In this blog, I’ll cover some valuable insights, including Q&As and valuable links, from Day 7 of our recent Cloud Security for Azure, AWS, Google Cloud, and Oracle live class, where we started our discussion on Storage and Database Security. Starting with Storage Security, we also did hands-on Lab-12 of our 18+ hands-on extensive labs in the live session.
On Day 6 in the previous week, we covered Platform Protection in Cloud.
So, here are some of the Q&As asked during the Live session from Module 3: Secure Data and Application.
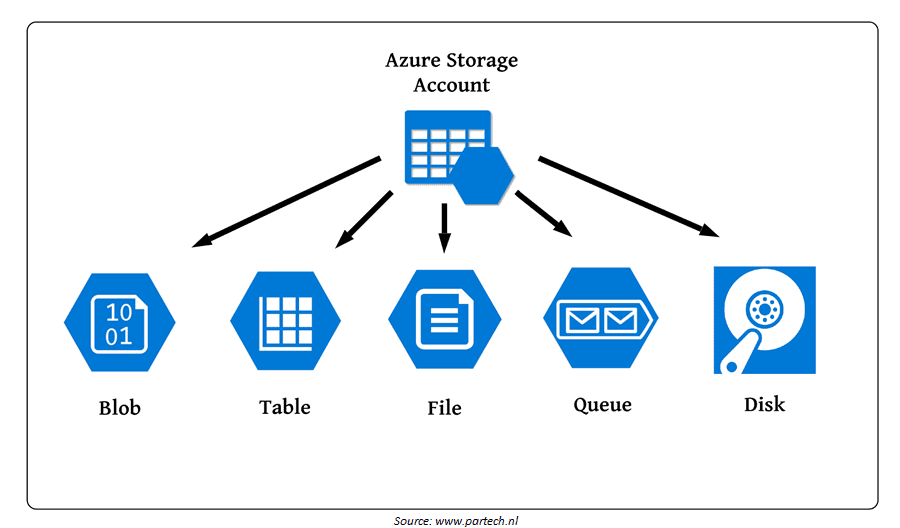
What is a Storage Account?
All your data items are stored in an Azure storage account: blobs, file shares, queues, tables, and discs. The storage account creates a unique namespace for your Azure Storage data that can be accessed through HTTP or HTTPS from anywhere in the world. Your storage account’s data is long-lasting and highly available, as well as safe and enormously expandable.
Q1. What do you mean by blobs, file share, queues, table and discs?
- Blob: The term “blob” is an acronym for “binary large object.” Blobs are large, unstructured files such as photos, video, music files, backup files, and so on. It’s a text and binary data object store with huge scalability. Data Lake Storage Gen2 also provides support for big data analytics.
- Azure Files: provides fully managed cloud file shares that can be accessed via the industry-standard Server Message Block (SMB) or Network File System (NFS) protocols. Cloud and on-premises deployments can both mount Azure Files file shares at the same time.
- Azure Queue: Storage is a service for storing large numbers of messages. Authenticated HTTP or HTTPS calls allow you to access messages from anywhere in the world.
- Azure Table: A NoSQL store for schemaless storage of structured data.
- Azure Disk: Block-level storage volumes for Azure VMs.
>Know more about Storage Account
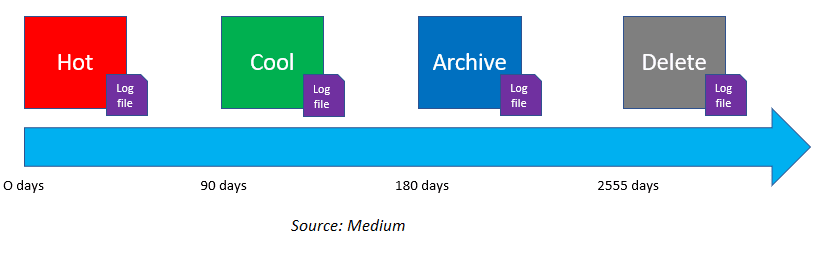
Access Tiers
The amount of data saved in the cloud is growing at an exponential rate. To keep expenses down as your storage needs grow, it’s a good idea to arrange your data by how often it’ll be accessed and how long it’ll be kept. Different access tiers are available in Azure storage, allowing you to store your blob data in the most cost-effective way possible based on how it will be used. The following are the Azure Storage access tiers:
- Hot tier: An online layer designed for storing data that is regularly accessed or updated. The storage costs at the hot tier are the highest, but the access costs are the lowest.
- Cool tier: An online layer designed for storing data that is accessed or modified seldom. The data in the cool tier should be kept for at least 30 days. In comparison to the hot tier, the cool tier has reduced storage costs but greater access expenses.
- Archive tier: Offline tier for archiving data that is rarely accessed and has variable latency requirements on the order of hours. The data in the archive tier should be kept for at least 180 days.
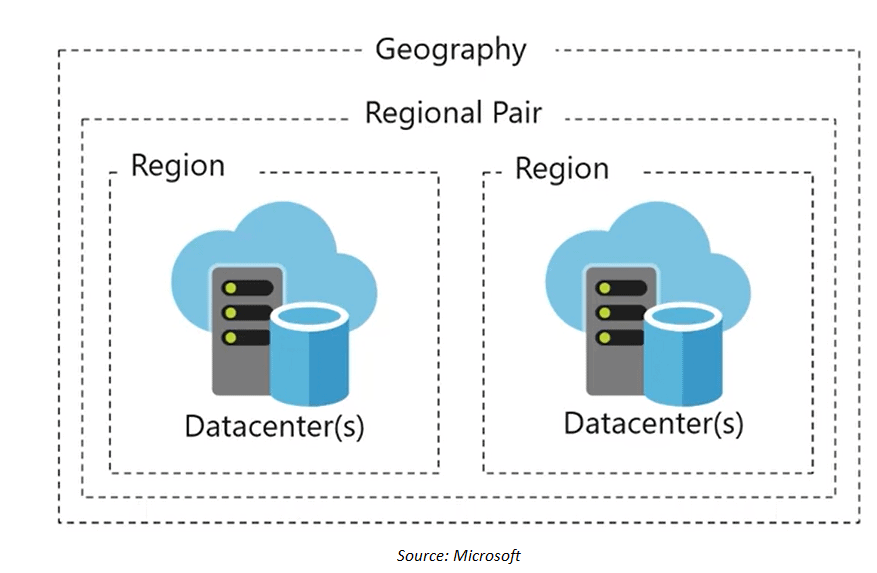
Data Sovereignty
Data sovereignty refers to the necessity that data be subject to the laws of the country in which it is gathered or processed and remain within its boundaries. These regulations have existed in many nations for decades, and new privacy legislation, such as the GDPR, are just increasing their prominence. Countries such as Russia, China, Germany, France, Indonesia, and Vietnam, to name a few, mandate that individuals’ data be maintained on physical servers within their borders.
Azure has more global regions than any other cloud provider, giving you the scalability and data residency options you need to bring your apps closer to your global users and well as maintain Data Sovereignty.
Q2. What storage redundancy options does Azure Files support?
Ans. Currently, Azure Files supports locally redundant storage (LRS), zone redundant storage (ZRS), geo-redundant storage (GRS), and geo-zone-redundant storage (GZRS). Azure Files premium tier currently only supports LRS and ZRS.
>Know about regions and region pairs
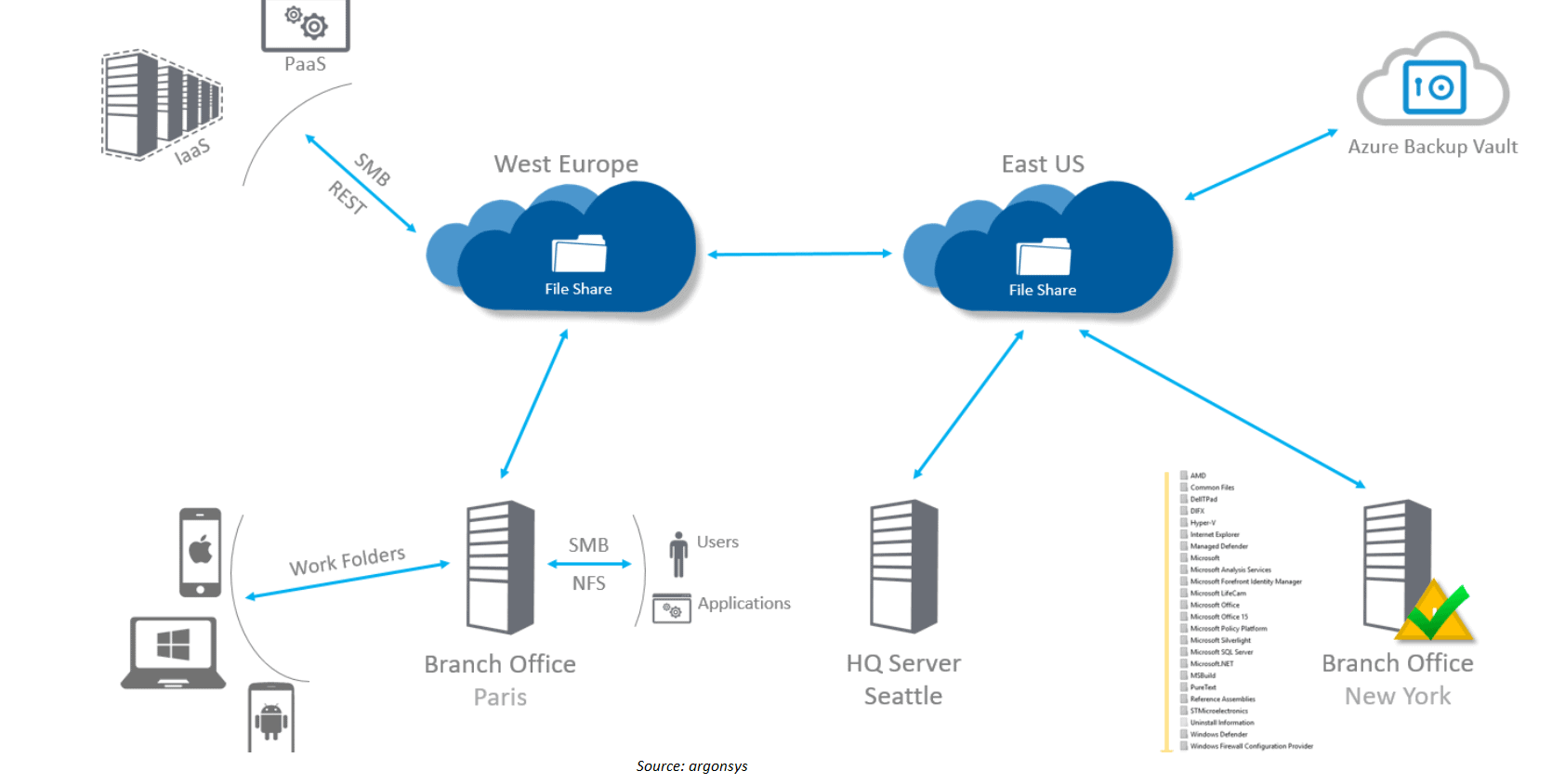
File Sync
With Azure File Sync, shares can be replicated on-premises or on Azure and accessed via SMB or NFS shares on Windows Server.
Azure File Sync is useful in instances when data must be accessed and edited from a location other than an Azure datacenter, such as a branch office. Data can be replicated between different Windows Server endpoints, for example, between branch offices. Windows Server becomes a rapid cache of your Azure file sharing with Azure File Sync. To access your data locally, you can use any protocol supported by Windows Server, including SMB, NFS, and FTPS. You can have as many caches as you want anywhere on the planet.
Azure File Sync enables organizations to:
- Centralize file services in Azure storage
- Cache data in multiple places for fast, local performance
- Eliminate DR and local backup
Q3. Is Azure File Sync compatible with geo-redundant storage?
Ans. Yes, both locally redundant storage (LRS) and geo-redundant storage are supported by Azure Files (GRS). If you failover a storage account across paired regions from a GRS-enabled account, Microsoft suggests treating the new region as a data backup only. The new primary region is not automatically synced by Azure File Sync.
Azure Storage Access
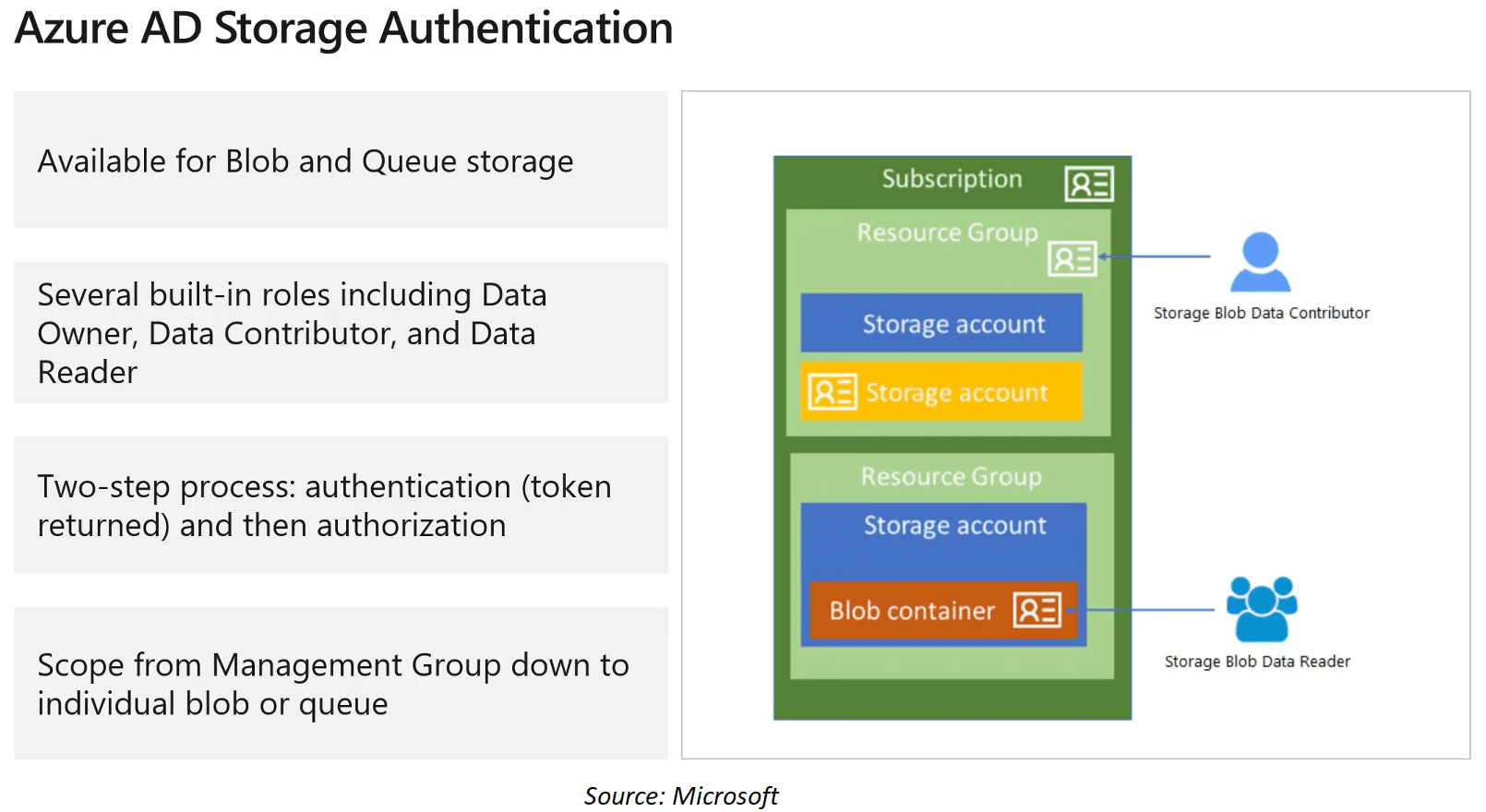
Every request made against the secure resources must be authorized. The authorization ensures that the resources in your storage account are accessed only when you want them to be accessed and only by trusted apps or users, as it may contain data like credit card information.
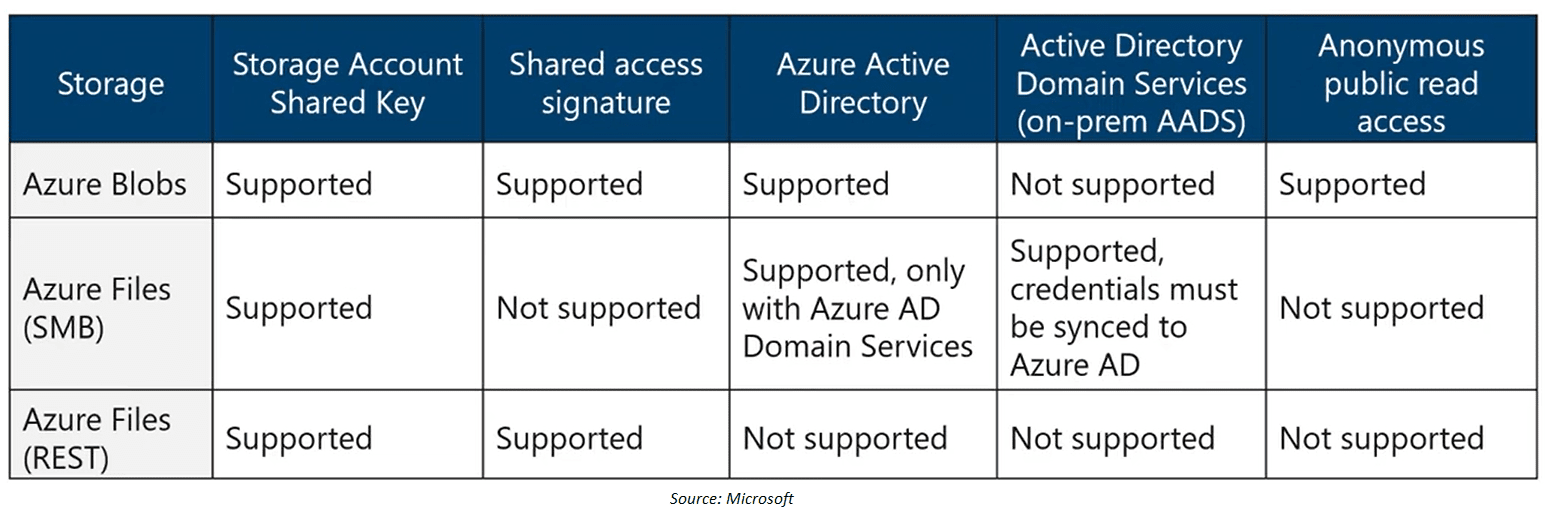
We have different options for authorizing access to Azure Storage, for example, Azure AD. Azure Storage provides integration with Azure AD for identity-based authorization of requests to the blob and queue services. A brief picture of which authentication method is supported by which storage type is given below:
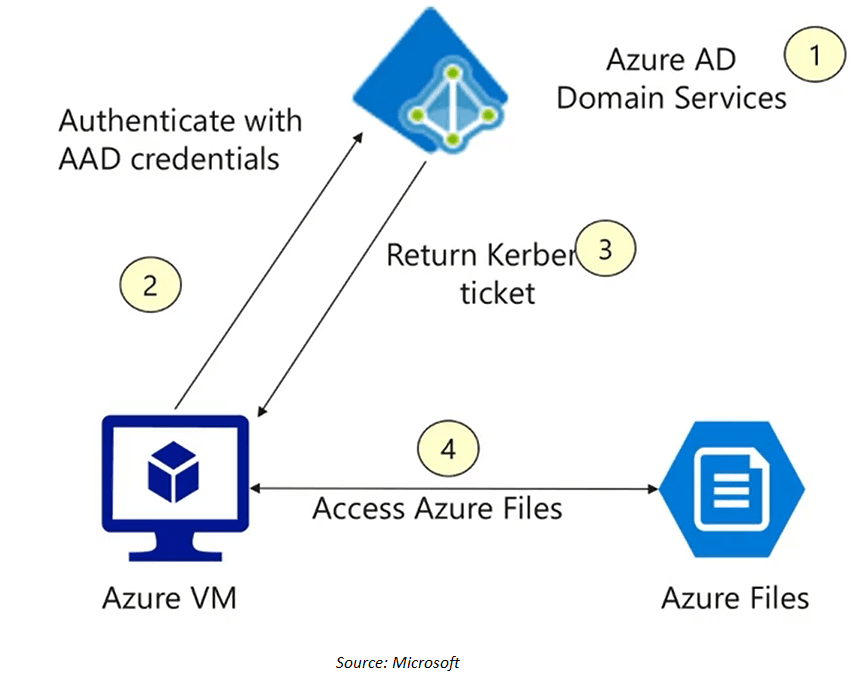
Q4. Does Azure AD DS or on-premises AD DS authentication for Azure file shares support Linux VMs?
Ans. No, authentication from Linux VMs is not supported.
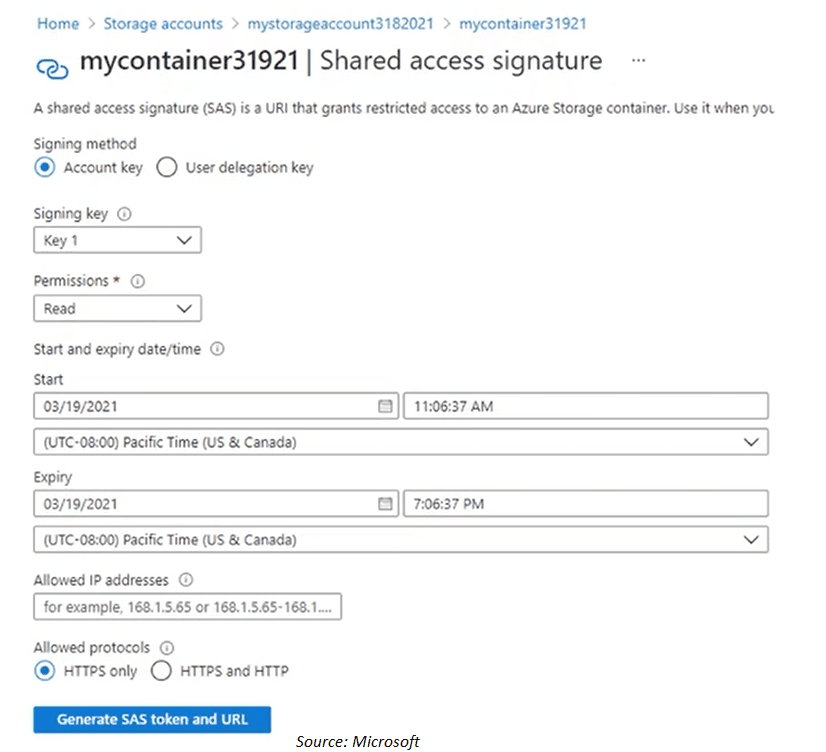
Shared Access Signature
As a best practice, you should not share the storage account keys with third-party app or users outside your organization. Because the storage account key is like a master key. So for these kinds of clients, we use a shared access signature.
A shared access signature is a string that contains the security token that can be attached to the URI. By using a shared access signature you don’t have to worry about sharing the key.
Q5. How can I provide access to a specific file by using a web browser?
Ans. You can use shared access signatures to generate tokens that have specific permissions, and which are valid for a specified time interval.
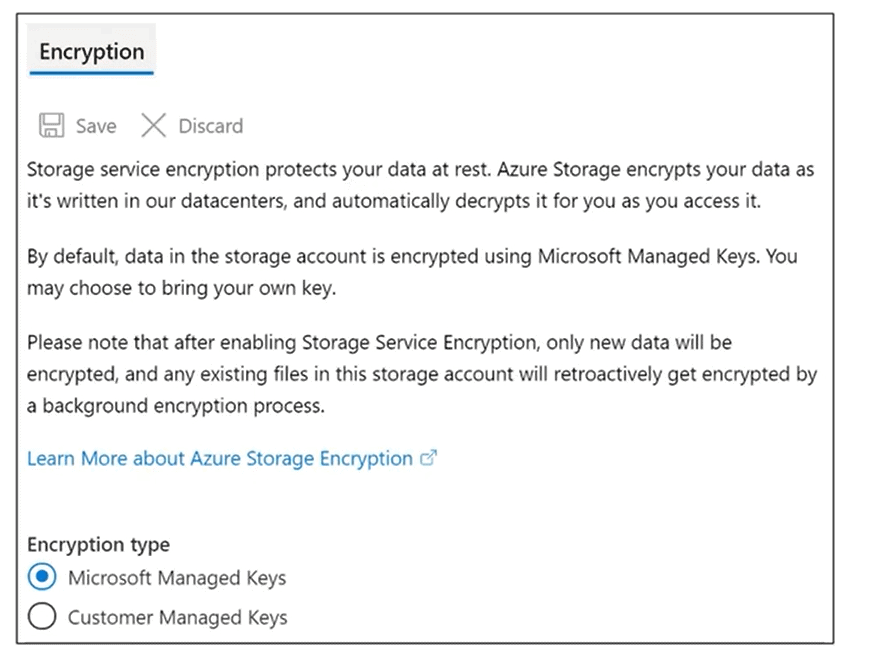
Storage Service Encryption
When your data is saved to Azure Storage, it is immediately encrypted using server-side encryption (SSE). Azure Storage encryption safeguards your data while also assisting you in meeting your organization’s security and regulatory goals.
All storage accounts, including Resource Manager and conventional storage accounts, have Azure Storage encryption enabled. Encryption in Azure Storage cannot be turned off. You don’t need to change your code or applications to use Azure Storage encryption because your data is secured by default.
Blob Data Retention Policy
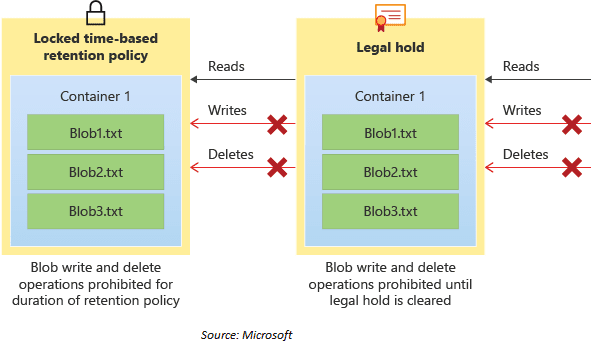
Immutable storage for Azure Blob Storage enables users to store business-critical data in a WORM (Write Once, Read Many) states. For a user-specified interval, data cannot be updated or destroyed while in a WORM state. By configuring immutability policies for blob data, you can protect your data from overwrites and deletes.
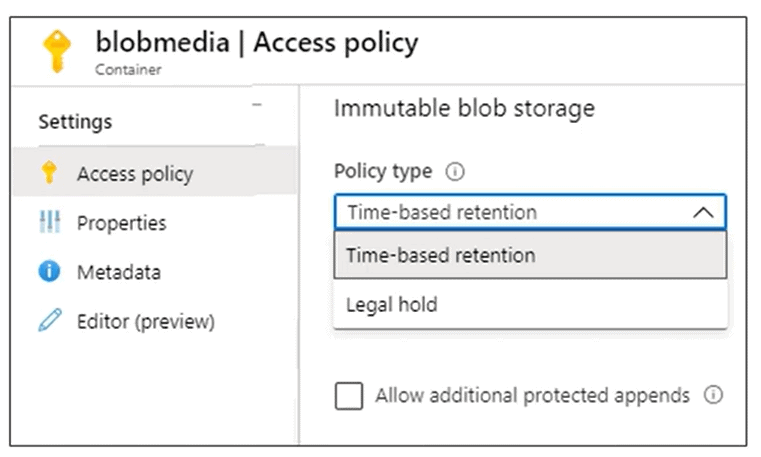
Immutable storage for Azure Blob storage holds two types of immutability policies:
- Time-based retention policies: Users can set policies to store data for a specified interval with a time-based retention policy. When a time-based retention policy is set, objects can be created and read but not modified or deleted. After the retention period has expired, objects can be deleted but not overwritten.
- Legal hold policies: A legal hold stores immutable data until the legal hold is explicitly cleared. Objects can be created and read when a legal hold is set, but not modified or deleted.
Azure Files Authentication
Azure Files supports identity-based authentication over Server Message Block (SMB) through on-premises Active Directory Domain Services (AD DS) and Azure Active Directory Domain Services (Azure AD DS).
When you enable identity-based access for your Azure file shares, you may replace current file servers with Azure file shares without having to replace your existing directory service, ensuring that users have seamless access to the shares.
User access to both the share and the directory/file levels is controlled by Azure Files. The Azure role-based access control (Azure RBAC) architecture can be used to assign share-level permissions to Azure Active Directory (Azure AD) users or groups. The credentials you use for file access should be available or synced to Azure AD if you’re using RBAC. To grant read access to an Azure file share, you can assign Azure built-in roles like Storage File Data SMB Share Reader to users or groups in Azure AD.
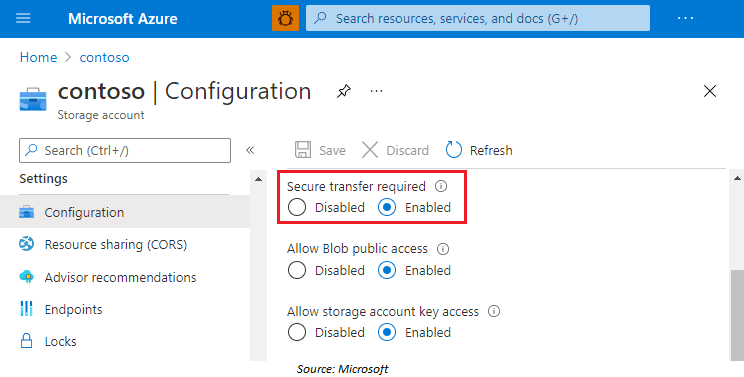
Secure Transfer Required
Only the Secure transfer required property for the storage account can be used to configure your storage account to allow requests from secure connections. When the secure transfer is required, any requests coming from an unsecured connection are rejected. Microsoft advises having secure transfers for all of your storage accounts.
A call to an Azure Storage REST API action must be conducted over HTTPS when a secure transmission is required. Any HTTP request will be denied. When you create a storage account, the Secure transfer required property is activated by default.
>Know more about Secure Transfer
Quiz Time (Sample Exam Questions)!
Ques: Which of the following Azure cloud services offers serverless capabilities?
- A. Azure Functions
- B. Azure App Service
- C. Azure Kubernetes Service (AKS)
- D. All of the above
Developers can use multiple Azure services to build and maintain applications without having to manage infrastructure. Azure Functions is the platform’s serverless computing offering that executes code in response to events. Azure App Service provides a serverless application environment where developers can build and run mobile and web applications. AKS offers serverless Kubernetes container management.
Feedback
Related/References
- Visit our Youtube channel to know more
- [Recap] Day 6: Implement Platform Protection In Cloud Part – III
- [Recap] Day 5: Implement Platform Protection In Cloud Part – II
- Microsoft Azure Security Technologies: Step By Step Activity Guides
- Microsoft Azure Security Technologies Certification
- Azure Security Center [AZ-500]: Everything You Should Know
Next Task For You
To get more clarity on what to expect in the training program, I recommend you to attend the FREE Class I’m holding this weekend! This FREE class will help you to understand what the training program looks like and give will you a clear vision to plan your career ahead!
Join me in the FREE Session and fast track your success!
Click on the below image and Register for our FREE CLASS Now!



Leave a Reply