[July 10, 2019] Oracle released a new update in Oracle Cloud Infrastructure (OCI) that allows you to create Network Security Groups (NSGs) used to implement security rules in your Virtual Cloud Network (VCN).
The OCI Networking service offers two virtual firewall features:
- Security Lists (SL): The original virtual firewall feature from the Networking service.
- Network Security Groups: A subsequent feature designed for application components that have different security postures.
These two features offer different ways to apply security rules to a set of Virtual Network Interface Cards(VNICs) in the Virtual Cloud Network(VCN).
In this blog post, we discuss the Differences between Network Security Groups and Security List. Also, we tell you When to use what.
Overview Of Network Security Groups
Network Security Groups are another method for implementing security rules. NSGs provide a virtual firewall for a set of Cloud resources that have the same security posture.
NSGs consist of two types of items:
- VNICs: One or more VNICs (for example, the VNICs attached to a set of Compute instances have the same security posture). All the VNICs must be in the VCN that the NSGs belong to.
- Security rules: Security rules define the types of traffic allowed in and out of the VNICs in the group. For example, ingress TCP port 22 SSH traffic from a particular source.
Resources That Support Network Security Groups:
- Compute instances
- Load balancers
- DB systems
- Autonomous Databases
Note: For resource types that do not support NSGs yet, continue to use security lists to control traffic in and out of those parent resources.
Overview Of Security List
A Security List acts as a virtual firewall for an instance with ingress and egress rules that specify the types of traffic allowed in and out. Security lists are regional entities.
Security List allows two types of traffic:
- Ingress: Incoming Traffic
- Egress: Outgoing Traffic
Comparison Of Network Security Groups And Security List
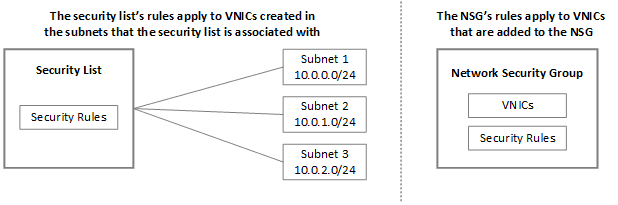
- A Security list lets you define a set of security rules that applies to all the VNICs in a subnet whereas Network Security Groups let you define a set of security rules that applies to a group of VNICs of your choice.
- NSGs’ security rules apply only to the resources in that NSG. By contrast, Security Lists’ rules apply to all the resources in a subnet that uses the list.
- NSGs consist of a set of ingress and egress security rules that apply only to a set of VNICs of your choice in a single VCN.
- Unlike with Security List, the VCN does not have a default NSGs. Also, the NSGs you create are initially empty. They have no default security rules.
- A Security List is used at the packet level.
- NSGs are another way to implement security rules.
- Security Lists have separate and different limits compared to the Network Security Groups.
When To Use What?
Security Lists provide comprehensive security to applications with security rules applied to every subnet. But if you have multiple resources that require different security postures within a subnet, and you need to control the traffic at a more granular application level, then you can create those granular rules and add multiple resources to them using Network Security Groups.
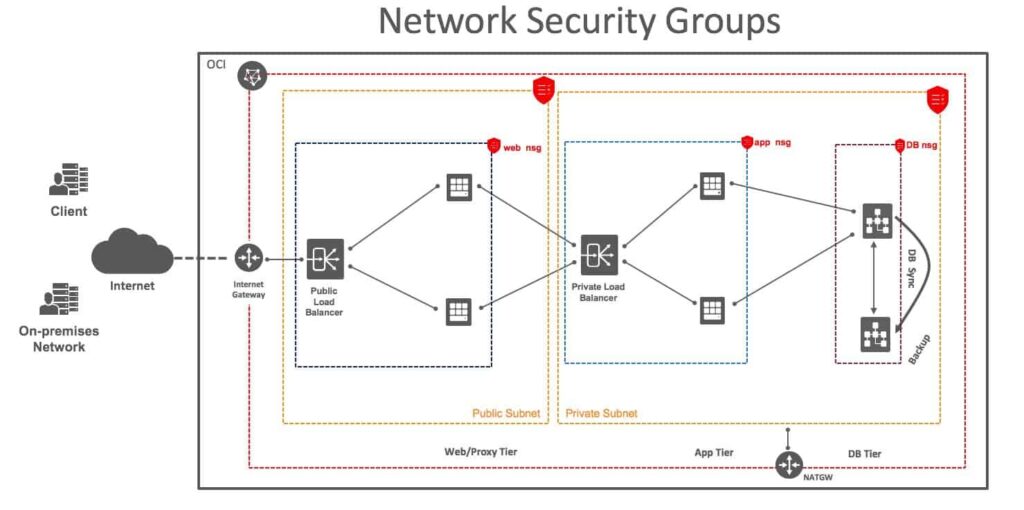
In this diagram, you have a 3-tier web application in which the web/proxy tier is deployed in the public subnet, and the application and the database tiers are deployed in the private subnet. To secure the application tier, you can create granular security rules to control the traffic that enters the application and then apply the same rules to the application VNICs.
Related Posts
- Oracle Cloud Infrastructure (OCI): Region, AD, Tenancy, Compartment, VCN, IAM, Storage Service
- Oracle Cloud Infrastructure Architect Associates: Step by Step Activity Guides
- Network Security Groups
Next Task For You
Click on the image below to Register for the FREE Masterclass NOW!




Leave a Reply