![]()
This blog post will go through some quick tips including Q/A and related blog posts on the topics that we covered in the Google Cloud Training (GCP) Day 3 Live Session which will help you gain a better understanding and make it easier for you to
On our Day 3 Live Session of the Training Program, we covered the concepts of Cloud IAM, Policies, Resource Hierarchy, Service Accounts, Roles, etc.
The previous week, In Day 2 session, we got an overview of concepts of Virtual Machines, Compute Engine, Images and Snapshots, Virtual networks, VPC, subnets, routing, etc.
>Google Cloud IAM
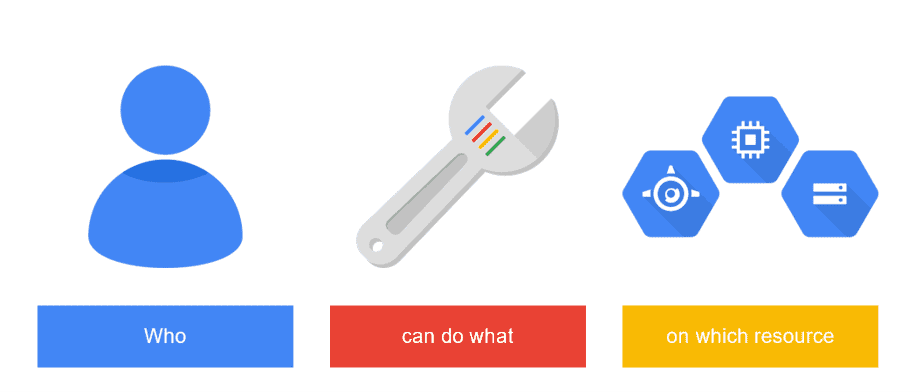
Google Identity and Access Management is a web service that gives cloud administrators the authority to decide who can take a particular action on a particular resource.
In simple words, IAM lets one decide who (Identity) has what role (Access) to which resource.
Q1: What are the security aspects offered by the cloud?
Ans: Some of the important security aspects that the cloud offers are as below:
- Access control: it offers control to the users who can control access to other users who are entering the cloud ecosystem
- Identity management: this provides the authorization for the application services
- Authorization and Authentication: this security feature lets only the authenticated and authorized users access the applications and data
Q2: Which of the Google Cloud services support IAM?
Ans: All Google Cloud services use IAM to make sure that only authorized identities can access them. In addition, some services provide IAM roles specific to their services or support, granting access at the resource level.
>Authentciation, Authorization & MFA
Authentication refers to giving access to only the right accounts (user accounts or service accounts) whereas Authorization lets you decide what permission to give to each authenticated account.
Multi-Factor Authentication (MFA) is an increasingly common tool in cloud security that relies on having a 2 step process instead of a single sign-in. The two components are usually something the user knows (like a password), and something the user has (physical key/access code). This is used so that even if the password is somehow compromised, the data is protected.
Q3: Can I use IAM policies to manage both authentication and authorization for my applications?
Ans: Use IAM to manage authorization to Google Cloud resources. To manage user authentication, use whatever methods you use to manage them today, for example, LDAP, Google groups, etc. Using IAM, you can grant access to a Google account, a service account, a Google group, a Cloud Identity domain, or a Google Workspace domain.
Q4: How can I use Multi-Factor Authentication (MFA) with IAM?
Ans: When individual users use MFA, the methods they authenticate with will be honored. This means that your own identity system needs to support MFA. For Google Workspace accounts, this needs to be enabled by the user themselves. For Google Workspace-managed credentials, MFA can be enabled with Google Workspace tools.
Check Out: Best Way to learn GCP.
>Cloud IAM Components
Cloud IAM has three main parts:
- Member: A member can be a Google Account, a service account, a Google group, or a Google Workspace or Cloud Identity domain that can access a resource.
- Role: A role is a collection of permissions that determine what operations are allowed on a resource.
- Policy: The IAM policy collects role bindings that bind one or more members to individual roles.
Q5: What are members in Cloud IAM?
Ans: A member can be a Google Account (for end-users), a service account (for apps and virtual machines), a Google group, or a Google Workspace or Cloud Identity domain that can access a resource. The identity of a member is an email address associated with a user, service account, or Google group; or a domain name associated with Google Workspace or Cloud Identity domains.
Types of Member Accounts
In IAM, you grant access to members which can be of the following types:
- Google Account – Represents a developer, administrator, or any other person who interacts with GCP
- Service Account – Belongs to your application instead of an individual end-user
- Google Group – Named collection of Google accounts and Service accounts Each group has a unique email address Efficient way to apply access policies Don’t have login credentials
- Google Workspace domain
- Cloud Identity domain
- All authenticated users
- All users
Q6: How do I grant permissions to resources in my project to someone who is not a member of my organization?
Ans: Google groups are used to add a user outside of your organization to a group and bind that group to the role. Note that Google groups don’t have login credentials, and you cannot use Google groups to establish identity to make a request to access a resource.
You can also directly add the user to the IAM policy even if they are not a part of your organization. However, check with your administrator if this is compliant with your company’s policy.
Q7: What is G-Suite & Identity Domain?
Ans: A Google Workspace(also known as G-Suite) domain represents a virtual group of all the Google Accounts that have been created in an organization’s Google Workspace account. Google Workspace domains represent your organization’s internet domain name (such as example.com), and when you add a user to your Google Workspace domain, a new Google Account is created for the user inside this virtual group (such as username@example.com).
A Cloud Identity domain is like a Google Workspace domain because it represents a virtual group of all Google Accounts in an organization. However, Cloud Identity domain users don’t have access to Google Workspace applications and features.
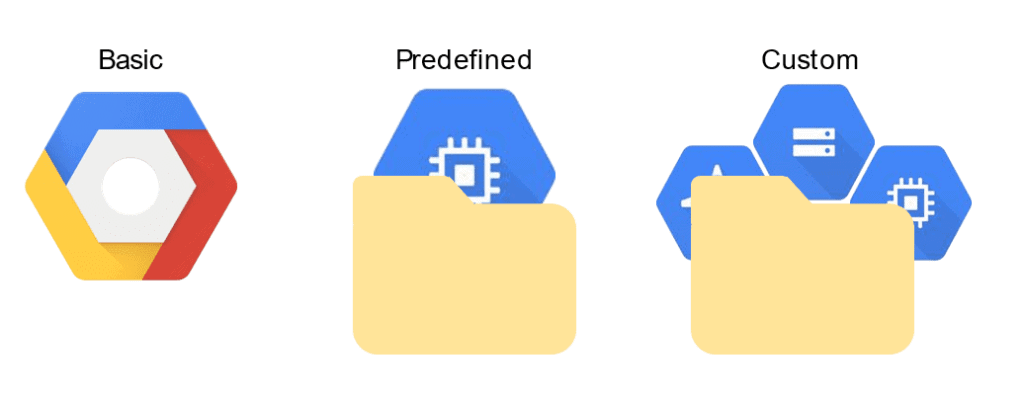
>IAM Roles
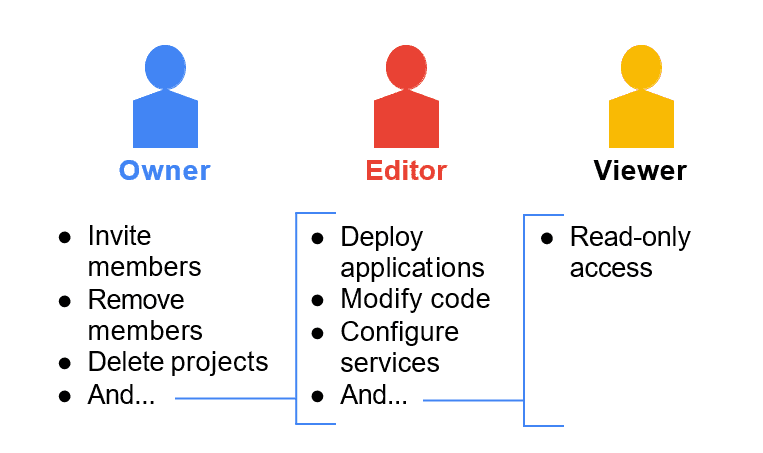
This is one of the most important topics in the Google Cloud Architect training. A role in IAM is an entity that defines a set of permissions, which are to be granted to selected users. There are three types of roles in Google IAM:
- Primitive/Basic Roles: It includes the Owner, Editor, and Viewer roles that existed before the introduction of IAM.
- Predefined Roles: These provide granular access for a specific service and are managed by Google Cloud.
- Custom Roles: These provide granular access according to a user-specified list of permissions.
Q8: What is the difference between basic roles and predefined roles?
Ans. Basic roles are the legacy Owner, Editor, and Viewer roles. IAM provides predefined roles, which enable more granular access than the basic roles.
Q9: If a company wants to have a Google Cloud Account, is it necessary that the organization admin must be one of their employees?
Ans: Yes, to manage access to various resources, the admin must be an employee of the concerned company. These Organization admins are responsible for granting roles to the employees as per the need, which controls what permissions they have.
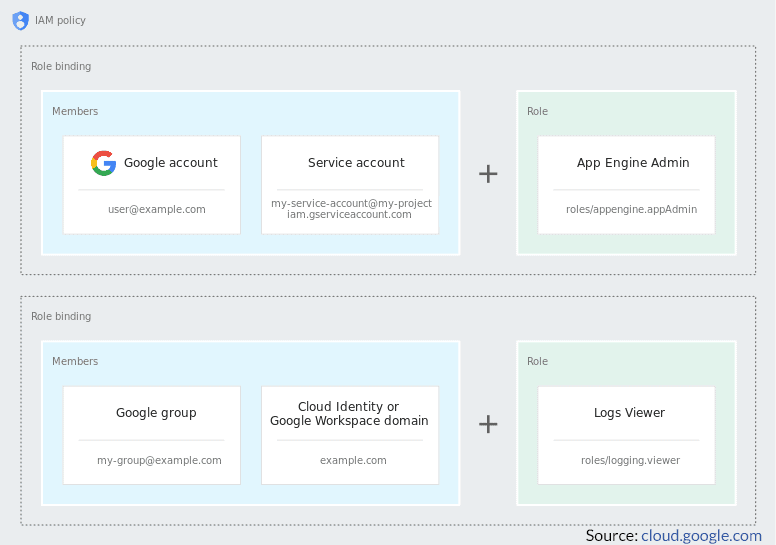
>IAM Policy
IAM policy is a collection of statements that define who has what type of access. A policy is attached to a resource and is used to enforce access control whenever that resource is accessed.
Q10: What does an IAM Policy look like?
Ans: An IAM policy is represented by a policy object that consists of a list of bindings. A Binding binds a list of members to a role. This can be represented in code as shown in this example code snippet:
{
"bindings": [
{
"role" : "roles/owner",
"members": [
"user:jiwoo@example.com",
"group:admins@example.com",
"domain:google.com",
'serviceAccount:my-other-app@appspot.gserviceaccount.com" ]
},
{
"role": "roles/compute.networkViewer",
"members": ["user:luis@example.com" ]
}
]
}
Q11: What is the relationship between a role and a policy?
Ans: Permissions determine what operations are allowed on a resource. In the IAM world, permissions are represented in the form of . . , for example, compute.instances.get. A role is a collection of permissions. You cannot assign permission to the user directly; instead, you grant them a role. When you grant a role to a user, you grant them all the permissions that the role contains. IAM lets you control who (users) has what (roles) permission to which resources by setting IAM policies. An IAM policy on a resource is the full list of roles granted to members on the resource.
Q12: How can I find out what roles are granted on a resource?
Ans: You can find out what roles are granted on a resource using the Cloud Console, the getIamPolicy() method, or the gcloud command-line tool.
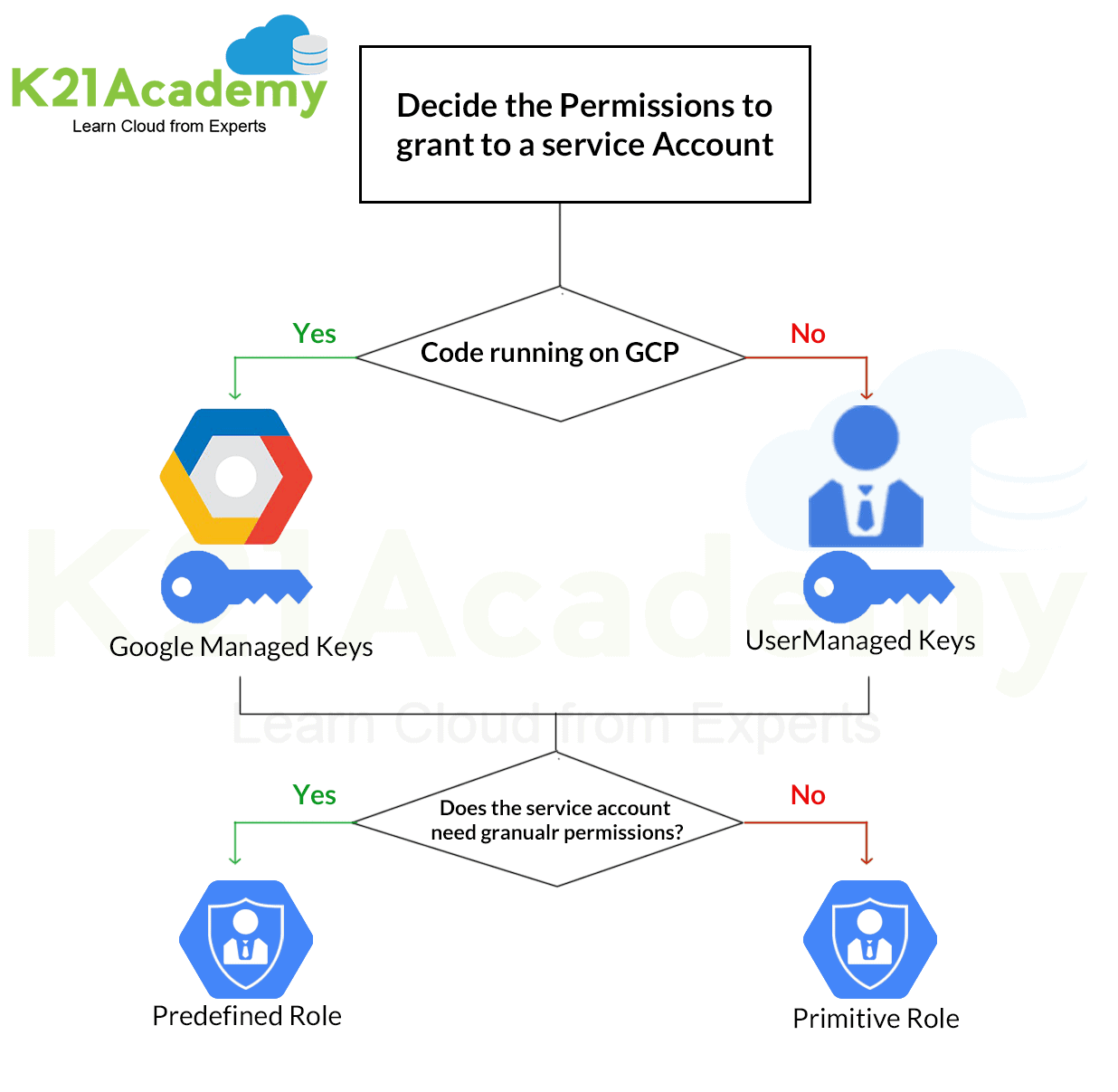
>Service Accounts
A service account is a special account used by an application or a virtual machine instance, not a person. Applications use service accounts to make authorized API calls, authorized as either the service account or as Google Workspace or Cloud Identity users through domain-wide delegation.
Q13: How does a service account differ from a user who uses IAM?
Ans: A service account is a special Google account used by applications to access Google services programmatically. This account belongs to your application or a virtual machine (VM) instead of an individual end-user. Your application uses the service account to call the Google API of service, not to be directly involved.
Q14: What is the maximum number of service accounts I can have in a project?
Ans: By default, you can create up to 100 service accounts in a project. If you need to create additional service accounts in a project, you can request a quota increase.
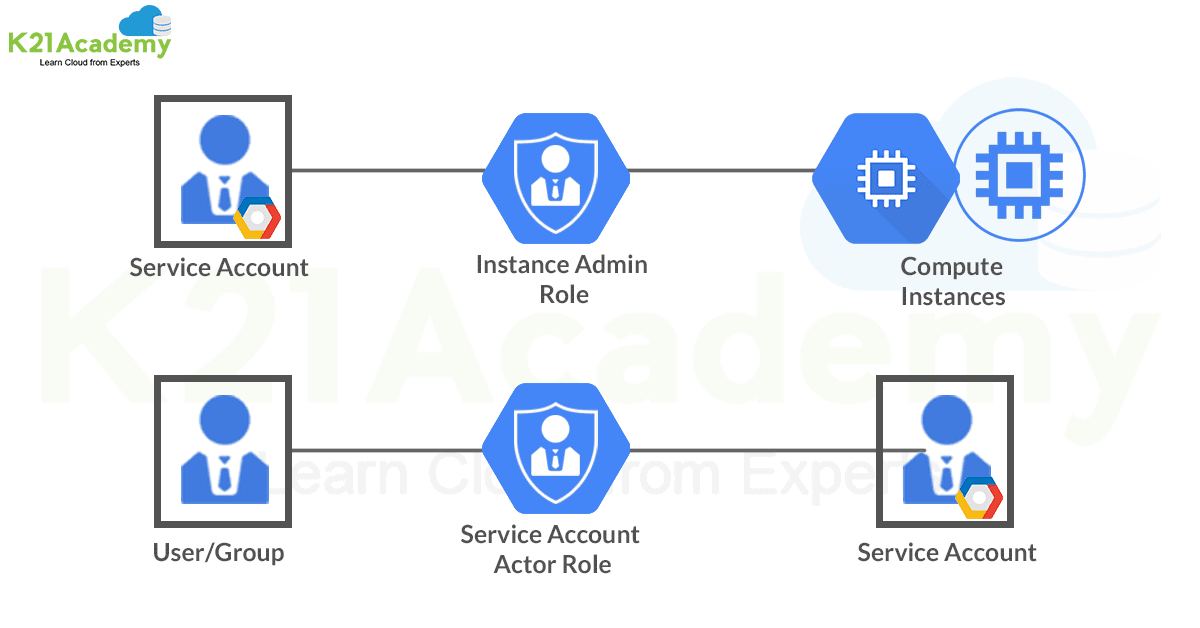
Q15: In what scenarios would I use the Service Account User role?
Ans: The Service Account User gives permissions to run operations as the service account. When
granted together with the compute.instanceAdmin role, the iam.serviceAccountUser role gives
users the ability to create and manage Compute Engine instances that use a service account.
Users who are serviceAccountUsers for a service account can access all the resources for which
the service account has access.
Q16: How do I control who can create a service account in my project?
Ans: Owner and editor roles have permissions to create service accounts in a project. If you wish to grant a user permission to create a service account, grant them the owner or the editor role.
Q17: Can I create a service account under an organization?
Ans: Currently you can create service accounts only under a project; you cannot create a service account directly under an organization. But if you grant IAM permissions at an organization level, the permissions will be inherited by projects under that organization, and in turn by service accounts under the projects.
Quiz Time (Sample Exam Questions)!
With our Google Professional Cloud Architect training program, we cover 200+ sample exam questions to help you prepare for the certification.
Check out one of the questions and see if you can crack this…
Ques: Your customer is moving their corporate applications to Google Cloud. The security team wants detailed visibility of all resources in the organization. You use Resource Manager to set yourself up as the Organization Administrator. Which Cloud Identity and Access Management (Cloud IAM) roles should you give to the security team while following Google recommended practices?
A. Organization viewer, Project owner
B. Organization viewer, Project viewer
C. Organization administrator, Project browser
D. Project owner, Network administrator
Comment your answer in the comment box below.
Feedback
We always improve and be the best version of ourselves from the previous session, hence constantly asking for feedback from our attendees.
Here’s the feedback that we received from our trainees who had attended the Day 3 session of our Google Cloud Training…
Related References
- Google Cloud Architect Q/A| Day 1 Live Session Overview
- Google Cloud Architect Q/A| Day 2 Live Session Overview
- Google Professional Cloud Architect: Step-By-Step Hands-On Guide
- Google Cloud Services & Tools
- Google Cloud Functions
- Google Kubernetes Engine
Next Task For You
If you are also interested and want to know more about the Google Professional Cloud Architect certification, register for our Free Class.








![AWS DevOps [DOP-C02] Professional Step By Step Activity Guides (Hands-On Labs)](https://k21academy.com/wp-content/uploads/2023/02/DOP-C02-1.png)



