The more recent the technologies are, the more prone they are to security issues. And container technology is not an exception. A containerization environment … [Read more...]
Secure and Harden Kubernetes, AKS and EKS Cluster with kube bench, kube-hunter and CIS Benchmarks
Security is a concern that never fades away, and it doesn't matter how recent the technology has rolled out. So we should always harden the Kubernetes cluster … [Read more...]
Docker Image Vulnerabilities and Trivy Image Scanner Guide
Docker containerization seems to be the perfect strategy to deploy your application. But is it really flawless? Well, it all depends on how you build the … [Read more...]
Kubernetes Installation Options: The Hard Way, Kubedm, MiniKube, Managed K8s (EKS, AKS, OKE, GKE)
This Blog lists different ways to set up and run Kubernetes. So when you install Kubernetes, choose an installation type based on ease of maintenance, security, … [Read more...]
Docker Storage: Volume, Bind Mount, tmpfs And NFS
Docker simplifies and accelerates our workflow while giving developers the liberty to innovate with their choice of tools, application stacks, and deployment … [Read more...]
Monolithic vs Microservices – Difference, Advantages & Disadvantages
Over the past few years, we've been teaching Docker & Kubernetes and 1st topic we cover is monolithic vs microservices here's why- There has been a lot … [Read more...]
Kubernetes Security For Beginner – CKS
Kubernetes is the most used platform among admins. Given the platform's popularity and high adoption rates, it’s important for developers to ensure that … [Read more...]
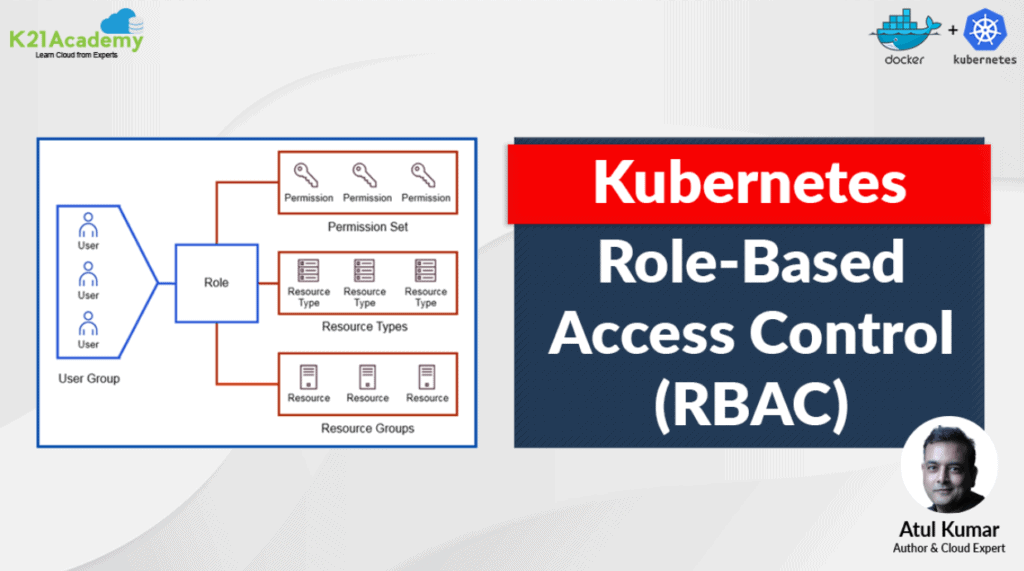
Role Based Access Control (RBAC)
In this blog, we will be covering RBAC or Role-Based access control. It's the way to outline which users can do what within a Kubernetes cluster. A Kubernetes … [Read more...]