In this blog, we will cover AWS Certified Security Specialty Exam Questions that give you a first-hand idea of the type of SCS-C01 exam questions that may appear in the final certification exam.
Cloud computing, which delivers information technology services over the web, has become the main demand for businesses and governments seeking to accelerate innovation and collaboration. Cloud security involves the procedures and technology that protects cloud computing environments against external and insider cybersecurity threats. Cloud security and security management best practices designed to stop unauthorized access are required to stay data and applications within the cloud secure from current and emerging cybersecurity threats.
Through AWS, you’ll gain the control and confidence you would like to securely run your business with the foremost flexible and secure cloud computing environment available.
AWS allows you to automate manual security tasks so you’ll shift your focus to scaling and innovating your business. Additionally, you pay just for the services that you simply use.
The AWS Certified Security Specialty Certification exam is among the best 10 Most Popular Cyber Security Certifications. It is intended to gauge and approve the capacity of the contender to point out their insight across various AWS security spaces, including mindfulness, comprehension, and skill in getting AWS design, administrations, assets, and information.
If you are preparing for AWS Certified Security Specialty Certification [SCS-C01] Exam. Then check your readiness by attending to these SCS-C01 Exam Questions.
Let’s Discuss the domain of the question wise:
AWS Certified Security Specialty SCS-C01 Exam Questions
Domain 1: Identity Access Management, S3 & Security Policies
Q1. You currently have an S3 bucket hosted in an AWS Account. It holds information that must be accessed by a partner account. Which is the MOST secure way to allow the partner account to access the S3 bucket in your account? Select three options.
A. Make sure an IAM role is created which can be assumed by the partner account.
B. Make sure an IAM user is created which can be assumed by the partner account.
C. Make sure the partner uses an external id when making the request.
D. Provide the ARN for the role to the partner account.
E. Provide the Account Id to the partner account.
F. Provide access keys for your account to the partner account.
Answer: A, C, and D
Explanation:
Option A is CORRECT because a cross-account assume role has to be created for the requesting AWS account to access the services in your account.
Option B is Incorrect because IAM roles are assumed and not IAM users to allow cross-account service access.
Option C is CORRECT because a cross-account assume role requires an external ID to be provided for the requesting AWS account to access the services in your account.
Option D is CORRECT because a cross-account assume role requires an ARN to be provided for the requesting AWS account to access the services in your account.
Option E is Incorrect because the account ID is already available through ARN shared with the cross-account who wants to make a request.
Option F is Incorrect because access keys are not required to assume a role for the requesting AWS account.
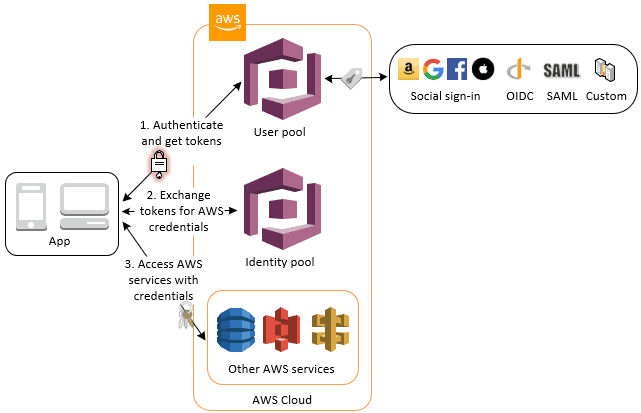
Q2. Your application currently uses AWS Cognito for authenticating users. Your application consists of different types of users. Some users are only allowed to read access to the application and others are given contributor access. How would you manage the access efficiently?
A. Create different AWS Cognito endpoints, one for the readers and the other for the contributors.
B. Create different AWS Cognito groups, one for the readers and the other for the contributors.
C. You need to manage this within the application itself.
D. This must be managed via Web security tokens.
Explanation:
Answer: B
Option A is incorrect because you need to create Cognito groups instead of endpoints to manage several users and groups.
Option B is CORRECT because we can utilise the groups to create a collection of users in a user pool, which is often done to set the permissions for those users. Like, we can create separate groups for users who are readers, contributors, and editors of your website and app.
Options C is Incorrect since there would be additional overhead to manage within the application. You can use different Cognito groups to manage permissions.
Option D is Incorrect because managing via Web security tokens is not as simple as option B.
Domain 2: Logging & Monitoring
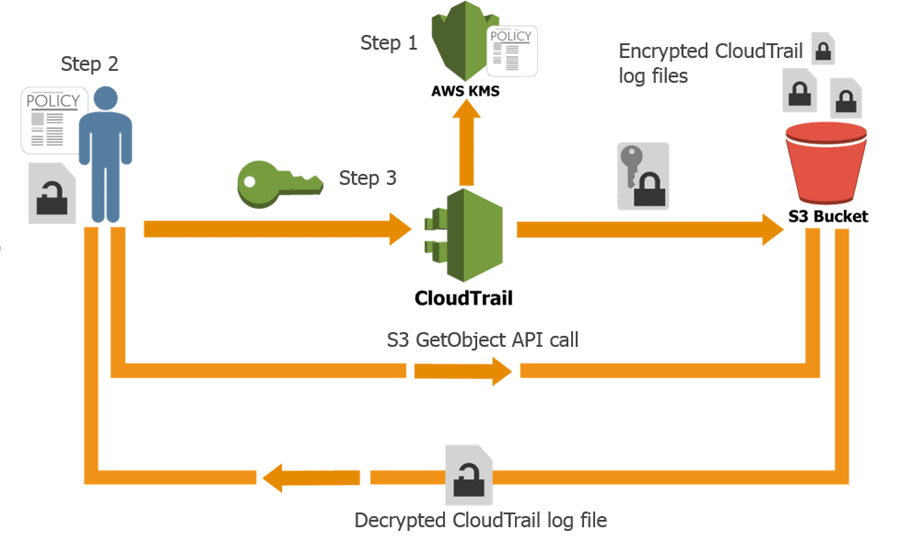
Q1. Your company uses AWS KMS for the management of its customer keys. From time to time, there’s a requirement to delete existing keys as a part of housekeeping activities. What is often done during the deletion process to verify that the key’s not being used?
A. Use CloudTrail to see if any KMS API request has been issued against existing keys.
B. Use Key policies to check the access level for the keys.
C. Rotate the keys once before deletion to check if other services are using the keys.
D. Change the IAM policy for the keys to check if other services are using the keys.
Explanation:
Answer: A
Option A is CORRECT because we can use AWS CloudTrail to check for any API request made to the existing KMS key. This can help us verify if the keys are being used or not.
Option B is Incorrect because Key policies cannot be used to check and verify if the keys are being used or not.
Option C is Incorrect because key rotation is employed when you retire an encryption key and replace the old key by generating a new cryptographic key. It can’t be used to check the last time interval for those keys.
Option D is Incorrect because the KMS key does not have IAM policies.
Q2. As an AWS account administrator, you wish to perform an audit and create a report of all services that have not been used in the IAM role “DevOps_Admin” in the past 6 months.
Which AWS service would you use to accomplish this task?
A. AWS IAM Access Advisor
B. AWS GuardDuty
C. AWS CloudTrail
D. AWS Resource Access Manager
E. AWS Config
Explanation:
Answer: A
Option A is CORRECT because AWS IAM Access Advisor provides permission guardrails to help control which services your developers and applications can access. By analyzing the last accessed information, you can determine the services not used by IAM users and roles.
Option B is incorrect because GuardDuty is a threat detection service.
Option C is incorrect because using CloudTrail does not provide the most efficient way to accomplish the task.
Option D is incorrect because AWS Resource Access Manager is a service for securing shared access to AWS resources across multiple AWS accounts.
Option E is incorrect because AWS Config is a service for controlling the configurations of AWS resources.
AWS IAM access advisor uses data analysis to help you set permission guardrails confidently by providing service last accessed information for your accounts, organizational units (OUs), and your organization managed by AWS Organizations.
You can implement permissions guardrails using service control policies (SCPs) that restrict access to those services.
Domain 3: Infrastructure Security
Q1. You have been given a new brief from your supervisor for a client who needs a web application set up on AWS. The most important demand is that MySQL must be used as the database. This database must not be hosted in the public cloud but rather at the client’s data centre due to security risks. Which of the subsequent solutions would be the best to assure that the client’s requirements are met? Choose the right answer from the options.
A. Build the application server on a public subnet and the database at the client’s datacenter. Connect them with a VPN connection that uses IPsec.
B. Use the public subnet for the application server and use RDS with a storage gateway to securely access and synchronize the data from the local data centre.
C. Build the application server on a public subnet and the database on a private subnet with a NAT instance between them.
D. Build the application server on a public subnet and build the database in a private subnet with a secure ssh connection to the private subnet from the client’s data centre.
Explanation:
Answer – A
Since the database should not be hosted on the cloud, all other options are invalid. The best option is to create a VPN connection for securing traffic as shown below in the diagram.

Option C is invalid since this is the incorrect utilisation of the NAT instance.
Option D is invalid since this is an incorrect configuration.
Q2. A company security team would like to receive notifications if an EC2 instance in their AWS environment is querying IP addresses that are associated with cryptocurrency-related (Bitcoin) activity. What steps can the security team take to achieve this most efficiently? (SELECT TWO.)
A. Install Amazon Inspector Agent.
B. Enable Amazon GuardDuty.
C. Create a CloudWatch Log group.
D. Create a new CloudTrail.
E. Subscribe to an SNS Topic.
Explanation:
Answer: B & E
Option A is incorrect because Amazon Inspector performs network and EC2 host assessment for common security vulnerabilities such as ones defined in the CIS Security Benchmarks. It does not help in this scenario.
Option B is CORRECT because GuardDuty can perform an assessment of network communication and produce “CryptoCurrency:EC2/BitcoinTool.B” finding when an EC2 instance is querying an IP address(es) that is associated with Bitcoin.
Option C is incorrect because a new CloudWatch Logs group is not efficient in finding the EC2 instance that is querying certain IP addresses.
Option D is incorrect because CloudTrail is used to trace the API activities and cannot check if an EC2 instance is querying certain IP addresses.
Option E is CORRECT because the SNS topic can be used to provide notifications.
Domain 4: Data Protection With VPCs
Q1. A company has a large set of keys defined in AWS KMS. The application uses the keys frequently. What is one of the ways that can be used to reduce the cost of accessing the keys in the AWS KMS service?
A. Enable rotation of the keys.
B. Use Data key caching.
C. Create an alias of the key.
D. Use the right key policy.
Explanation:
Answer: B
![AWS Security Specialty Certification [SCS-C01] Exam Questions](https://k21academy.com/wp-content/uploads/2021/11/2021-11-16-13_32_25-Data-key-caching-details-AWS-Encryption-SDK.png)
Option B is CORRECT because data key caching stores data keys and related cryptographic material in a cache. When you encrypt or decrypt data, the AWS Encryption SDK looks for a matching data key in the cache. If it finds a match, it uses the cached data key rather than generates a new one. Data key caching can improve performance, reduce cost, and help you stay within service limits as your application scales.
Option C is incorrect because creating aliases for the key would not impact how the key is used and not reduce the access request.
Option D is incorrect because providing a key policy would not impact how the key is used and not reduce the access request.
Q2. You have an EBS volume attached to a running EC2 Instance that uses KMS for Encryption. Someone has deleted the Customer Key which was used for the EBS encryption. Which of the following options is needed so that the EC2 instance can still use the EBS volume?
A. Create a new Customer Key using KMS and attach it to the existing volume.
B. Nothing is needed as the key deletion has no immediate effect on the EC2 instance or the EBS volume.
C. Request AWS Support to recover the key.
D. Use AWS Config to recover the key.
Explanation:
Answer: B
Option A is incorrect because creating a new CMK and attaching it to the exiting volume will not allow the data to be decrypted. You cannot attach customer master keys after the volume is encrypted.
Option B is correct because the deletion of CMK has no immediate effect on the EC2 instance or the EBS volume because Amazon EC2 uses the plaintext data key—not the CMK—to encrypt the disk I/O to the EBS volume.
Option C is incorrect because you cannot use AWS Support to recover the key once the key has been deleted.
Option D is incorrect because once the key has been deleted, you cannot use Config to recover the key.
Domain 5: Incident Response
Q1. You’ve accidentally lost the administrator password for an EBS-backed Windows Server EC2 instance. The instance has the Systems Manager agent installed. You want to regain access to your instance. What is the easiest way to resolve this issue?
A. Use Systems Manager Run Command to run AWSSupport-RunEC2RescueForWindowsTool command document.
B. Open Amazon EC2 console. Under Instances, select the specific instance. Under Actions, Instance Settings, choose the Reset Instance Password option.
C. Generate a new key pair. Use Import-EC2KeyPair AWS Tools for Windows PowerShell command.
D. Use EC2Rescue Tool. Choose Diagnose and Rescue. Select Ec2SetPassword.
Explanation:
Answer: A
Option A is CORRECT because using the SSM run command to run the AWSSupport- RunEC2RescueForWindowsTool command document with the ResetAccess command is the easiest way to reset a lost Windows Server password.
Option B is incorrect because there is no Reset Instance Password option under Actions, Instance Settings.
Option C is incorrect because the Import-EC2KeyPair command imports a key pair into the AWS EC2 Console and is not used to reset the password for a windows machine.
Option D is incorrect because it is not the easiest and quickest solution. This option requires provisioning of a recovery Windows Server EC2 instance, installing EC2Rescue Tool, and manually reset the password.
Q2. One of the EC2 Instances in your company has been compromised. You have already terminated the instance. It has been found that someone opened a port in the EC2 security group that has resulted in the problem. You need to take some steps to detect configuration changes in the AWS account. Which of the following options are suitable? (Select TWO.)
A. Remove the IAM role applied to the EC2 Instance.
B. Turn on AWS CloudTrail in every AWS Region.
C. Configure AWS Config rules to track the Security Group changes.
D. Replace all EC2 instances with Lambda functions.
Explanation:
Answer – B and C
Option A is incorrect because removing the role will not help completely in such a situation.
Option D is incorrect because this may not be practical and need lots of work. Lambda functions may also have security issues if security best practices are not applied.
Turning CloudTrail on in every AWS Region will allow you to identify unusual behaviour more easily, such as AWS services being provisioned from an AWS Region that your organization does not use.
With AWS Config rules, you can trace the Security Group resources and alert you whenever a security group has been changed.
Download the Complete SCS-C01 Exam Questions
When you have tested your knowledge by answering these SCS-C01 exam questions, I hope you have a clear stand in terms of your AWS Certified Security Specialty Certification (SCS-C01) exam preparation.
Note: K21Academy also offers a complete SCS-C01 Exam Questions Prep Guide where learners get to practice questions to test their AWS Certified Security Specialty Certification (SCS-C01) exam preparation before the actual exam.
To download the complete SCS-C01 Exam Questions guide click here.
If you feel you are lagging somewhere and you need to buckle up your preparation process, then you can enrol for the K21 Academy AWS Certified Security Specialty Certification certification training course to clear the final exam successfully.
Related References
- AWS Certificate Manager: Overview, Features and How it Works?
- AWS Database Services – Amazon RDS, Aurora, DynamoDB, ElastiCache
- Multi-Account Management Using AWS Organizations
- AWS Certified Solutions Architect: Roles & Responsibilities
- Amazon Kinesis Overview, Features And Benefits
- AWS Route 53 Introduction
- Amazon Elastic LoadBalancer
- Amazon RDS
Next Task For You
Begin your journey towards an AWS Cloud by joining our FREE Informative Class on Amazon Cloud Free Class by clicking on the below image.
![AWS Security Specialty Certification [SCS-C01] Sample Exam Questions](https://k21academy.com/wp-content/uploads/2021/11/S3-IAM-2020-Figure-2.png)



Leave a Reply