If you’re considering a large-scale AWS deployment, you’re certainly curious about how to orchestrate numerous AWS apps and teams. How can you ensure that everyone on your team has access to AWS without your accounts devolving into huge, unmanaged chaos?
A multi-account structure can assist many businesses in meeting the particular needs of each application team or business group. AWS provides free native tools such as AWS Organisations to aid in the central orchestration of numerous accounts, allowing you to enforce security and billing policies while still allowing each team some degree of autonomy over their account. Maintaining several AWS accounts, however, can be time-consuming and prone to configuration drift.
In a nutshell, it provides the simplest way to set up and manage a secure, compliant, multi-account AWS environment based on best practices developed through collaboration with thousands of businesses.
In this blog, we will be covering –
- Overview
- Why separate central functions from application accounts?
- Architecture of the Control Tower
- What does a default AWS control tower include?
- Features
- Benefits
- Logging and monitoring in AWS Control tower
- Security
- Pricing
- Frequently Asked Questions
What is AWS Control Tower?
It offers a straightforward method for setting up and managing an AWS multi-account setup while following prescribed best practices. It combines the abilities of a number of other AWS services, including AWS Organisations, AWS Service Catalogue, and IAM Identity Centre (the replacement for AWS Single Sign-On), for rapidly creating a landing zone.
It uses preventive and investigative controls to assist in preventing your organizations and accounts from straying from recommended practices (guardrails). For example, guardrails can be used to make sure that security logs and the required cross-account access rights are produced and kept in place.
Why should central functions and application accounts be kept separate?
1. Because it is built on the AWS Organizations backbone, you can automatically control access and permissions for child accounts. You can define Service Control Policies in AWS Organizations to limit the services available to different accounts within the Organization. To ensure your organization has the safeguards in place to maintain a secure environment, you can enforce policies on account users and define cross-account permissions.
2. This is especially useful for restricting powerful roles in child accounts. A child account has no ability to override a restriction imposed by the master account. It is more difficult to grant select administrative access without the controls available within an AWS Organization structure.
3. AWS Control Tower and AWS Organizations are most appealing to businesses with a diverse set of IT roles and requirements. It’s also useful if you want to separate compliance standards while maintaining default functionality across environments.
Architecture of the Control Tower
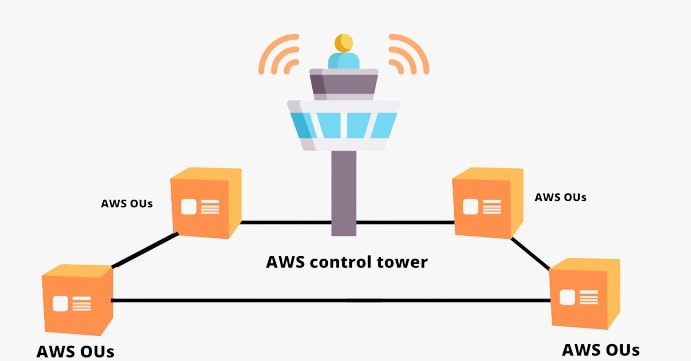
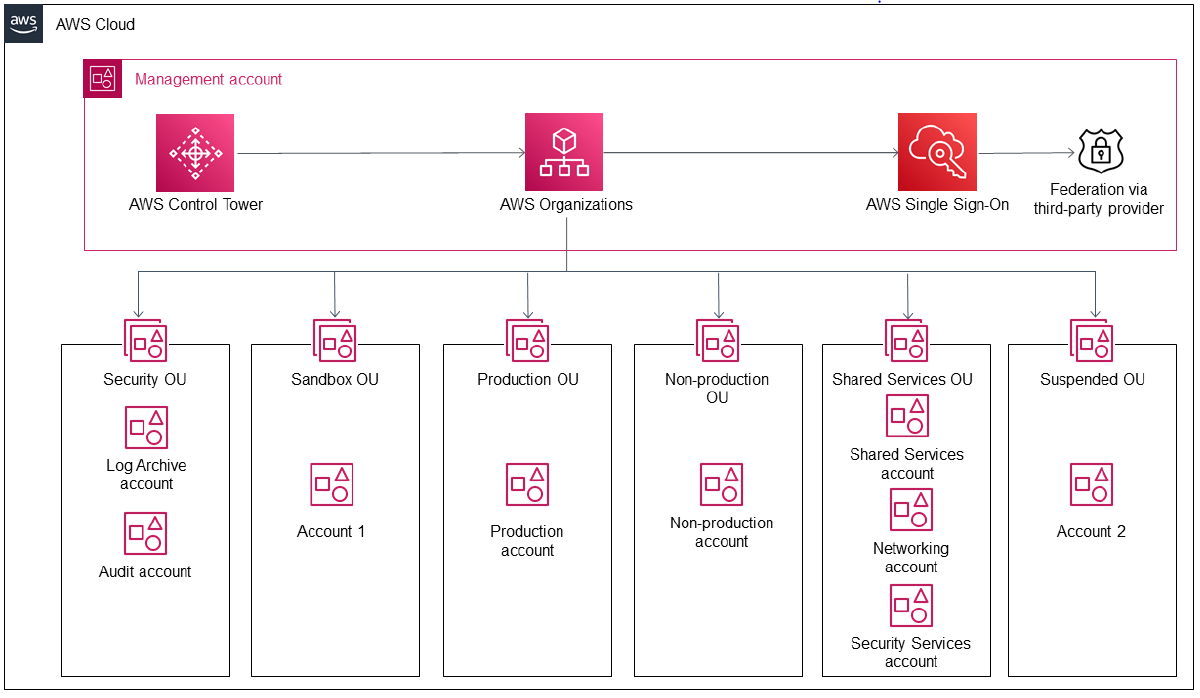
As you can see, accounts are assigned to a variety of OUs (Organisational Units). AWS Organisations are used to provide these for you.
- The Security OU has two accounts: the Log Archive Account and the Audit Account. The Log Archive Account acts as a central repository for all CloudTrail and AWS Config logs across the Landing Zone, which are securely saved in an S3 Bucket.
- The Sandbox OU is configured to host testing accounts (Sandbox Accounts) that are safely segregated from any production workloads.
- Production OU – This OU is responsible for hosting all of your production accounts and workloads.
- Non-Production OU – This OU can be used as a pre-production environment for additional testing and development.
- Suspended OU – This is a secure OU where you can move any deleted, reused, or compromised accounts. Permissions in this OU are tightly restricted, ensuring that it is a secure location.
- Shared Services OU – Accounts in the Shared Services OU host services are shared by numerous other accounts.
What is included in a standard AWS Control Tower?
1. Core Organizational Unit with 3 accounts:
- Master Account – Allows for the creation and financial management of member accounts Also used for Account Factory provisioning and reports, Organizational Unit management, and guardrails.
- Log Archive Account – This includes a centralized Amazon S3 bucket for storing logs of API activities and resource configurations from all solution accounts.
- Audit Account – A restricted account that provides read/write access to all accounts in the landing zone to security and compliance teams. You can review accounts programmatically from the audited account, thanks to a role that is only available to Lambda functions. The audited account does not permit you to manually log in to other accounts.
2. An initial security baseline that includes:
- AWS CloudTrail data is sent to the Logging Account’s centrally managed S3 bucket.
- In addition, AWS Config is sent to a centrally managed S3 bucket in the Logging Account.
- AWS Config Rules are enabled for monitoring encryption, IAM password policies, MFA, and security group rules.
- In AWS IAM roles, possibly including restrictions imposed by the master account.
- A preliminary Amazon VPC network
3. Account Factory –Essentially, an AWS Service Catalog product that allows you to automatically create new “child” accounts for the existing Organization while maintaining all predefined security baselines.
4. The Control Tower Dashboard –The UI was restricted to the basic Control Tower constructs. The dashboard displays only Control Tower-deployed and managed components.
The diagram below depicts the Control Tower dashboard with a few accounts provisioned.
Features of AWS Control Tower
1. Landing zone- A landing zone is a multi-account AWS environment that is well-architected and adheres to security and compliance best practices. It uses best-practices blueprints for identity, federated access, and account structure to automate the creation of a new landing zone.
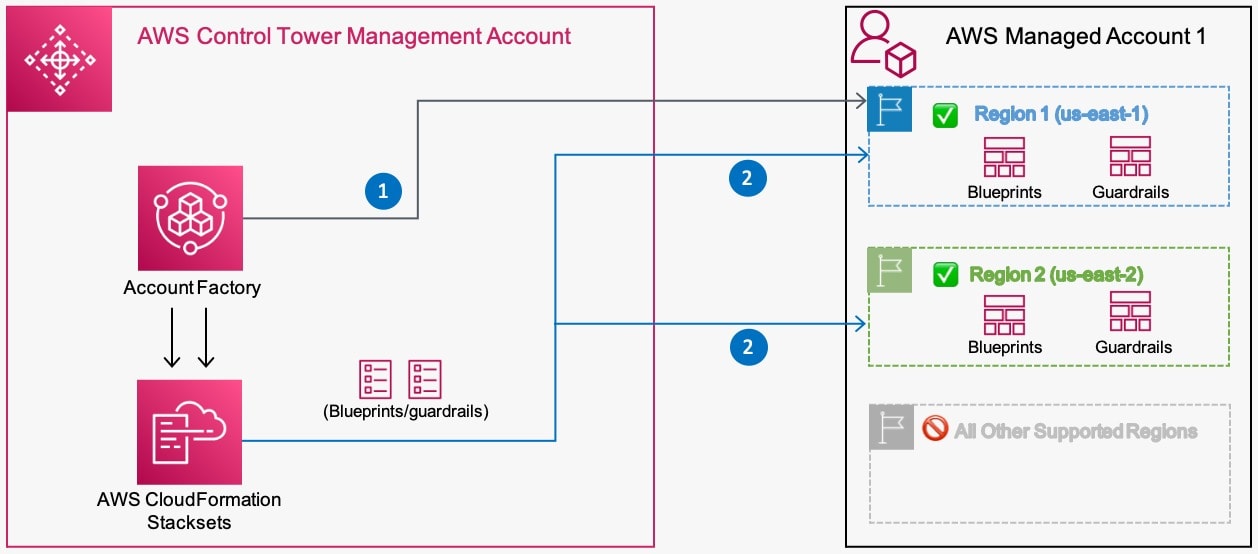
2. Account factory– It enables self-service for your builders to configure and provision new accounts using AWS Service Catalogue and helps you standardize the provisioning of new accounts with pre-approved account configurations and Region selections.
3. Preventive and detective guardrails– Guardrails are pre-packaged governance rules for security, operations, and compliance that you can select and apply to specific groups of accounts or the entire enterprise.
4. Mandatory and optional guardrails–
Some examples of mandatory guardrails include:
- Disallow changes to AWS IAM roles created by AWS Control Tower and AWS CloudFormation.
- Disallow changes to bucket policy for AWS Control Tower created Amazon S3 buckets in the log archive.
- Disallow cross-Region networking.
Some examples of optional guardrails include:
- Determine whether public write access to Amazon S3 buckets is permitted.
- Determine whether MFA for the root user is enabled, and
- Determine whether encryption is enabled for Amazon EBS volumes attached to Amazon EC2 instances.
5. Dashboard– The AWS Control Tower dashboard provides you with real-time insight into your AWS environment. It also looks at the number of OUs and accounts that have been provisioned, as well as the number of guardrails that have been enabled, and compares the status of your OUs and accounts to those guardrails.
6. Solutions of AWS control tower in AWS marketplace-These solutions address infrastructures and operational use cases such as multi-account security, centralized networking, operational intelligence, and Security and Information Event Management (SIEM).
Benefits of AWS Control Tower
1. Quick Configuration – While many businesses spend weeks or months developing a management strategy for their AWS environments, Control Tower allows them to do so in hours.
2. Manage All Accounts – You can give each account its own set of permissions when creating it. This customization enables you to form teams for various tasks without fear of them interfering with the progress of others.
3. Apply Guardrails – Guardrails can be quickly added by selecting them from the dashboard. The guardrails can then be applied to any accounts you want.
4. Use Visual Indicators – Visual indicators on the Control Tower’s dashboard provide a good indication of the state of the AWS environment. These indicators can be used in conjunction with notifications to make controlling the Control Tower easier.
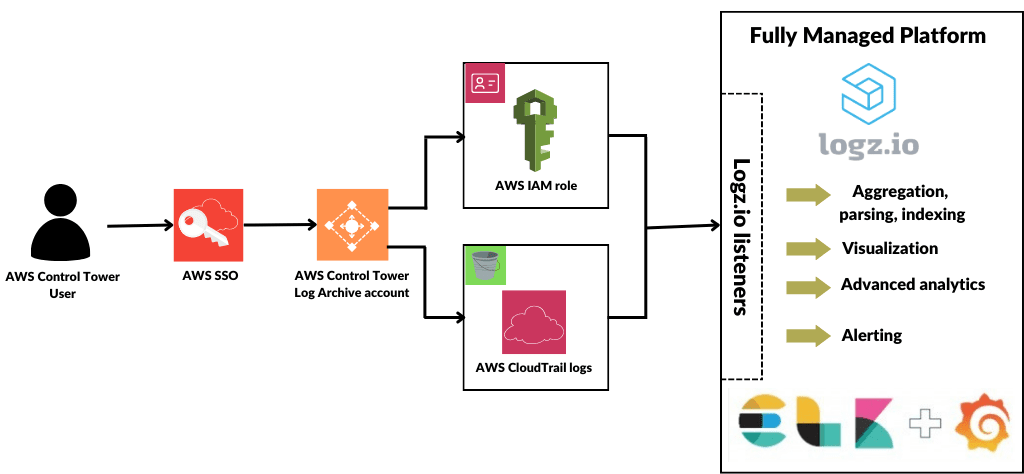
Logging & Monitoring in AWS Control Tower
Logging:
1. The integration with CloudWatch automates the logging of actions and events. All actions are recorded, including those taken from the AWS Control Tower management account and your organization’s member accounts. Management account actions and events can be viewed on the console’s Activities page.
2. The Activities page provides an overview of AWS Control Tower management account actions. Select Activities from the left navigation to get to the AWS Control Tower Activities page. The following are the fields displayed on the Activities page:
- Date and time: The timestamp for the activity.
- User: The person or account that initiated the activity.
- Action: The activity that occurred.
- Resources: The resources affected by the activity.
- Status: Success, failure, or another state of the activity.
- Description: More details about the activity.
Monitoring:
- Monitoring enables you to anticipate and respond to potential incidents. As a result, monitoring is an essential component of the well-designed nature of the AWS Control Tower. Because the outcomes of monitoring activities are saved in log files, logging and monitoring are closely related concepts.
- One of the shared accounts created when you set up your landing zone is the log archive account, which is dedicated to collecting all logs centrally, including logs for all of your other accounts. These log files enable administrators and auditors to review previous actions and events.
- It provides several tools for monitoring your landing zone’s resources and activity.
Security-
1. At AWS, cloud security is of the utmost importance. As an AWS customer, you will have access to a data center and network architecture designed to meet the needs of the most security-conscious organizations. AWS and you share the responsibility for security.
2. This is referred to as cloud security and cloud security in the shared responsibility model:
• Security of the cloud – AWS is in charge of safeguarding the infrastructure that supports AWS services in the AWS Cloud. As part of the AWS compliance programs, third-party auditors regularly test and verify the effectiveness of our security.
• Security in the cloud – The AWS services you use determine your liability. You are also accountable for other factors such as the sensitivity of your data, the requirements of your organization, and applicable laws and regulations.
 Pricing-
Pricing-
- The use of AWS Control Tower is free of charge. When you set up AWS Control Tower, however, you will start incurring costs for AWS services configured to set up your landing zone and mandatory guardrails. You only pay for what you use and only when you use it.
- For example, if you enable public subnets in the AWS Control Tower account factory configuration when creating a new account, the account factory will configure Amazon VPC to create a NAT Gateway, and you will be billed by Amazon VPC for your usage.
- If you run ephemeral workloads from AWS Control Tower accounts, you may see an increase in costs from AWS Config because it records configuration changes associated with creating and deleting these temporary resources.
- Amazon Elastic Compute Cloud (EC2) spot instances, Amazon EMR jobs, and AWS Auto Scaling are some examples.
Frequently Asked Questions
Who should use AWS Control Tower?
It is used to create or manage your multi-account AWS environment according to best practices. If you are creating a new AWS environment, beginning your AWS journey, launching a new cloud initiative, are completely new to AWS, or have an existing multi-account AWS environment but prefer a solution with built-in blueprints and guardrails, you will benefit.
Can I use my existing directory with AWS Control Tower?
It creates a native default directory for the IAM Identity centre. After configuring the landing zone, you can connect IAM Identity Centre to a supported directory, such as AWS Managed Microsoft AD.
What AWS Control Tower solutions can help me customize my accounts
It offers additional solutions such as Customizations for AWS Control Tower and Account Factory for Terraform to help you easily add customizations to your AWS Control Tower accounts using an AWS CloudFormation template and SCPs or Terraform. Accounts are created with all of the standard AWS Control Tower governance benefits, but you can add customizations to meet any additional standard procedures or guidelines that you require.
Related Links/References
- AWS Free Tier Limits
- AWS Free Tier Account Details
- How to create a free tier account in AWS
- AWS Free Tier Account Services
- AWS Certified Solutions Architect Associate SAA-Co3
Next Task For You
Begin your journey towards an AWS Cloud by joining our FREE Informative Class on Amazon Cloud Free Class by clicking on the below image.






 Pricing-
Pricing-


![AWS DevOps [DOP-C02] Professional Step By Step Activity Guides (Hands-On Labs)](https://k21academy.com/wp-content/uploads/2023/02/DOP-C02-1.png)