In this blog, I have covered the overview, the need for Ansible vault, encrypt and decrypt the confidential information, and many other things which are part of the Ansible for Beginners Training Program.
Technological advancements make life way easier. But with advanced technology, there comes the threat to security. Ansible follows a typical setup with lots of sensitive data such as credentials, SSL certificates, public or private keys, and many more things. Hence, Ansible Vault came into existence to enhance the security of Ansible.
Let’s have a look at the topics of discussion:
- What is Ansible Vault?
- What is the need for Ansible Vault?
- Create an Encrypted File
- View Encrypted File
- Edit Encrypted File
- Rekeying Vault Password
- Encrypt Unencrypted File
- Decrypt Encrypted File
- Runtime Decryption of Encrypted File
- Encrypt Specific Variables
- Vault ID
- FAQ
- Conclusion
What is Ansible Vault?
It is a feature that allows users to encrypt values and data structures within Ansible projects. Ansible Vault is one of the great features of Ansible to keep all your files safe using encryption methods. Infrastructure as Code can increase a slight chance of exposing your sensitive data to the world. Therefore, Ansible can encrypt all your files, playbooks, and variables very easily. Ansible Vault comes up with file-level granularity where you can entirely encrypt or unencrypt the data. One of the smartest features of the Ansible vault is that it lets you use the same password for the encryption of files and decryption of files. This makes it very user-friendly.
What is the need for Ansible Vault?
While provisioning or automating the environment for deployment, there is a chance that playbooks contain sensitive data such as SSL certificates and other credentials. If you save this data in a normal text file, one wrong commit on a laptop or Github can create blunders. To resolve these kinds of issues, the Ansible vault came into existence.
Consider a scenario where you are provisioning your AWS Ubuntu server. There you will write a playbook that contains the AWS access key and AWS secret key. But there is no substantiated method of how you will save these keys from exposure. So you can either encrypt these two variables or encrypt the entire playbook. Now you are allowed to commit changes in GitHub securely.
Also Check: What is Ansible?
Create an ansible vault encrypt File
Note: While using Ansible Vault, we also need to work in vi editor. It works a bit differently.
Whenever you are done writing in the file, press the Esc button and then type :wq to save and exit from this editor. If you have pressed the Esc button and you want to write again, press the I button, and you will be able to write again. So let’s start with creating an Encrypted file.
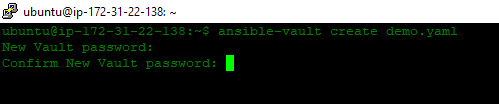
Step 1) Use the ansible-vault create command with file name in the following manner to create an encrypted file:
$ ansible-vault create filename.yaml
Step 2) Now, the terminal will prompt you to enter the password and confirm it, as shown in the image.
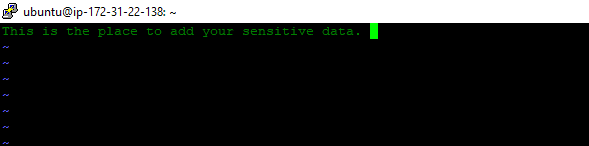
Step 3) When you confirm your password, your file will be saved, and an editor will open up. You can add your data in this editor, then save and exit. By default, Ansible Vault uses vi editor.
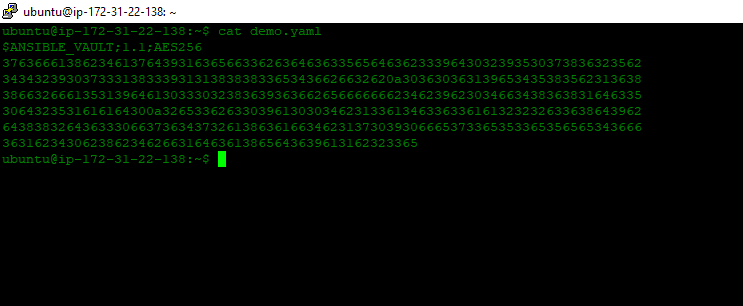
Step 4) Now, you can check that your file is encrypted using the following command:
$ cat filename.yaml
Check out: Ansible Configuration Management Tools
View Encrypted File
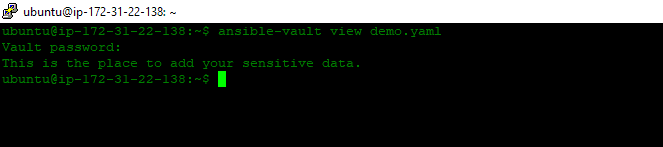
Step 1) You can also view the encrypted File using the following command:
$ ansible-vault view filename.yml
Step 2) Once you enter this command, it will ask for the password, enter the password, and you will be able to see the encrypted data present in this file.
Let’s see how to edit the encrypted files.
Edit Encrypted File
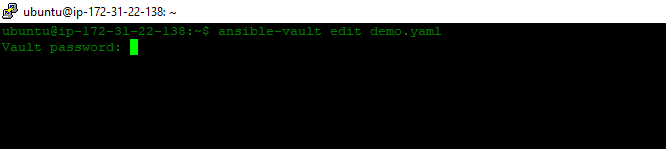
Step 1) Follow the commands given below to edit the encrypted file:
$ ansible-vault edit filename.yaml
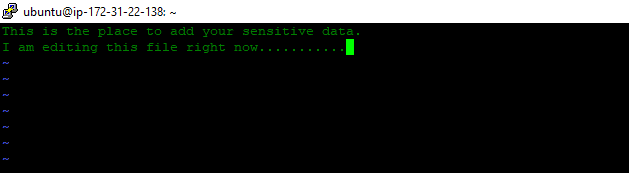
Step 2) When you paste this command, it will ask for the password. Enter the password, and it will open up the vi editor for you.
Step 3) Now, you can edit the file, save the changes, and exit.
Check out: Ansible vs Terraform
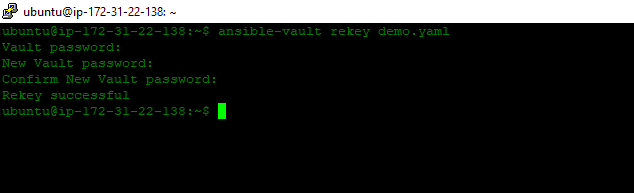
Rekeying Vault Password
Step 1) You can also change your old password with the new password using the Rekeying Vault Password Feature of Ansible. Follow the command given below to change the password:
$ ansible-vault rekey filename.yaml
Step 2) Once you enter this command, it will ask for the current password. After that, it will prompt for a new password. You can enter the new password, and it will display rekey successful.
Now, we will see how to Encrypt Unencrypted Files.
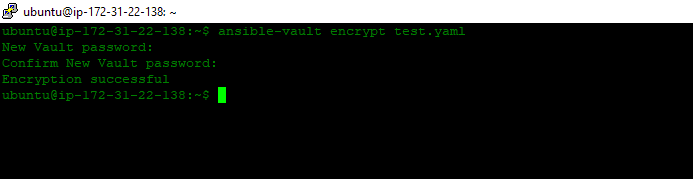
Encrypt Unencrypted File
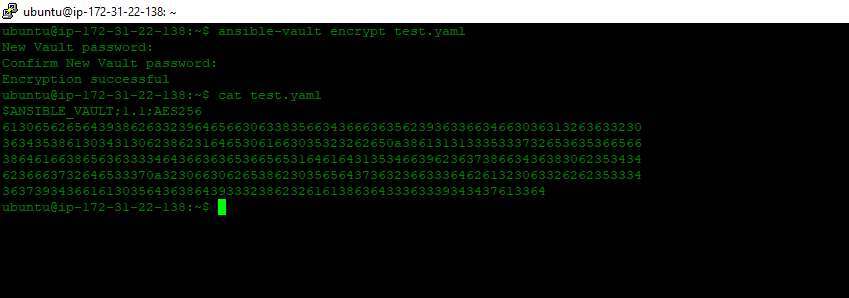
Step 1) Encrypting an existing file is also possible. You can do that using the ansible-vault command given below:
$ ansible-vault encrypt filename.yaml
Step 2) You can look at the image below that the data has been encrypted.
Let’s decrypt the file using the following methods.
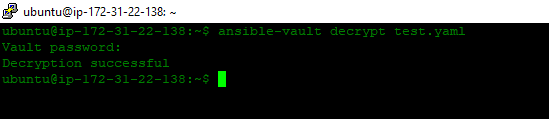
Decrypt Encrypted File
Step 1) If you want to decrypt the encrypted file, use the following command:
$ ansible-vault decrypt filename.yaml
Let’s see the runtime Decryption of Encrypted Files.
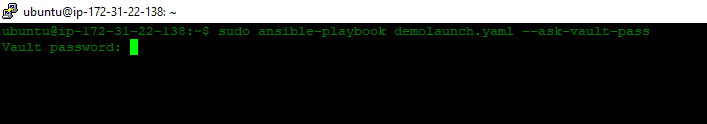
Runtime Decryption of Encrypted File
Step 1) You can also Decrypt a file during runtime using the –ask-vault-pass flag. In the following command demolaunch.yaml is a playbook that we have created.
$ ansible-playbook demolaunch.yaml --ask-vault-pass
Step 2) This command will decrypt all encrypted files which are required to execute the demolaunch.yaml playbook. But this is possible in the only case if the files are encrypted with the same password.
Step 3) Guys, there is no use of automation if it prompts you to enter the password again and again. So, as a solution, we will use one of the features of the Ansible vault called a reference file. You can add the password in this reference file and pass this file for automation during runtime.
$ ansible-playbook demolaunch.yml --vault-password-file ~/ .vault_password.txt
Step 4) You can also specify a separate script for the password. Make sure that your script file is in executable form and the password is printed in a standard output to reduce the margin of errors.
$ ansible-playbook demolaunch.yml --vault-password-file ~/ .vault_password.py
Check out: Ansible Provisioning
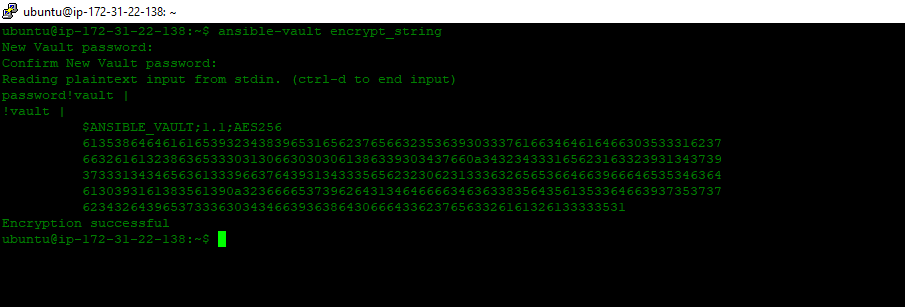
Encrypt Specific Variables
Step 1) Ansible Vault comes up with tons of features. You can even encrypt only specific variables or sensitive data. Let’s say if you want to show only specific data to other people, so you encrypt the data you want and keep the rest of the data as it is. You can use ansible-vault-encrypt_string as shown below:
$ ansible-vault encrypt_string
Step 2) Now, you need to enter the password and confirm it. You can add string values that you want to encrypt; when you insert values, press ctrl+d together to end the input. Now you can assign these encrypted values to the string you want to encrypt in the playbook.
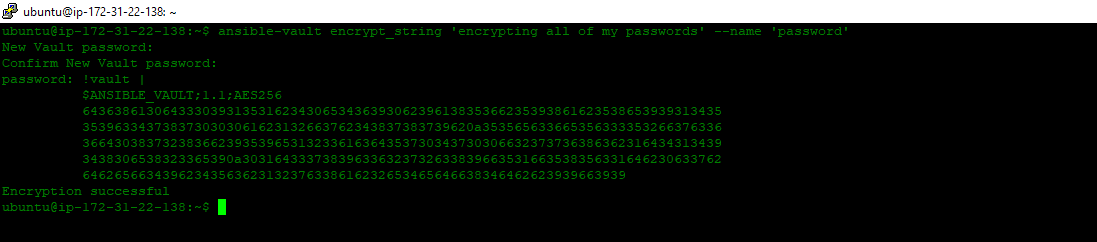
Step 3) If you do not want to follow this long process, you can also achieve this in a single line using the following command:
$ ansible-vault encrypt_string 'string' --name 'variable_name'
Check out: [AZ-400] Roles And Responsibilities As An Azure DevOps Engineer
Vault ID
Vault ID helps to provide an identifier to a specific vault password. You can encrypt different files with different passwords as a reference for a playbook. Ansible 2.4 update comes out with this feature. The latest versions of Ansible support only one password in the execution of each Ansible playbook.
You can execute a playbook that uses multiple files encrypted with different passwords using Vault Id.
$ ansible-playbook --vault-id vault-pass1 --vault-id vault-pass2 filename.yml
Common Mistakes to Avoid
Avoid the following common mistakes when using Ansible Vault:
- Storing passwords in plain text
- Sharing encryption keys insecurely
- Neglecting to rotate encryption keys regularly
FAQs
Can Ansible Vault encrypt any type of file?
Yes, Ansible Vault can encrypt any type of file, including YAML, JSON, and plaintext files.
Is Ansible Vault suitable for large-scale enterprise deployments?
Absolutely, Ansible Vault is designed to scale and can be effectively utilized in large-scale enterprise environments.
Can multiple users access encrypted files simultaneously?
While multiple users can access encrypted files, it's crucial to manage access control and encryption keys securely.
Does Ansible Vault support integrations with other tools and platforms?
Yes, Ansible Vault offers integrations with various tools and platforms, making it versatile and adaptable to different environments.
Is Ansible Vault open source?
Yes, Ansible Vault is part of the Ansible open source project and is available for free under the GNU General Public License.
Conclusion
Ansible is a blessing for automation and configuration management purposes. At the same time, to prevent the loss of sensitive data and provide that extra layer of security, an Ansible vault is introduced. As discussed above, it is an essential factor for the security and safety of SSL certificates and many other important credentials.
Related/References
- Check out Ansible for Beginners | Overview
- Check out the official Docs for Ansible Vault
- [AZ-400] Roles And Responsibilities As An Azure DevOps Engineer
- [AZ-400] Microsoft Azure DevOps Certification Exam: Everything You Need To Know
Next Task For You
If you are considering in-depth learning about Ansible in the coming days, then do join our WAITLIST and don’t miss an opportunity to attend a free class and gain a plethora of insights on the basics of Ansible.




Leave a Reply