We are back again with some quick tips, including Q/A and blog posts on the topics covered in the Day 5 Live sessions, which will help you clear Kubernetes Certifications [CKA/D] and get a better-paid job in the field of Microservices, Containers, DevOps & Kubernetes.
In the previous week, i.e., from Day 3 and Day 4 sessions, we covered Services, Replica Sets, Deployment, HPA, Configuring Autoscaling with HPA, Resource Quota, and Daemonset Controller and Dashboard.
This week of Day 5, we have covered the Kubernetes Scheduling (Node Selector, Node Affinity and Anti-Affinity, Taint and Toleration), Secrets and Maintenance.
We also covered hands-on Lab 19, Lab 20, Lab 21 and Lab 25 out of our 30+ extensive labs.
↦ Know everything about the CKA Certification
So, here are some of the Q/A’s asked from Day 5 Live session
Introduction to Scheduling(Node Selector, Node Affinity, Anti-Affinity, Taint and Toleration)
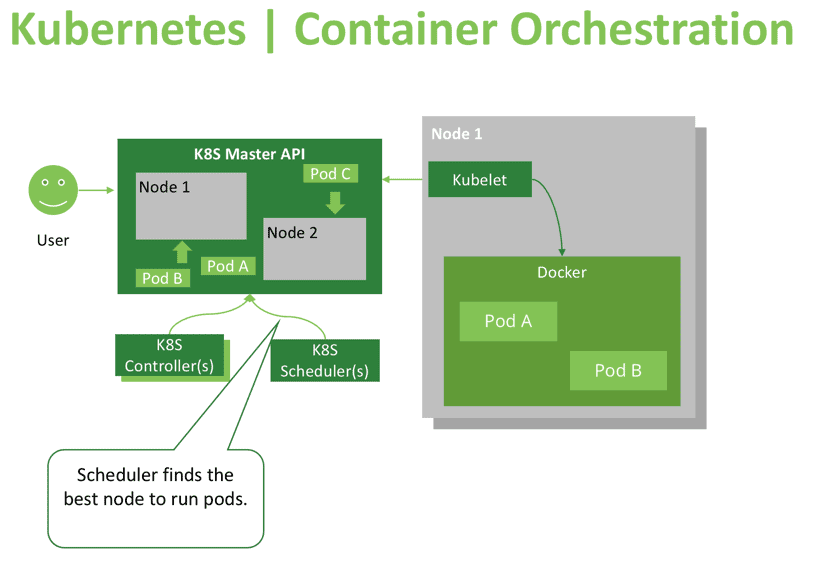
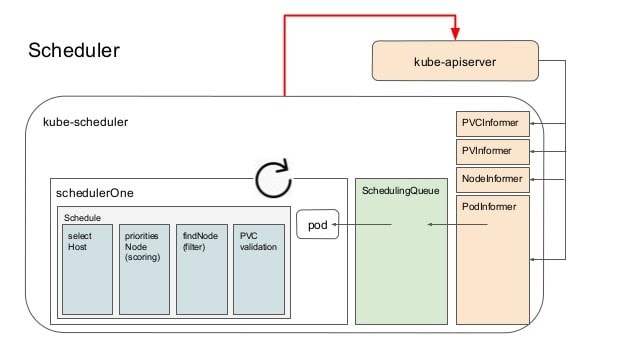
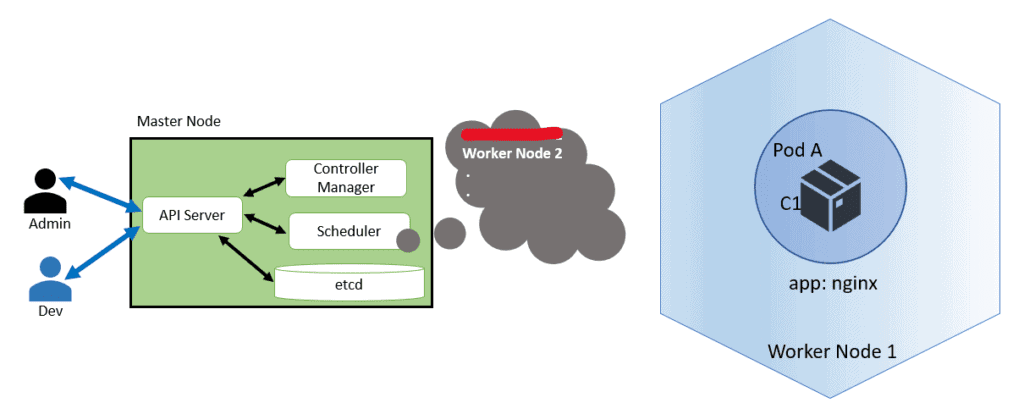
The Kubernetes scheduler is a control plane process that assigns pods to nodes. The scheduler determines which nodes are the effective positions of each pod in the scheduling queue based on restrictions and available resources. The scheduler then classifies each valid node and links the pod to the appropriate node.
Q1) What is scheduling in Kubernetes?
Every pod that the scheduler discovers becomes responsible for finding the best node for that pod to run on. In Kubernetes, scheduling refers to making sure that Pods are matched to Nodes so that Kubelet can run them on the available nodes.
The Kubernetes scheduler’s task is to ensure that each pod is assigned to a node to run on. At a high level K8s scheduler works in the following way:
- When new pods are created, they’re added to a queue.
- The scheduler continuously takes pods off that queue and schedules them on the nodes.
↦ Read more about the Kubernetes scheduling
Q2) What is Node Affinity?
Ans: Node Affinity provides advanced features that restrict pod placement to specific nodes. Affinity has three types: node affinity, sheath affinity, and anti-affinity. It is crucial to think of them as attributes of the pod.
Q3) What are types of Node affinity?
Ans: There are two types:
- requiredDuringSchedulingIgnoredDuringExecution – In this state, the pod has not been created yet and will be created for the first time. Typically, association rules will be applied when creating a pod to place the pod on the correct.
- preferredDuringSchedulingIgnoredDuringExecution – In this state, the pod has been running and changes have been made to the environment that affects node affinity, such as changing the label of the node.
Q4) What is Kube-scheduler?
Ans: kubescheduler is the default Kubernetes scheduler and runs as part of the control plane. Kubescheduler means that you can write your own programming component and use it if you want and expect it. For each newly created pod or another unscheduled pod, kubescheduler will choose an optimal node to run. However, each pod container has different requirements for resources, and each pod also has different requirements. Therefore, existing nodes must be consistently filtered according to specific scheduling requirements.
Q5) What is a node selector?
Ans: In node selector, we specifically mentioned which node the pod should go to. Using node affinity, we specify some rules for selecting the nodes that can schedule the pod. These rules are defined by marking nodes and letting the pod specification specify selectors to match these tags.
Q6) What is node anti-affinity?
Ans: Pod anti-affinity allows you to specify rules for placing pods to other pods. These rules are defined by custom tags in the node and tag selectors specified in the pod. Pod affinity / anti-affinity allows a pod to specify the associativity (or anti-affinity) of the set of pods it can place. The node cannot control the location.
Q7) What is the topologykey?
Ans: The topologyKey is the key to the node label. If two nodes are marked with this key and the label has the same value, the programmer will treat the two nodes as being in the same topology. Developers try to place a balanced number of pods in each topology domain. DoNotSchedule (default) tells the scheduler not to schedule it.
Q8) What are Taints and Tolerations?
Ans: Tolerations are applied to pods and allows (but is not required) to schedule pods on nodes with matching taints, and tolerations work together to ensure pods are not programmed into inappropriate nodes. One or more taints are applied to a node; this means that the node should not accept any pod that does not tolerate taints
Q9) What are three type’s of taint effect which we can apply to a node?
Ans:
- NoSchedule: If we apply this taint effect to a node, it will only allow the pods with a toleration effect equal to NoSchedule. But if a pod is already scheduled in a node and then apply taint to the node having effect NoSchedule, then the pod will remain scheduled in the node.
- PreferNoSchedule: In this effect, it will first prefer for no scheduling of pod, but if you have a single node and a PreferNoSchedule taint is applied on it. Then even if the pod didn’t tolerate the taint, it would get schedule inside the node, which has a taint effect: PreferNoSchedule.
- NoExecute: This effect will restrict the pod to get scheduled in the node, and if a pod is already scheduled a specific node and we have applied a taint of effect NoExecute to the specific node, it will immediately throw out the pod outside the node.
Also Check: Our blog post on Kubernetes Statefulset.
Kubernetes Secrets
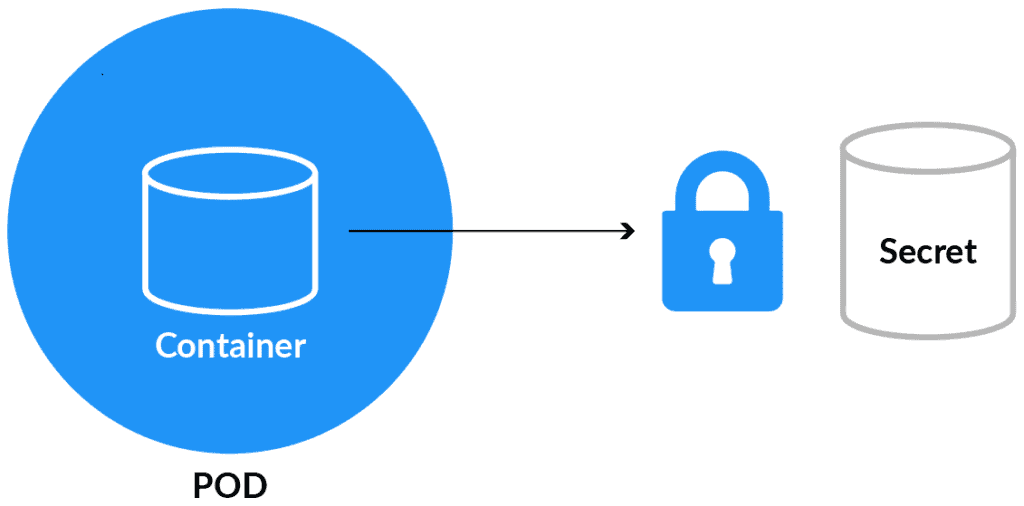
Secrets are used to hold sensitive data like passwords or keys. They’re similar to configMap except that they’re stored in an encoded or hashed format with config maps.
There are two levels involved in working with secrets. First, to create the secret, and second, to introduce it into the pod. Putting confidential data in secret is safer and adaptable rather than putting it in a container image or a Pod definition.
To use a secret, a pod has to reference the secret. There are three ways to use a secret with a Pod:
- As a file in a volume mounted on one or more of its containers.
- As a container environment variable.
- kubelet uses secrets by pulling images for the pod.
Read More: About Kubernetes Secrets
Q10) What are built-in Secrets?
Ans: Built-in Secrets is where Service accounts automatically create and Attach Secrets with API credentials. K8s automatically creates secrets that include credentials for reaching the API and automatically alters your pods to use this type of secret. The automatic and also the use of API credentials can be overridden or disabled if wanted.
Q11) How to create a Secret in Kubernetes?
Ans: There are several options to create a Secret:
- Create Secret using kubectl command
- We can create a Secret from the config file
- Create Secret using customise
Q12) How to edit/update and use a Secret in Kubernetes?
Ans: Run the following command to edit a Secret:
$ kubectl edit secrets mysecret
Secrets can be attached as data volumes or exhibited as environment variables used by a container in a Pod. Other parts of the system can also use secrets without being directly exposed to the pod.
Read More: About how to update/edit secrets
Cluster Node Maintenance
Suppose any node is facing any performance issue or needs to apply kernel upgrade that requires some node downtime. In that case, we can drain a node, which indicates that all pods have been safely evicted and scheduled to another node, which is marked as unschedulable.
Here is the answer to the question shared last week
Ques) To create a new deployment in Kubernetes which command you will use from the following options?
A. Kubectl run
B. Kubernetes get deployment
C. Kubernetes set deployment
D. None of the above
Answer: D
Explanation: Kubectl run command is used to create a new deployment in Kubernetes.
Quiz Time (Sample Exam Questions)!
With the CKA training program, we will cover 100+ sample exam questions to help you prepare for CKA certification. Check out the questions and see if you can solve this.
Ques) Which of the below taint effect are possible which can apply to a node?
A. NoSchedule
B. PreferNoSchedule
C. NoExecute
D. All of the above
Comment down your answers.
The correct answer will reveal in next week’s blog.
Related Post
- How To Setup A Three Node Kubernetes Cluster For CKA: Step By Step
- CKA Certification Exam (Certified Kubernetes Administrator)
- Multi Container Pods In Kubernetes
- Kubernetes Architecture: An Introduction to Kubernetes Components
- Kubernetes Ingress Controller Examples with Best Option
Join Our FREE class
To know about CKAD and what to study Including Hands-On labs you must perform to clear Certified Kubernetes Application Developer(CKAD) certification exam by registering for our FREE class.
Click on the below image to Register Our FREE Class Now!





![AWS AI Services: Complete List of AI, ML & GenAI Tools with Use Cases [2026]](https://k21academy.com/wp-content/uploads/2024/09/AWS-AI-1.png)

![AWS DevOps [DOP-C02] Professional Step By Step Activity Guides (Hands-On Labs)](https://k21academy.com/wp-content/uploads/2023/02/DOP-C02-1.png)