AWS Solution Architecture Associate is the comprehensive Training for those who run enterprise architecture programs, as well as solutions architects or Beginners who want to learn AWS Solution Architecture Associate covering Identity Access Management (IAM), Amazon Simple Storage Service (S3), Serverless Websites, Autoscaling & Load Balancing, etc. If you are new to AWS, then I would recommend you to check our blog on AWS Solution Architecture and Its Roles and Responsibilities.
This blog will cover the FAQs of AWS Solution Architect Associate Training covering Module 1 (Lab): Create Cloud Account, Machine and Install CLI, and Module 2: Security Management AWS. This blog will help you to clear your concepts with AWS Solution Architect.
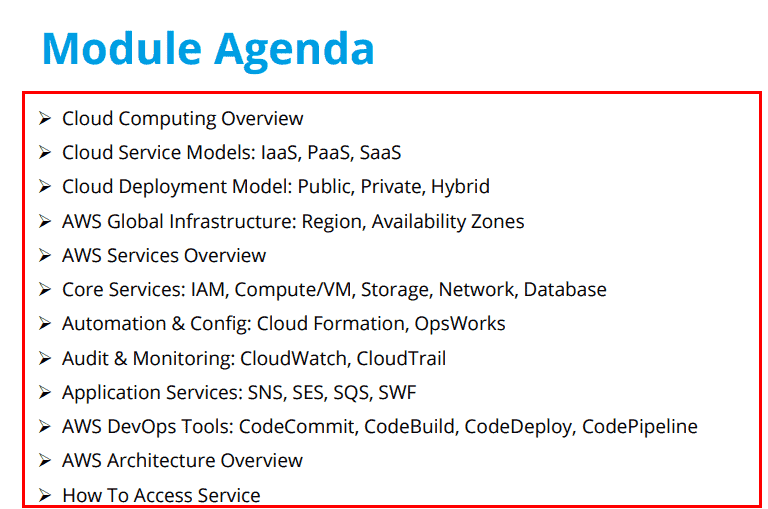
On Day 2 we covered the following topics in Module 1 (Lab):
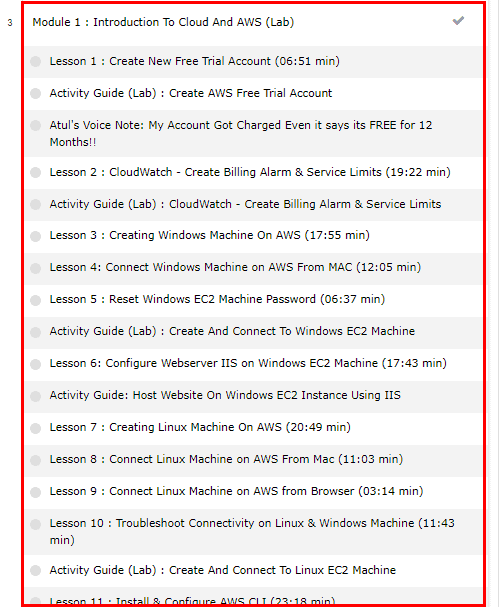
Q/A Related to Module 1 (Lab): Create a cloud Account, Machine, and Install CLI
Q1. Is the AWS account free or not?
Ans. The AWS Free Tier account makes certain amounts and types of resources for new AWS accounts available free of charge for a 1 year period in limited usage of resources. To avoid unnecessary charges delete/clean up the resources when you’re done using them.
Q2. What is CloudTrail in AWS?
Ans. The AWS CloudTrail is a service that enables auditing, compliance, operational, governance, and risk auditing of your AWS account. CloudTrail provides the event history of your AWS account activity, including actions taken through the AWS Management Console, AWS CLI, AWS SDK, and other AWS services.
Check Out: What is AWS X-Ray?
Q3. Is CloudWatch a Free Service?
Ans. You can get started with Amazon CloudWatch for free. Most AWS Services (S3, EC2, Kinesis, etc.) vend metrics automatically for free to CloudWatch. Many applications should be able to operate within these free tier limits.
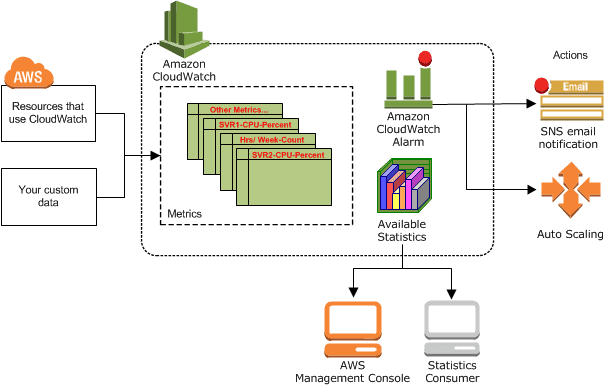
Q4. What types of monitoring can AWS CloudWatch be used for?
Ans. CloudWatch is a monitoring service for resources and the applications you run on AWS. You can use CloudWatch to track and collect metrics, collect and monitor log files, and set alarms.
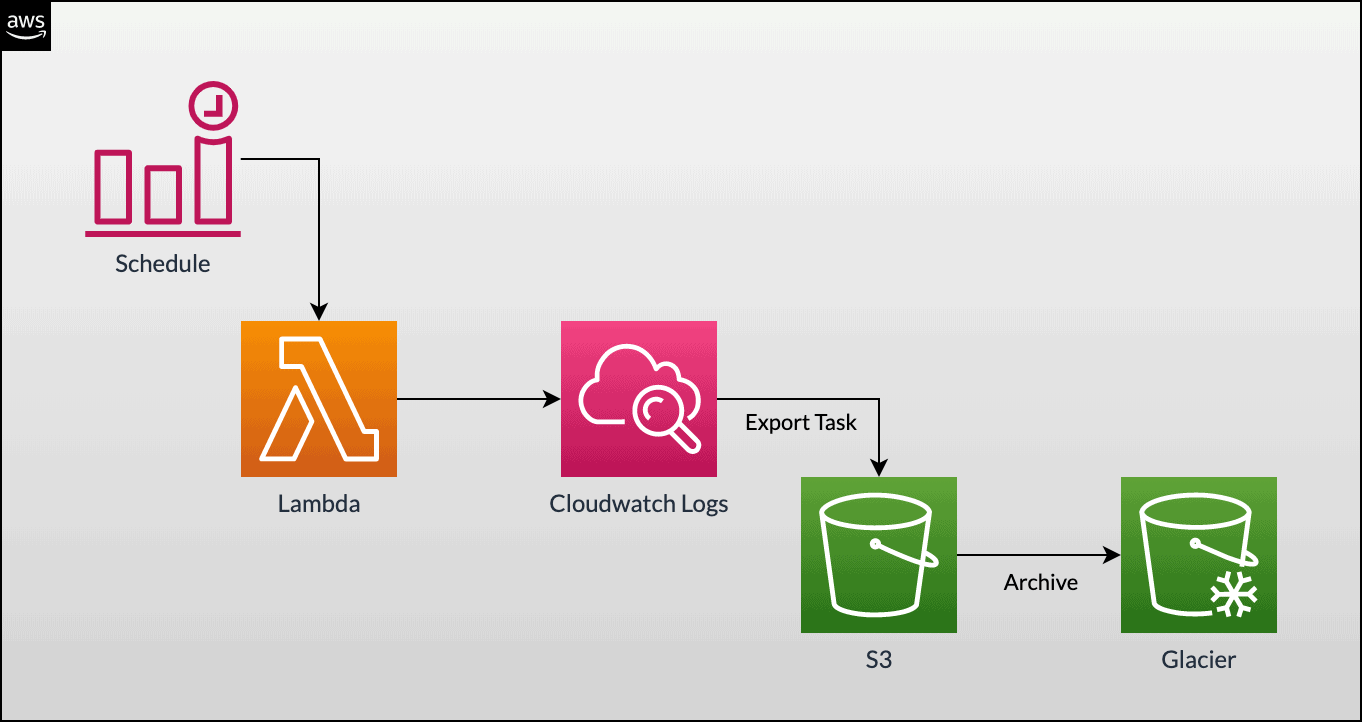
Q5. Are CloudWatch logs stored in S3?
Ans. Choose Save to set the policy that you just added as the access policy on your bucket. This policy enables AWS CloudWatch Logs to export log data to your Amazon S3 bucket.
Q6. Why does AWS have service limits?
Ans. AWS maintains the service quotas (service limits) for each account to help guarantee the availability of AWS resources and prevent the accidental provisioning of more resources than needed. Some service quotas are raised automatically over time as you use AWS.
Q7. How can I increase the AWS service limits?
Ans. You have to open the AWS Support Center page, sign in to your account if necessary, choose to Create a case, Choose Service limit increase, and complete and submit the form.
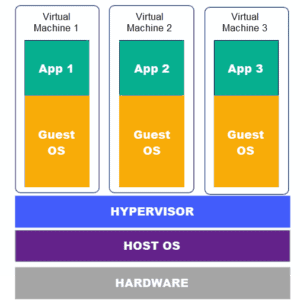
Q8. What is a virtual machine?
Ans. Amazon Elastic Compute Cloud is the service that use to create and run virtual machines (VM), also known as instances.
Q9. What is Amazon EC2 Instance?
Ans. Amazon Elastic Compute Cloud (Amazon EC2) is a web service that provides secure, resizable, and compute capacity in the cloud. The EC2 is designed to make web-scale cloud computing easier for developers.
Also Read: Our blog post on AWS Cloud Storage.
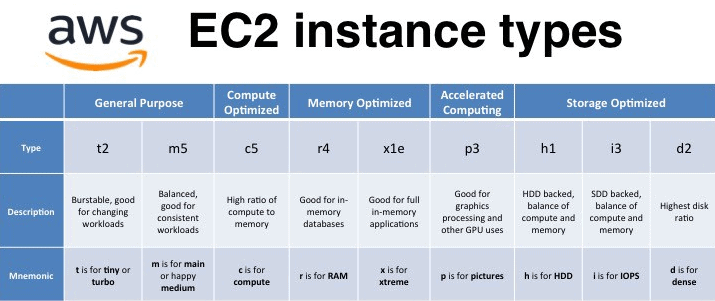
Q10. What is the EC2 instance type?
Ans. Amazon EC2 provides a wide selection of instance types optimized to fit different use cases. The EC2 Instance types comprise varying combinations of memory, CPU, storage, and networking capacity and give you the flexibility to choose the appropriate mix of resources for your applications.
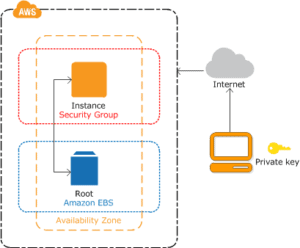
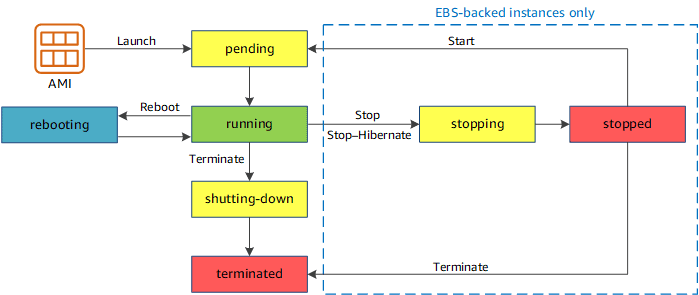
Q11. What is the difference between stopping and terminating ec2 instances on AWS?
Ans. The key difference between stopping and terminating an instance is that the attached bootable EBS volume will not be deleted. The data on your EBS volume will remain after stopping while all information on the local (ephemeral) hard drive will be lost as usual.
Q12. What is the AWS CLI?
Ans. The AWS Command Line Interface is an AWS tool that enables developers to control Amazon public cloud services by typing commands on a specified line. AWS’s version of a command-line interface is one of several methods a developer can use to create and manage AWS tools.
Q13. Why use AWS CLI?
Ans. AWS CLI gives you the ability to automate the entire process of managing and controlling AWS services through scripts. These scripts make it easy for users to use the fully automated cloud infrastructure.
Q14. Is AWS CLI open source?
Ans. The AWS Command Line Interface (AWS CLI) is an open-source tool that enables you to interact with AWS services using commands in your command-line shell.
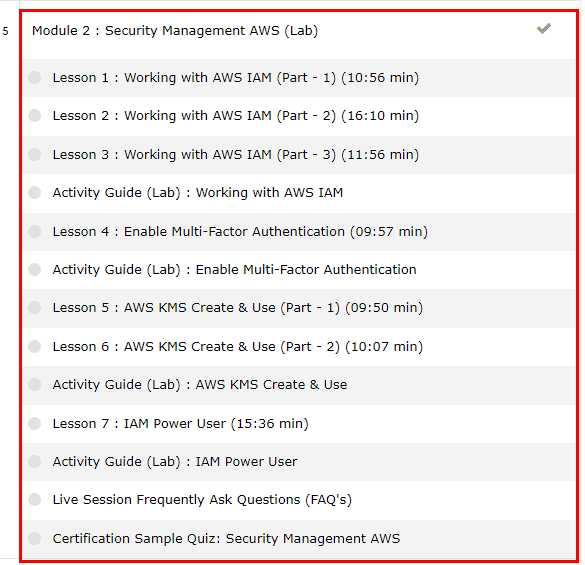
Now let’s analyze Module 2: Security Management AWS which includes the following lessons
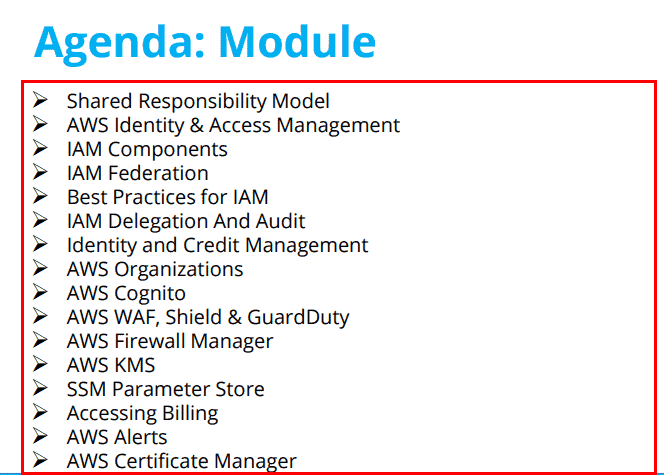
 [Q/A] Related to Security Management AWS
[Q/A] Related to Security Management AWS
Q1. What is the difference between a root user and an IAM user?
Ans. The root users are the users who you have signed up with by providing your card and billing details and logging in via providing your email and password only. IAM user accounts are user accounts that you can create for individual services offered by AWS and they are logged in by providing the Account Id, username, and password. The IAM users are created under the root account only.
Q2. How many IAM roles can I create?
Ans. You are limited to 1,000 IAM roles under your AWS account. If you need more roles, then you have to submit the IAM limit increase request form with your use case to AWS.
Q3. IAM is a free service or paid service?
Ans. IAM roles are free of charge, You will only pay for the resources that the IAM role in your AWS account will consume.
Q4. What are IAM policies?
Ans. IAM policies define permissions for action regardless of the method that you use to perform the operation. For example, if a policy allows the GetUser action, then a user with that policy can get user information from the AWS Management Console, the AWS API, or the AWS CLI.
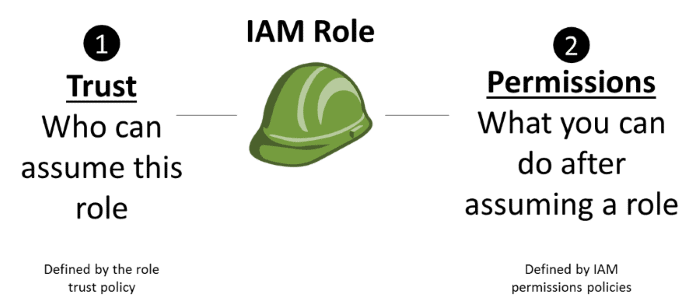
Q5. What are IAM roles?
Ans. An IAM role is an IAM entity that defines a set of permissions for making AWS service requests. The IAM roles are not associated with a specific user or group.
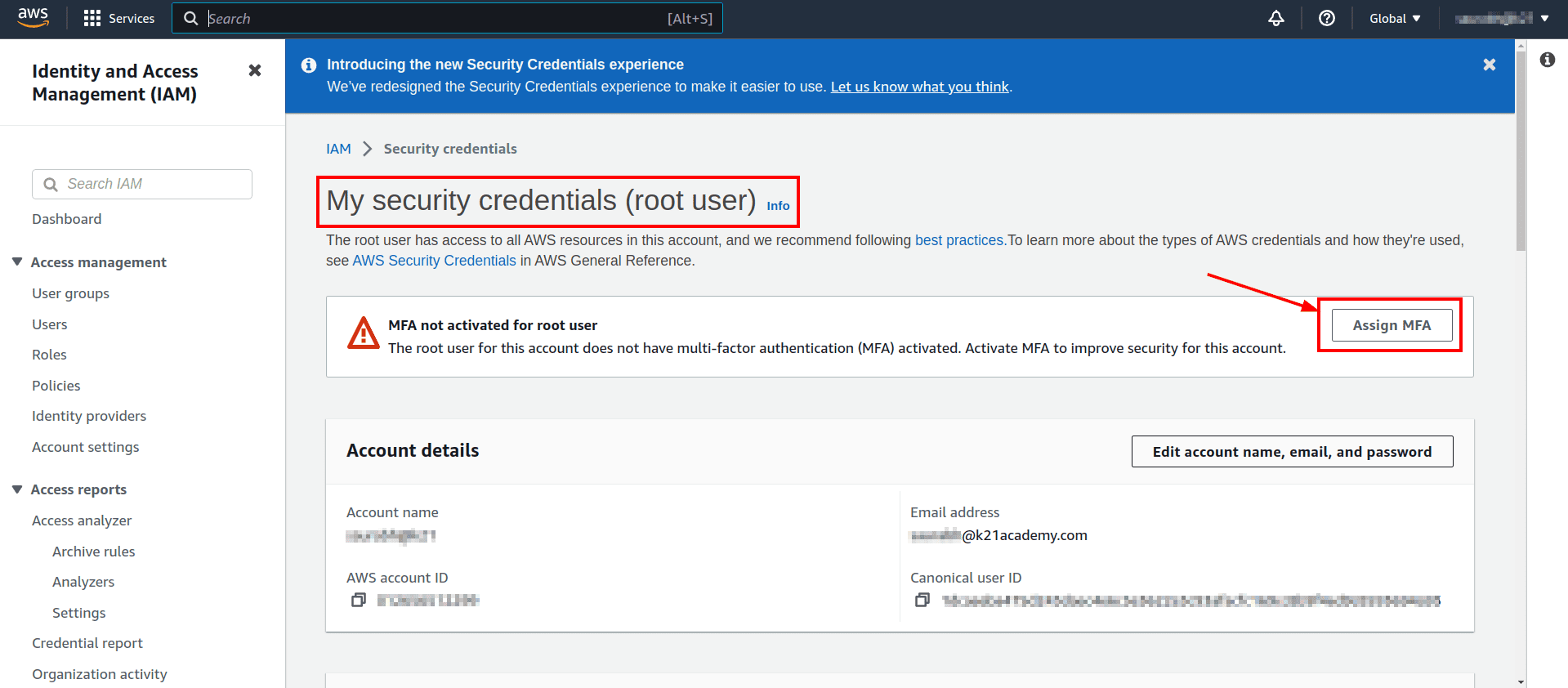
Q6. What is the MFA?
Ans. AWS Multi-Factor Authentication (MFA) is a simple best practice that adds an extra layer of protection on top of your username and password. You can enable MFA for your AWS account and for individual IAM users you have created under your account. MFA can also be used to control access to AWS service APIs.
Q7. Why do we use MFA in our root account?
Ans. Because your root user can perform sensitive operations in your account, adding an additional layer of authentication helps you to better secure your account. MFA is a very secure method of protecting corporate data and networks but combining it with other identity security solutions such as single sign-on (SSO) and least privilege access allows for even better security.
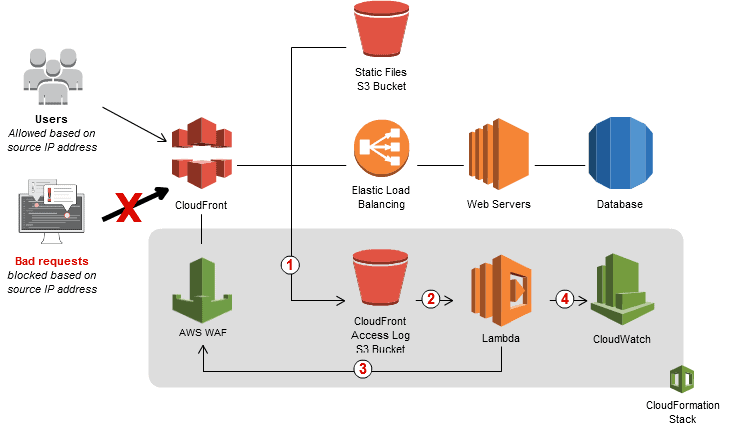
Q8. How does AWS WAF work for users on AWS?
Ans. AWS WAF gives you control over how traffic reaches your applications by enabling you to create security rules that block common attack patterns, such as SQL injection or cross-site scripting, and rules that filter out specific traffic patterns you define. With AWS WAF, you pay only for what you use.
Q9. How AWS WAF is different from GuardDuty?
Ans. Amazon GuardDuty sends notifications based on Amazon CloudWatch Events when any change in the findings takes place. AWS WAF is a web application firewall that helps protect your web applications from common web exploits that could affect application availability, compromise security, or consume excessive resources.
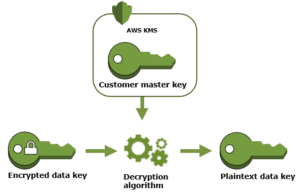
Q10. What is the use of KMS?
Ans. The Key Management Service is a managed service used to store and generate encryption keys that can be used by other AWS services and applications to encrypt your data. For example, S3 may use the KMS service to enable S3 to offer and perform server-side encryption using KMS-generated keys known as SSE-KMS.
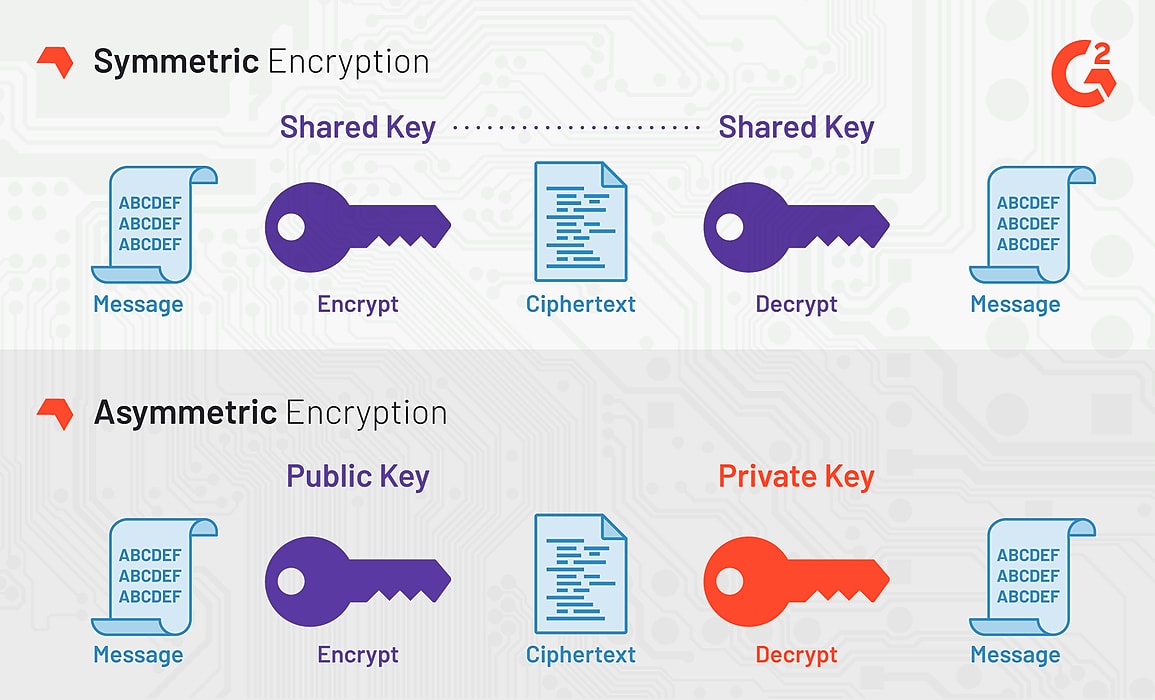
Q11. What is the difference between symmetric and asymmetric key KMS on AWS?
Ans. In a symmetric key, only one key is used, and the same key is used to encrypt and decrypt the message. And in Asymmetric keys, Two different cryptographic keys are used for encryption, called the public and the private keys, which are used for encryption and decryption.
Q12. Do AWS Charge for KMS keys?
Ans. There is no commitment and no upfront charges to use AWS KMS. You only pay $1/month to store any key that you create. AWS-managed keys that are created on your behalf by AWS services are free to store. You are charged per request when you use or manage your keys beyond the free tier.
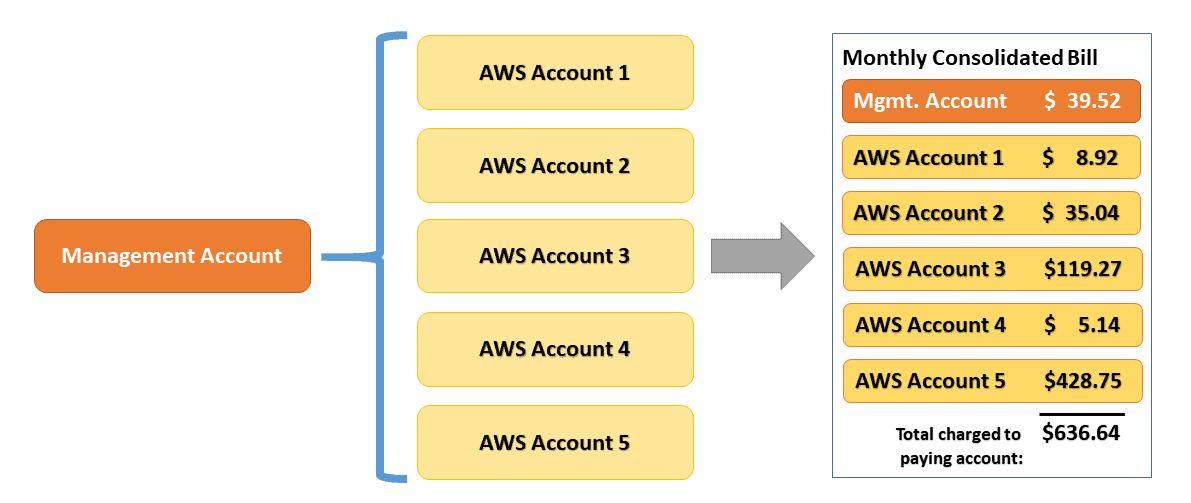
Q13. How does AWS Billing work?
Ans. AWS Billing and Cost Management is the service that you use to pay your AWS bill, monitor your usage, and analyze and control your costs.
Q14. What is an alarm in AWS?
Ans. Alarms watch metrics and execute actions by publishing notifications to Amazon SNS topics or by initiating Auto Scaling actions. SNS can deliver notifications using HTTP, HTTPS, Email, or an Amazon SQS queue. Your application can receive these notifications and then act on them in any desired way.
Q15. Are AWS billing alerts free?
Ans. AWS sends AWS Free Tier usage alerts to the email address that you used when you created your account. You can change the email address on the Billing and Cost Management console.
Related Links/References
- AWS Solution Architect Questions Day 1: Introduction To Cloud & AWS
- AWS Certified Solutions Architect Associate SAA-C03 Exam details
- AWS Free Tier: Create an Account
- AWS SAA C03 Exam Guide
- AWS SAA C03 Sample Questions
- AWS Virtual Private Network (AWS VPN): Everything You need to Know
- AWS Fargate: Everything You Need To Know About
Next Task For You
Begin your journey towards an AWS Cloud by joining our FREE Informative Class on Amazon Cloud Free Class by clicking on the below image.

 [Q/A] Related to Security Management AWS
[Q/A] Related to Security Management AWS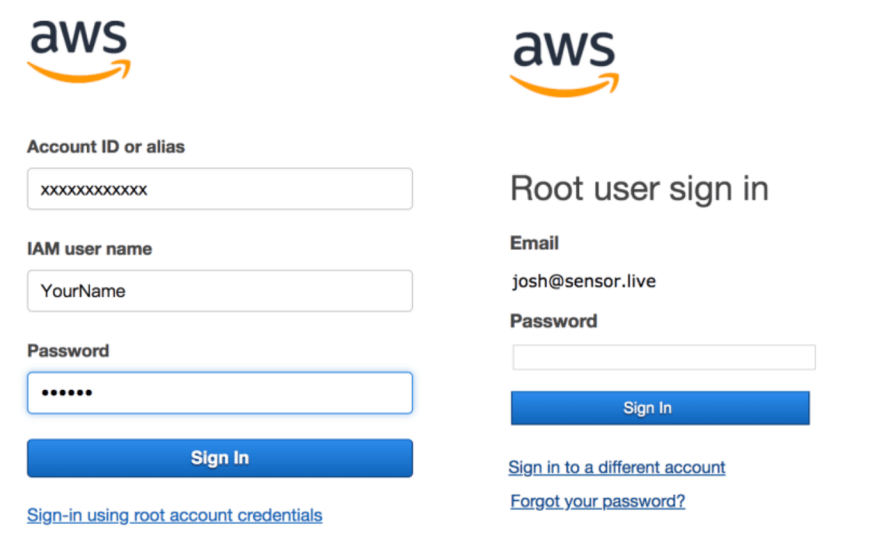




Leave a Reply