Technology is advancing at a never-before-seen pace. Businesses strive to adapt to and take advantage of new technology as they develop. Aiming for security, enterprises must find innovative ways to quickly develop and deploy software given the rate of technological advancement. Integrating security into DevOps to deliver DevSecOps requires new mindsets, processes, and tools.
In this blog, we are going to learn about the DevSecOps role and its Security in DevOps Architecture.
- DevOps comprehension
- SecOps: A Quick Overview
- Integrating DevOps with SecOps to create DevSecOps
- Is DevSecOps the Best Method for You?
- The Role of Security in DevOps Architecture
- The DevSecOps pipeline
- Conclusion
DevOps comprehension
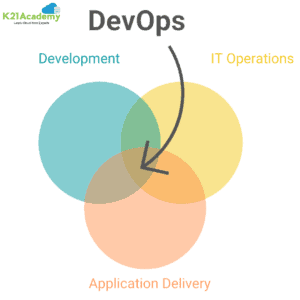
The prevalence of CI/CD structures emphasizes the significance of quickening development cycles and integrating deployment techniques into them. DevOps was born out of this need to manage a steady stream of service updates that improve customer satisfaction and result in stable product releases.
The DevOps methodology unifies the once separate functions of development and operations into a single cohesive entity that makes use of their backgrounds in many disciplines to increase the team’s success.
In an IT-driven organization, DevOps encourages teamwork and the collection of tools and technologies that work in concert to create better teams and speed up software development, upgrades, and deployment.
The need for technologies that improve collaboration and transparency is highlighted by DevOps. Businesses have primarily decreased the time spent on manual job handling as a result of embracing Software-as-a-Service across enterprise and customer-facing functionalities.
However, a variety of security risks have surfaced as a result of this new technology, endangering any company’s basic foundation.
SecOps: A Quick Overview
SecOps recognizes the rising necessity for enterprises to take software security seriously. SecOps is a seamless coordination of IT operations. To monitor cybersecurity risks and fix vulnerabilities, IT security teams should collaborate.
Again, this is a combination of teams that formerly worked in complete isolation from one another. Businesses may concentrate on a single objective — guaranteeing the security of their IT infrastructure and applications — by bringing these teams together.
As they search for the most effective solutions to secure servers, cloud environments, and networks, SecOps teams priorities security and compliance. SecOps fills a crucial role in multi-cloud setups as security challenges become more complex and systems grow to accommodate new requirements.
Automated processes are used by SecOps teams to swiftly find and fix vulnerabilities. In today’s high-risk environment, SecOps teams’ intense focus on system security can cause them to delay the development and deployment of a solution.
Integrating DevOps with SecOps to create DevSecOps
As you may have seen, both DevOps and SecOps place a strong emphasis on the necessity of communication between the IT and operations teams. In order to foster a deeper understanding of the system, both concepts encourage the utilization of multidisciplinary teams. As a result of their cooperation, teams now have a deep understanding of the underlying software rather than just being aware of the aspects that affect them.
With a fresh viewpoint, teams can concentrate on their work while also taking into account how any changes they make can affect the system as a whole.
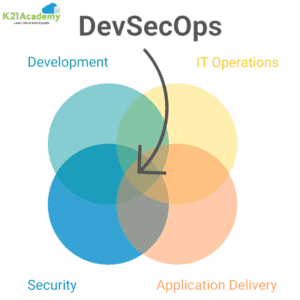
DevSecOps combines the principles of DevOps and SecOps to speed up software deployment while simultaneously guaranteeing high levels of security inside it. In essence, DevSecOps enables you to take use of the best of both environments.
To prevent the role from being centralized on a small group of individuals, DevSecOps assigns security to each team member. With this method, security teams are in a better position to identify potential vulnerabilities since they have a deeper comprehension of the product.
The collaborative environment of a DevSecOps methodology is designed to accommodate this shared responsibility. While operations teams learn about compliances and get a more comprehensive understanding of the system, developers embrace and practice high-security coding.
By doing this, companies may provide systems that are extremely secure from the start. If security issues arise, upgrades and improvements can be implemented without difficulty. In order to ensure the success of software enterprises, DevSecOps combines the speed and stability of DevOps with the security and compliance of SecOps.
Is DevSecOps the Best Method for You?
DevSecOps may be a suitable fit for your company if you are continuously trying to strike a balance between the need for security and compliance, quicker delivery, and the possibility of software updates and changes.
The managed DevSecOps services from WeSecureApp’s can support you if you’re prepared to introduce DevSecOps within your company. Planning, automation, and penetration testing are the three quick stages we use to help you transition operations from DevOps to DevSecOps in your CI/CD pipeline.
By speeding up product launches, fixes, upgrades, and revisions with a comprehensive DevSecOps implementation, you can gain a competitive edge.
The Role of Security in DevOps Architecture
DevOps has evolved into the unbreakable foundation of the software delivery ecosystem as cloud-powered digital company growth increases. DevOps enables development teams to produce apps more quickly by accelerating the deployment of functions and features. The fundamental principles of DevOps—”automation” for agility and “integration” of numerous tool sets for visibility—have lowered the complexity and distances between conventional development and operations teams. The result? Every development environment has significant productivity gains.
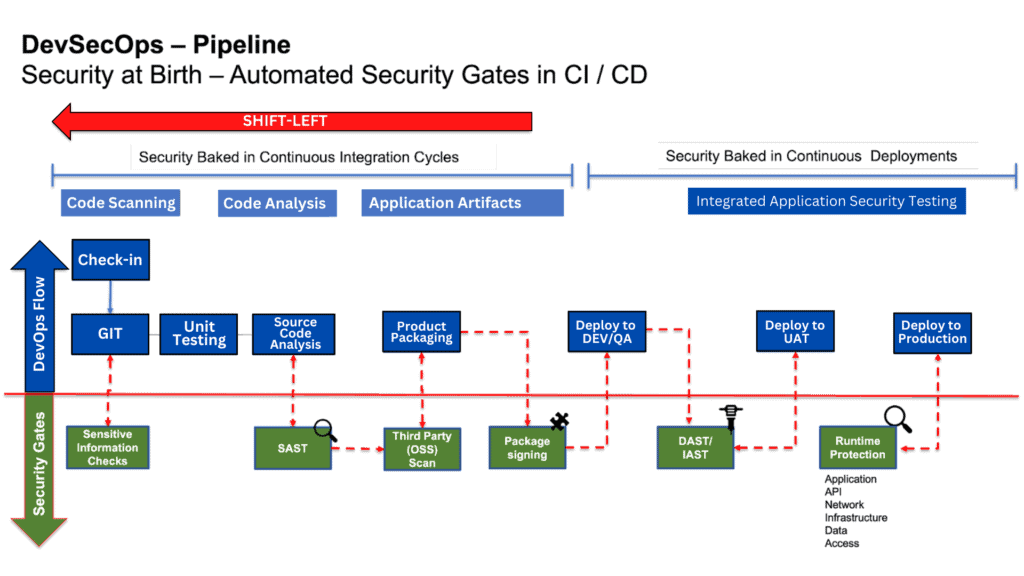
Due to the speed, agility, and cross-functional collaboration that DevOps provides, many organizations face the risk of surpassing “security,” which results in a massive backlog of remediation work for engineering and infrastructure teams. Fortunately, contemporary (CI/CD) tooling capabilities enable security checks to be incorporated into the DevOps process at practically any point of the development lifecycle (Code|Check-in|Build|Test|Deploy|Monitor).
Cloud-Native Application Security platforms (CNAPP) enable visibility for each software, DevOps, and security engineer by enabling security teams to design gates and guardrails that can be incorporated into any DevOps pipeline. A DevSecOps pipeline is a type of DevOps that incorporates security.
The DevSecOps pipeline
At several points of the CI and CD process, the security team can incorporate security gates, as detailed below:
Source code and integrated development environments (IDE)
An IDE is where code is created. Before the code is even checked into a source code system, developers could be made visible and directed to adhere to secure coding standards by integrating IaC scanning capabilities with an IDE.
The second check can be enabled during the source code check-in process. Every PR and MR raised by the developers is then examined for security holes and the potential for sensitive data leakage using SAST and OSS tools, giving approvers the chance to certify that the code is both clean and compliant before it enters the pipeline.
Build and Test (CI Pipeline)
After the code has been accepted and merged, the CI workflow is started. Security teams can scan the program throughout this phase for OSS (Open Source Software) vulnerabilities and their licensing, as well as do functional and unit testing. These security barriers assist in defending the product’s IP and avoiding zero-day vulnerabilities. Engineering teams’ review and approval timelines are shortened by this technique.
Artifacts
After completing the CI process, the central registry is pushed with clean and compliant code. To continuously check for the introduction of rogue or unregistered packages as well as zero-day and unauthorized access, security teams can enable vulnerability scanning, auditing, and access scanning on this central registry.
Deployment
Images from the registry that have been certified and signed are placed in a range of contexts to conduct stress, regression, and functional tests. In this cycle, security teams can “Grey-box test” the application using realistic attacker scenarios and project the exploitable dangers that may exist.
Monitor
The network, infrastructure, and apps have all been tested, scanned, and hardened. Security teams continuously monitor and safeguard the runtime behavior of the application, API, containers, cloud, network, and infrastructure using tools like CNAPP as SRE teams scale the application, infrastructure, and network. Security teams regularly gather, analyze, and correlate runtime signals from multiple application-building elements (Network, Infrastructure, and Cloud). In order to defend the customer-centric application and data, they create and implement the appropriate set of security guardrails.
Conclusion
Developers are empowered and guided by organization-defined security best practices thanks to security-integrated CI/CD workflows, which also help to reduce the security backlog. Proactive security is enhanced by DevSecOps workflows without sacrificing agility. For developing digital organizations and corporations, it’s essential to make sure that cloud apps are “born secure.”
Related Links/References:
- DevOps Foundation Certification Exam: Everything You Need To Know
- DevSecOps Overview And Important Tools
- [AZ-400] Microsoft Azure DevOps Certification Exam: Everything You Need To Know
- AWS Certified DevOps Engineer Professional DOP-C01
Next Task For You
Begin your journey towards becoming a DevSecOps Certified Engineer and earn a lot more in 2023 by joining our Free Class Waitlist.



Leave a Reply