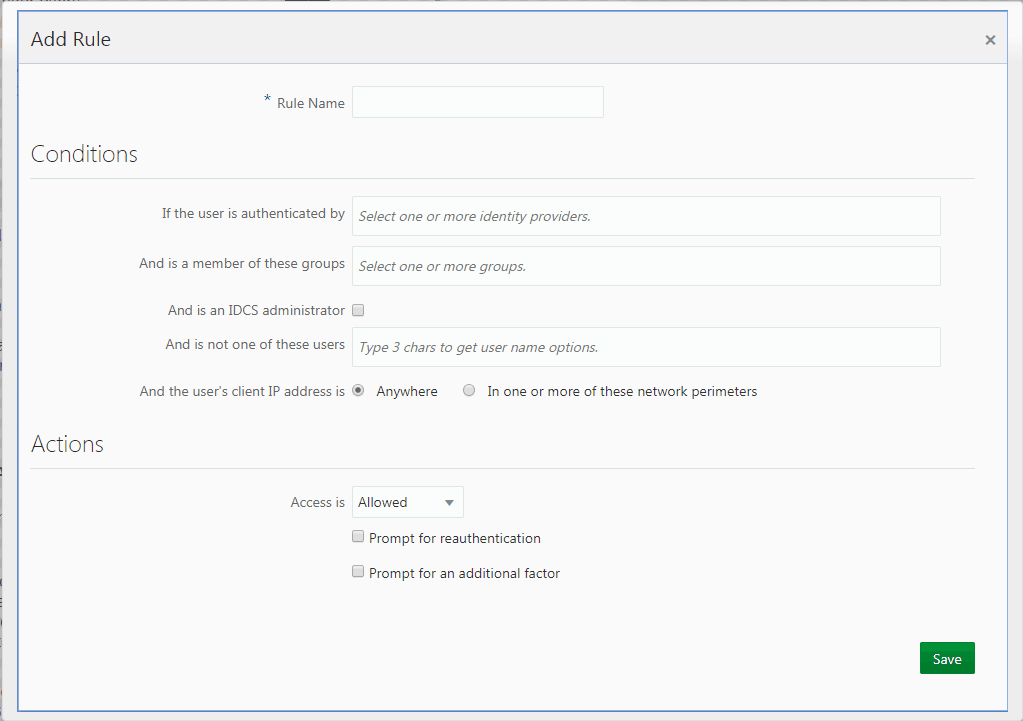
- In the Add Rule dialog box, name the rule, and then define conditions in the Conditions section.
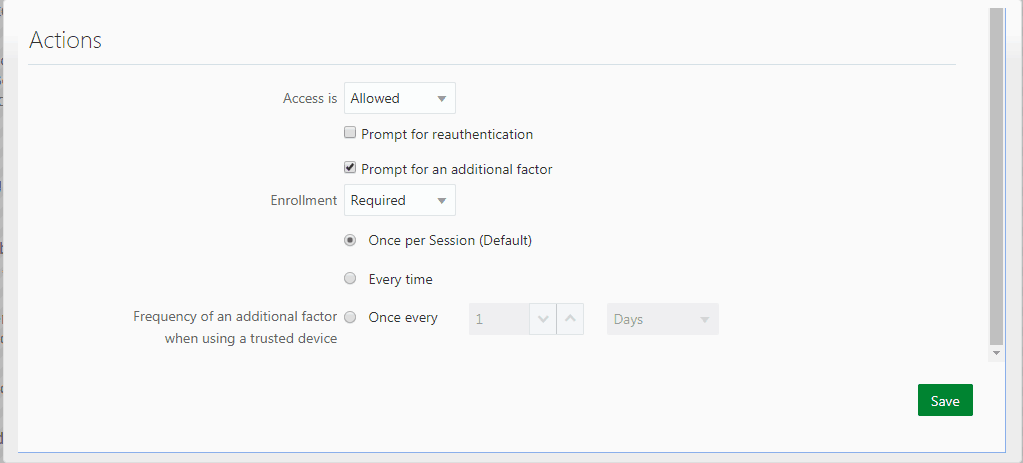
- In the Actions section of the dialog box, select Prompt for an additional factor. Additional MFA settings appear for specifying whether the user is required to enroll in MFA and how often this additional factor is to be used to log in to Oracle Identity Cloud Service
- Note: You must have selected at least one factor for MFA on the Multi-Factor Authentication (MFA) Settings page in Oracle Identity Cloud Service for the additional MFA fields to appear in the Add Rule window.
- Select Required to force the user to enroll in MFA. Select Optional to give a user the option of skipping MFA enrollment.
- Define the frequency that you want a user to be prompted for an additional factor when logging in using a trusted device.
- Once per Session (Default) requires a user to provide a second factor when they log in for each session that they open.
- Every time requires a user to provide a second factor each time that they log in.
- Once every defines how often a user provides a second factor when they log in.
- Click Save.
3. Configure Other MFA Settings
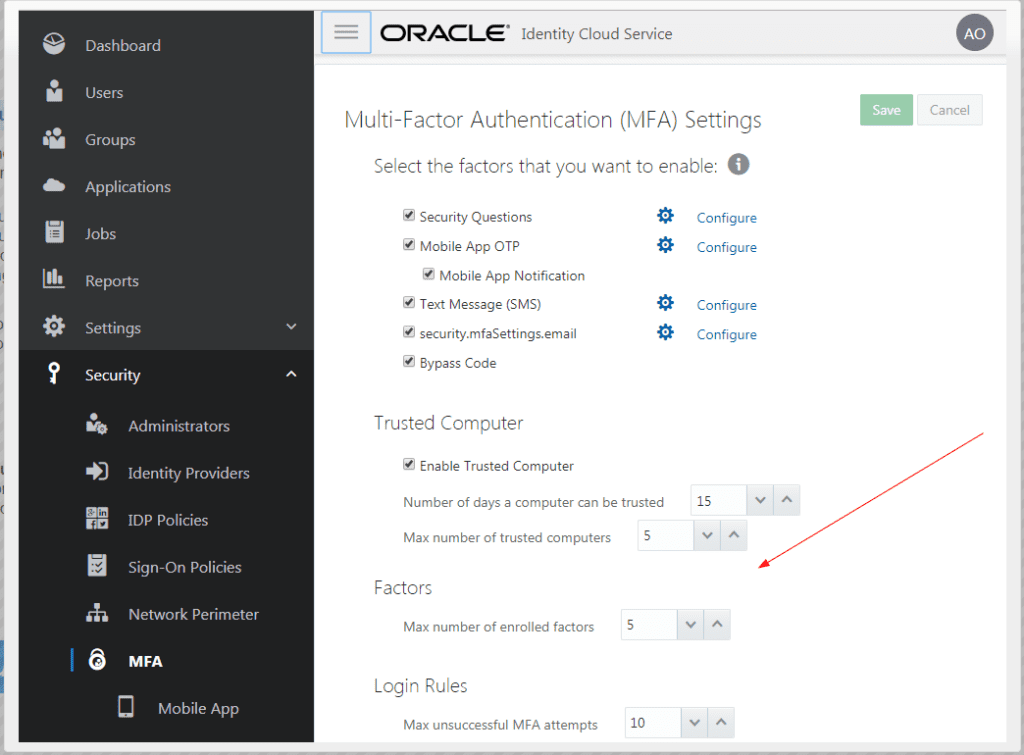
- In the Identity Cloud Service console, expand the Navigation Drawer, click Security, and then MFA.
- Select Enable Trusted Computer when you want to provide users the option to mark their computer and other devices as trusted during login, and then update the trusted computer and device policy criteria according to your requirements.
Trusted devices don’t require the user to provide secondary authentication each time that they sign in (for a defined time period). - Enter the maximum number of factors (Max number of enrolled factors) that a user can enroll in.
- Select the maximum number of times (Max unsuccessful MFA attempts) that a user can provide incorrect verification using their MFA factor before they are locked out of their account.
- Click Save.
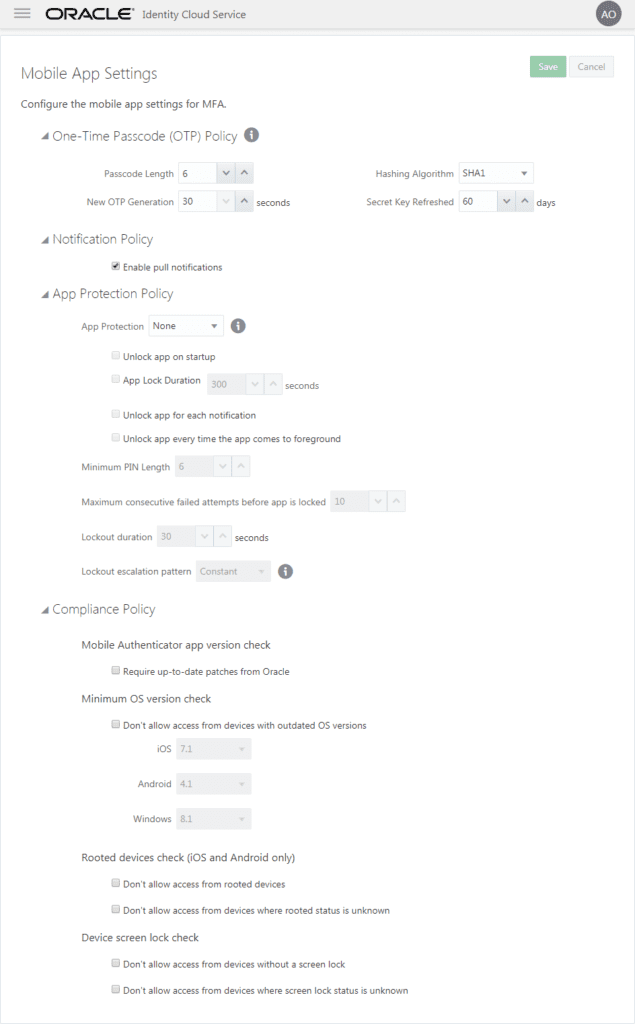
4. Configure Mobile OTP and Notifications
- In the Identity Cloud Service console, expand the Navigation Drawer, click Security, and then MFA.
- Access the Mobile App Settings page by either clicking Configure next to the Mobile App OTP checkbox or by selecting Mobile App from the Navigation Drawer.
- The default values for the One-Time Passcode (OTP) Policy fields are the industry-recommended settings. Leave the defaults or update these fields according to your requirements.
- Select which protection policy that you want to enforce on the Oracle Mobile Authenticator (OMA) app: App PIN or Fingerprint. Leave the default of None if you do not want to enforce a protection policy.
- Define the app protection policy criteria according to your requirements.
- Configure your compliance policy requirements such as which operating systems and which versions are allowed, detecting a rooted device, and whether a device must use the screen lock.
- Click Save.
Similarly, you can also configure another MFA factor’s as well such as Security Questions, Configure Text Message (SMS).
Please stay tuned for our future post on Oracle Cloud Identity Service, where we will be covering advanced concepts such as SAML, OAuth, SSO etc
This post is from our Oracle Identity Cloud Service (IDCS) training in which we have covered everything one should know about Oracle Identity Cloud Service
If you have any doubts please reach out to us at contact@k21academy.com
Next Task for You
Download our 7 Docs free Guide to become Expert in Oracle Identity Cloud Service(IDCS) for Security & Identity Administrator.
Click on Below image to download the guide:



You have described a detail Configuring Multi-Factor Authentication (MFA).
step by step made this article great.
Hi Mike,
Glad to hear from you, that you like the post.
Thanks & Regards,
Rohit
Hello Rohit, Such a very useful article. Very interesting to read this. I would like to thank you for the efforts you had made for writing this awesome article.
Hi Swetha,
Glad that you like the blog, please let us if you have any doubts about IDCS.
Thanks & Regards,
Rohit
Is there any possibility of first authentication against OID(after enabling the OAM/OID federation with IDCS) and second factor authentication with IDCS?